EvilTokens turns Microsoft’s device code flow into a phishing tool for account takeover

A new phishing-as-a-service platform called EvilTokens is helping cybercriminals hijack Microsoft 365 accounts by abusing Microsoft’s legitimate device code authentication flow. Sekoia says the kit began circulating in phishing-focused underground communities in early March 2026 and stands out because it does not need a fake Microsoft login page to steal credentials in the usual way.
Instead, EvilTokens tricks victims into entering a real Microsoft device code on Microsoft’s own sign-in page. That authorizes the attacker’s device, not the victim’s, and can hand over valid access and refresh tokens that give the operator direct access to Microsoft 365 resources. Sekoia describes it as the first known turnkey PhaaS kit built around Microsoft device code phishing.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The platform appears built for scale. Sekoia says EvilTokens uses Telegram bots, phishing page templates, email harvesting features, webmail access, reconnaissance modules, and AI-assisted automation to support affiliates running account takeover campaigns. The operator has also advertised future support for Gmail and Okta phishing pages.
How the EvilTokens attack works
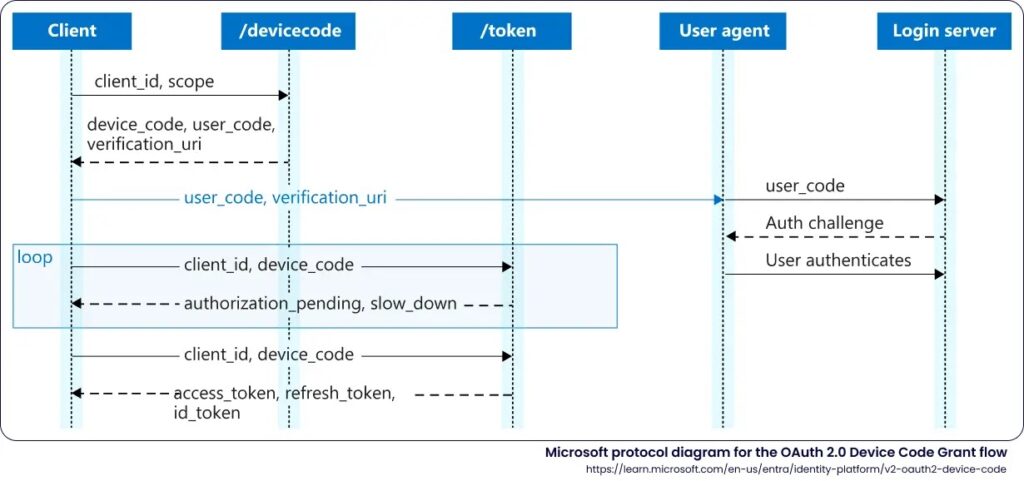
The attack abuses Microsoft’s OAuth 2.0 Device Authorization Grant, which is meant for devices that have limited input options such as TVs, printers, meeting-room systems, or other hardware that cannot easily handle a full login flow. Microsoft describes device code flow as a high-risk authentication method that can be abused in phishing attacks and recommends blocking it wherever possible unless it is truly needed.
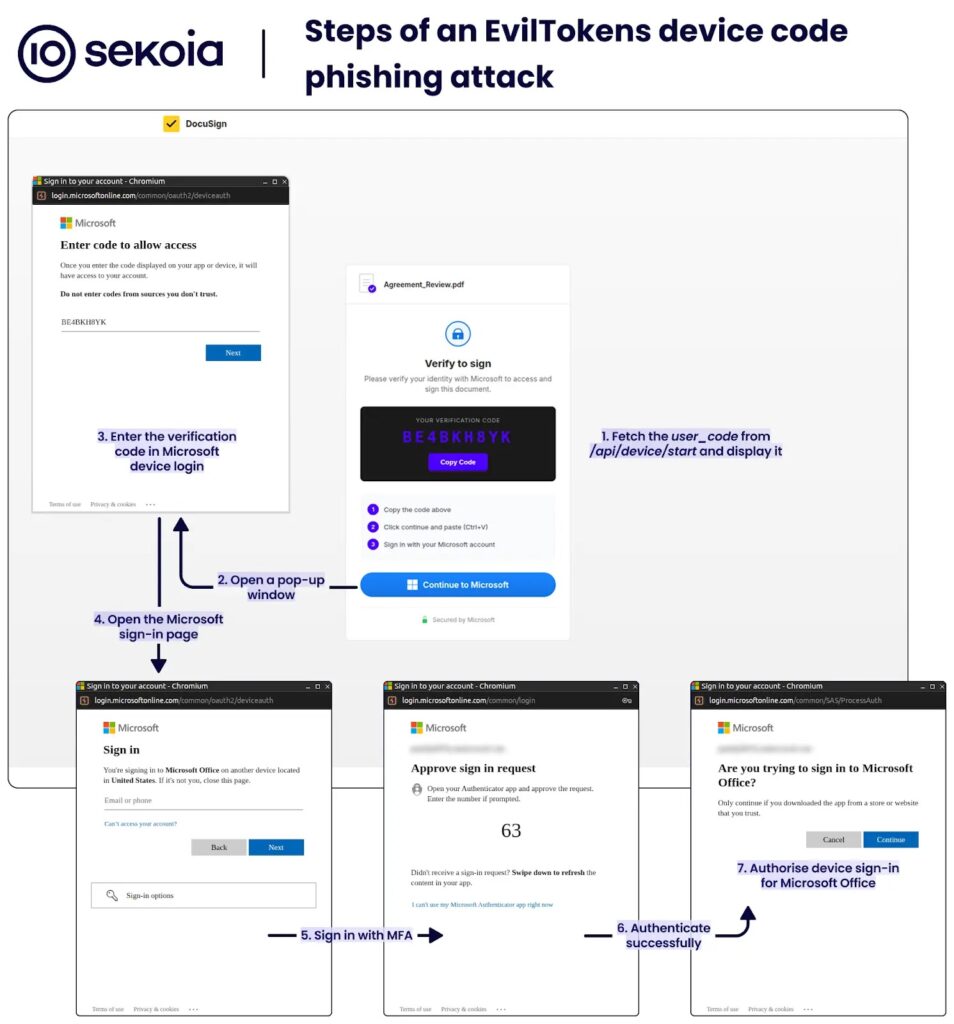
In a normal scenario, a device displays a short code and the user enters it on a separate Microsoft sign-in page to authorize that device. EvilTokens flips that process by generating the code on the attacker side and then sending it to the victim through phishing lures that pretend to be shared documents, invoices, meeting invites, or cloud collaboration links. When the victim enters the code on Microsoft’s real page, the attacker’s device receives the resulting tokens.
That makes the attack especially dangerous for organizations that rely heavily on Microsoft 365. Once access is granted, the operator can use the account to read mail, access OneDrive and SharePoint content, and review Teams messages, all without collecting the victim’s password in the traditional sense. Microsoft has already warned that threat actors use device code phishing in real-world campaigns and specifically recommends limiting or blocking the flow where possible.
Why the token theft matters
Microsoft says access tokens in Entra ID typically last around 60 to 90 minutes, while refresh tokens generally last 90 days for most non-SPA scenarios and renew themselves when used. That means a single successful device code phish can give attackers long-lasting access even after the initial sign-in window closes.
Sekoia says EvilTokens can also move beyond simple token theft in more advanced cases by converting stolen tokens into broader persistent access. Microsoft documents that a Primary Refresh Token can request access tokens for many resources and is renewable, which makes it especially valuable when attackers manage to obtain it or pivot toward it.
This is one reason device code phishing has become so attractive for business email compromise operations. The attacker does not need to defeat the victim’s password habits in the usual way. The victim authorizes the malicious session themselves on a real Microsoft page, which makes the activity look much more legitimate than a fake credential-harvesting site.
Global reach and targeting
Sekoia says EvilTokens-linked campaigns have already hit organizations across North America, South America, Europe, the Middle East, Asia, and Oceania. The researchers specifically call out strong activity against targets in the United States, Australia, Canada, France, India, Switzerland, and the United Arab Emirates.
The lure strategy reflects classic BEC targeting. EvilTokens affiliates focus on roles such as finance, HR, logistics, and sales, which often have access to invoices, payments, payroll, contracts, and sensitive communications. Sekoia says researchers identified more than 1,000 domains hosting EvilTokens phishing pages by March 23, 2026.
Those pages reportedly impersonate brands and services such as DocuSign, Adobe Acrobat Sign, OneDrive, and SharePoint. Sekoia also says the pages use encrypted content and dynamic rendering techniques to make automated analysis harder and keep the phishing infrastructure flexible across many lures.
Why defenders need to treat device code flow as a major risk
Microsoft’s own guidance now treats device code flow as a high-risk authentication method. The company says organizations should get as close as possible to a unilateral block on device code flow and only allow it in documented, secured scenarios where legacy tooling or special devices truly require it.
That advice lines up directly with what Sekoia found in EvilTokens. If device code flow stays broadly available across an organization, an attacker can turn a legitimate Microsoft sign-in page into the final step of a phishing attack. That gives the campaign a built-in credibility boost and makes user awareness much harder.
Microsoft also offers Conditional Access controls specifically for blocking device code flow. That makes this one of the clearer cases where a platform-level security setting can sharply reduce risk if an organization does not rely on the feature.
| Key detail | What is known |
|---|---|
| Platform name | EvilTokens |
| Model | Phishing-as-a-Service |
| Main target | Microsoft 365 accounts |
| Core technique | Device code phishing |
| First identified by Sekoia | Early March 2026 |
| Reported infrastructure scale | 1,000+ phishing domains by March 23, 2026 |
| Main operator alias | eviltokensadmin |
| Expected future support | Gmail and Okta phishing pages |
- Block device code flow for users who do not need it
- Audit sign-ins that use the device code grant type
- Watch for Microsoft login lures tied to shared docs, invoices, payroll, or meeting requests
- Train users that entering a Microsoft device code authorizes a device, not a document
- Review Conditional Access templates that block high-risk authentication flows
- Investigate consent grants and unusual token-based access quickly
FAQ
EvilTokens is a phishing-as-a-service platform that helps criminals hijack Microsoft 365 accounts by abusing Microsoft’s device code authentication flow. Sekoia says it began circulating in underground communities in early March 2026.
It generates a device code on the attacker side, lures the victim into entering that code on Microsoft’s real sign-in page, and then receives tokens that authorize the attacker’s session.
Not in the usual way. The victim often ends up on a real Microsoft page to enter the device code, which makes the phishing flow more convincing and harder to spot.
Microsoft says device code flow is a high-risk authentication method because it can be used in phishing attacks or to gain access from unmanaged devices.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages