XLoader’s latest update makes analysis harder by hiding real command servers among decoys

XLoader is not new, but its latest versions are becoming much harder to study and block. Zscaler ThreatLabz says recent XLoader builds, from version 8.1 through 8.7, add heavier code obfuscation and a command-and-control design that hides real servers among decoys.
The malware still focuses on what made it dangerous in the first place. It steals credentials from browsers, email clients, and FTP applications, and it can also receive commands to run additional malware or execute actions on infected systems. Zscaler says that core behavior remains active in the latest versions.
What changed is the way XLoader protects its inner workings. ThreatLabz says the newer builds do a better job hiding strings, code, and network logic, which makes reverse engineering slower and makes automated sandboxes less reliable when they try to separate fake infrastructure from real command servers.
How the new decoy server system works
According to Zscaler, XLoader stores 65 command-and-control IP addresses in the malware, but it does not expose them all in a readable form up front. Each one is decrypted only when the malware is about to use it.
When the malware starts a communication cycle, it randomly selects 16 of those 65 addresses and begins sending requests across them. ThreatLabz says it sends both data upload requests and command retrieval requests through this pool, which makes it difficult for defenders to tell which servers are real and which ones are just noise.
That design gives the attackers an obvious advantage. A sandbox may see traffic to many IPs, but without live interaction and response validation, it may not identify the actual malicious endpoint. That is the main reason researchers describe the new approach as a meaningful evasion upgrade rather than a minor protocol tweak.
What changed in XLoader’s obfuscation
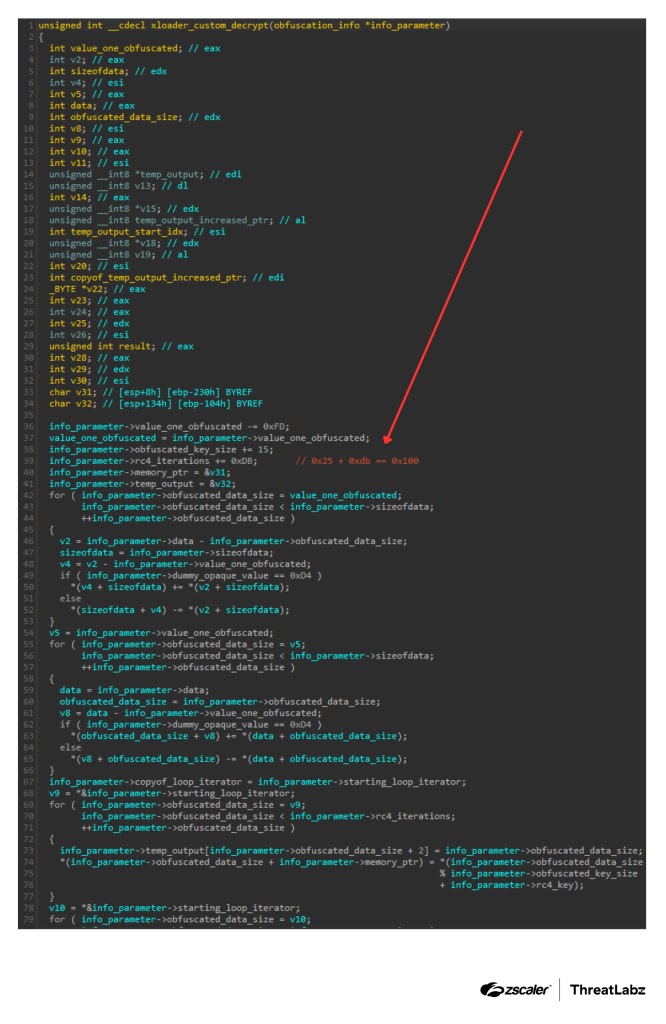
Zscaler says version 8.1 marked a turning point in the malware’s obfuscation methods. From that version onward, XLoader introduced a more complex custom decryption routine that made it harder to recover protected code and strings during static analysis.
The malware also continues to wrap its network traffic in several layers of protection. ThreatLabz says the traffic still moves over HTTP, but the malware uses additional encryption and hashing steps internally, which means defenders cannot rely on plain packet inspection alone to understand the contents of the traffic.
Your sample is mostly accurate here, but I would tighten one line. Saying the traffic is “practically impossible” to decode overstates the point. A better wording is that decoding the traffic without the proper keys and runtime context is difficult and slows analysis significantly.
Why this still matters
XLoader remains an active information stealer with broader backdoor-like capabilities. Zscaler says it can steal stored credentials and also support follow-on activity, including second-stage payload delivery. That keeps it relevant for both crimeware campaigns and access-brokering operations.
The latest version highlighted by ThreatLabz is 8.7. That detail matters because it shows active development is still underway, not just minor repackaging of an old malware family.
The infection vectors have not changed much. XLoader still commonly arrives through phishing emails and malicious attachments, which means the malware’s delivery remains simple even as its internal design becomes harder to inspect.
Key details at a glance
| Item | Details |
|---|---|
| Malware family | XLoader |
| Most recent version cited by Zscaler | 8.7 |
| Major obfuscation shift started in | 8.1 |
| Embedded C2 IPs | 65 |
| Randomly selected per cycle | 16 |
| Transport | HTTP with layered internal encryption |
| Main focus | Credential theft, command execution, second-stage delivery |
What defenders should watch for
Security teams should look for short bursts of HTTP requests sent across multiple IP addresses in a way that does not match normal application behavior. ThreatLabz also points to Base64-encoded parameters with random-looking names as a useful hunting clue.
Zscaler says network emulation remains one of the best ways to tell real command servers from decoys. That is important because static analysis of the sample alone may no longer be enough to map the true control infrastructure.
Endpoint tools also still matter. Your sample mentions detection under Win32.PWS.XLoader, but I would avoid presenting that as a universal vendor label. Detection names vary by security product, so it is safer to frame it as one detection family rather than a definitive industry-wide name.
Quick takeaways
- XLoader versions 8.1 through 8.7 add stronger obfuscation and better C2 concealment.
- The malware hides real command servers behind a larger set of decoy IP addresses.
- It randomly chooses 16 servers from a pool of 65 during communication cycles.
- It still steals credentials and can help deliver second-stage malware.
- Sandboxes and static analysis tools now have a harder time separating fake infrastructure from real C2.
FAQ
Zscaler says the major changes involve heavier code obfuscation and a decoy-based command server design that makes analysis harder.
ThreatLabz says the latest observed version is 8.7.
Yes. Zscaler says it targets browsers, email clients, and FTP applications for credential theft and can also receive commands from its operators.
They make it harder for sandboxes and defenders to identify the real command servers because the malware sends traffic across a wider pool of addresses.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages