New Akira lookalike ransomware campaign targets Windows users in South America
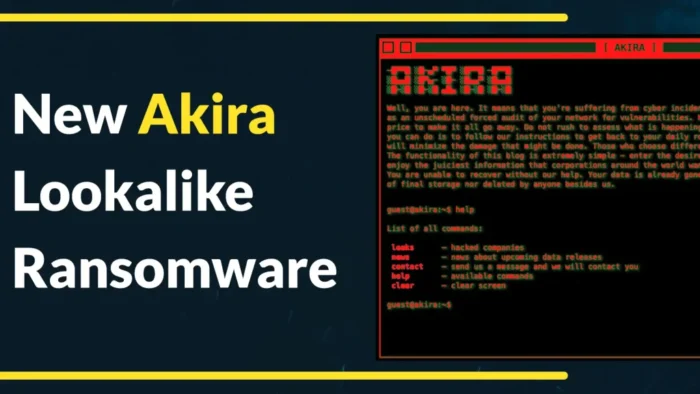
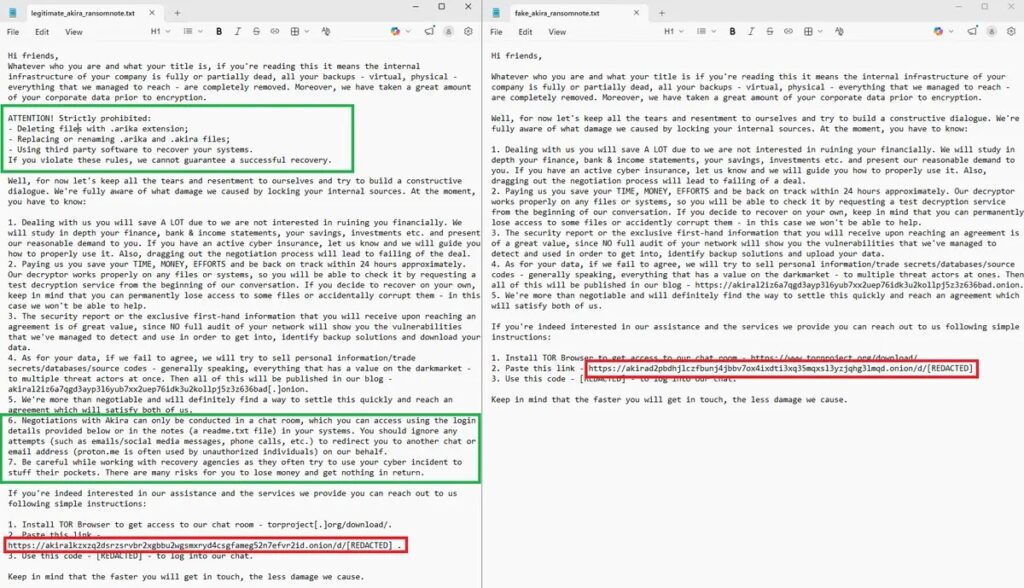
A new ransomware campaign is targeting Windows users in South America by imitating the Akira ransomware brand while relying on a different code base underneath. ESET Research said the threat actor uses a Babuk-based encryptor that adds the .akira extension and drops a ransom note that mimics Akira in both its Tor URLs and overall wording.
That matters because it can mislead victims and delay incident response. A company that sees Akira-style ransom notes may assume the attack came from the real Akira group, even though ESET says this operation only copies the branding and does not use Akira’s original encryptor.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign appears focused on South America, where the operators likely hope to use a familiar ransomware name to pressure victims into paying faster. ESET’s public statement on X identified the threat as an “Akira lookalike ransomware campaign targeting South America.”
Why the campaign stands out
This campaign does not just borrow Akira’s name. It also copies the visual and operational cues that victims and researchers often use to identify a ransomware attack. ESET said the actor appends the .akira extension and uses a ransom note that mirrors Akira’s Tor references and core content.
The technical core is different. According to ESET’s finding, the encryptor is based on Babuk, a ransomware family whose leaked source code has enabled copycat and derivative threats for years. That reuse gives attackers a quicker path to building new strains without writing a fresh encryptor from scratch.
The result is a ransomware operation that looks familiar on the surface but points investigators in the wrong direction if they only check the ransom note and file extension. That makes careful malware analysis more important than ever in ransomware response.
What security teams should take from this
The biggest lesson is simple: do not attribute a ransomware attack based only on branding. File extensions, ransom note wording, and Tor portal references can all be faked. In this case, ESET says the actor borrowed Akira’s identity while using Babuk-based encryption logic underneath.
Defenders should also expect more copycat operations like this. ENISA’s Threat Landscape 2025 notes that Akira remained an active ransomware name in the broader ecosystem, which helps explain why criminals may want to imitate it for intimidation value.
For Windows environments, the practical advice remains the same. Keep systems patched, maintain offline backups, segment networks, and watch for unusual encryption activity or newly created .akira files. Even when the branding is fake, the business impact is real. This defensive guidance aligns with long-standing CISA ransomware recommendations on patching, segmentation, identity protection, and backup hygiene.
Key details at a glance
| Item | Details |
|---|---|
| Campaign type | Akira lookalike ransomware |
| Region named by researchers | South America |
| Target platform | Windows |
| Underlying encryptor | Babuk-based |
| Fake branding used | Akira |
| Encrypted file extension | .akira |
| Ransom note style | Mimics Akira wording and Tor URLs |
| Research source | ESET Research |
What organizations should do now
- Verify ransomware attribution through technical analysis, not ransom note branding alone.
- Hunt for fresh encryption events and sudden appearance of .akira extensions.
- Check backup integrity and recovery speed before an incident happens.
- Limit lateral movement with network segmentation.
- Patch Windows systems and exposed services quickly.
- Review endpoint detections for Babuk-like behavior and suspicious mass file modification.
- Train users and administrators to report unusual file renames or ransom notes immediately.
FAQ
Not based on ESET’s public finding. ESET said the campaign is an Akira lookalike and uses a Babuk-based encryptor rather than Akira’s original ransomware code.
Akira is a recognizable ransomware name. By copying its branding, criminals can create confusion and add pressure on victims who already know the name or have seen coverage of past Akira attacks. This appears to be a brand impersonation tactic.
Watch for unexpected file encryption, the .akira extension, suspicious ransom notes, and system behavior that matches known Babuk-style ransomware activity. Then confirm attribution through deeper analysis instead of assuming the note tells the whole story.
Yes. It shows operators may be broadening their regional targeting or testing campaigns outside the markets that usually get the most ransomware attention. ESET explicitly said the campaign targets South America.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages