New ZAP PTK add-on sends browser security findings straight into ZAP alerts
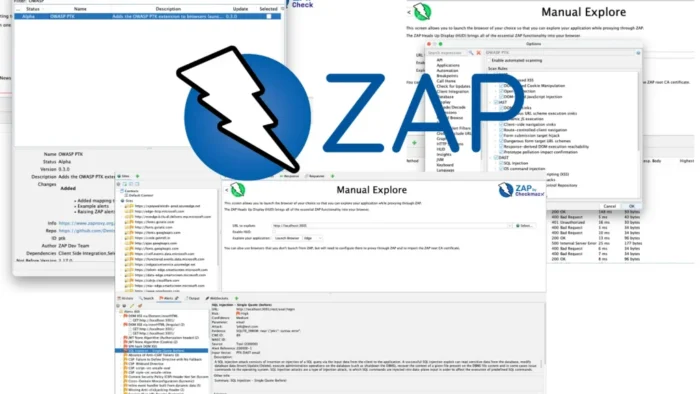
OWASP ZAP has released version 0.3.0 of its OWASP PTK add-on, and the main change is a practical one: findings from the browser can now show up directly as native ZAP alerts. The ZAP team says this works with OWASP PTK 9.8.0 and lets testers review browser-side findings inside ZAP’s normal alert workflow instead of treating them as separate output.
That matters because modern web apps keep more logic in the browser than older apps did. ZAP already sees proxy-layer activity well, but the ZAP team says risks tied to SPA routing, DOM updates, client-side rendering, and JavaScript behavior often happen inside the browser runtime where a proxy alone cannot fully observe them.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The new add-on closes that gap by making PTK findings visible where ZAP users already work. Instead of checking one tool for traffic and another for browser-side issues, security teams can now review both in one interface and use ZAP’s existing alert triage flow.
What changed in ZAP PTK add-on 0.3.0
The ZAP blog says version 0.3.0 keeps the earlier browser integration and adds three notable upgrades. First, PTK findings can now surface as ZAP alerts. Second, users can choose which PTK rule packs to run. Third, teams can enable an auto-start option so PTK scanning begins when a ZAP-launched browser opens.
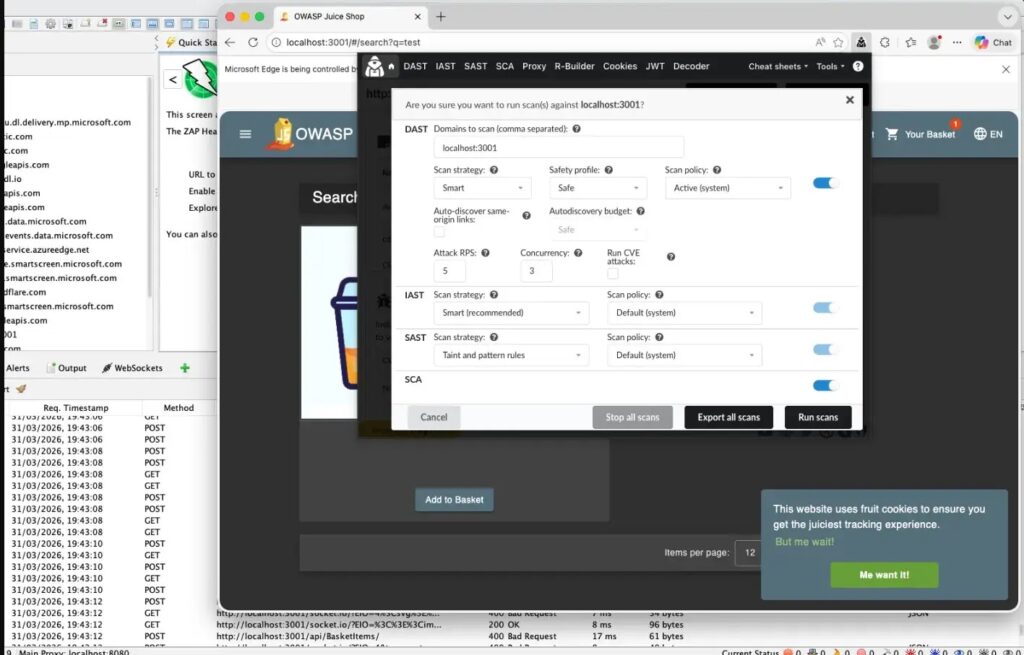
The rule selection piece covers SAST, IAST, and DAST. In the ZAP walkthrough, the team says users can choose which of those PTK rule packs to run before starting a browser session. That gives testers more control over whether they want source-oriented JavaScript findings, runtime browser findings, or browser-driven dynamic testing.
ZAP also continues to pre-install the OWASP PTK extension into Chrome, Firefox, and Edge when those browsers launch from ZAP. That part arrived earlier, but it remains the base workflow that makes the new alert mapping possible.
Why this matters for modern app testing
The release is useful because many important frontend issues do not show up clearly at the proxy layer. The ZAP team specifically points to client-side rendering, SPA navigation, minified JavaScript bundles, and DOM-driven behavior as examples of things that can carry risk without producing obvious server-side clues.
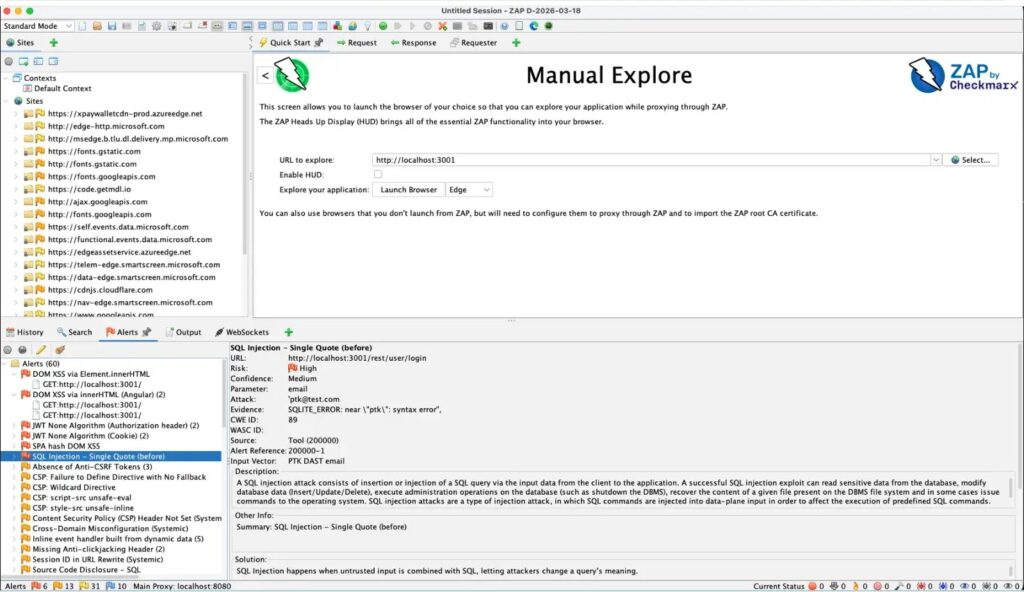
By pushing those findings into native alerts, ZAP lets teams keep their normal workflow. The blog says users can still filter by severity, review alerts in the usual place, and work through findings inside the same central interface instead of splitting client-side results into a separate review queue.
This is especially relevant for JavaScript-heavy applications. PTK runs in the browser context, while ZAP remains the hub for traffic and context. That pairing gives AppSec teams a more realistic view of how the application behaves during real authenticated sessions and UI flows.
What testers can do with it
| Feature | What it does |
|---|---|
| PTK → ZAP Alerts | Sends PTK browser findings into ZAP as native alerts |
| Rule selection | Lets users choose SAST, IAST, and DAST rule packs |
| Auto-start scans | Starts PTK scanning automatically on browser launch if enabled |
| Browser integration | Pre-installs PTK into Chrome, Firefox, and Edge launched from ZAP |
How the workflow looks now
The ZAP team’s walkthrough says users should install or update the OWASP PTK add-on through the ZAP Marketplace, configure PTK scan options, then launch a browser from ZAP into the target app. From there, testers can navigate realistic flows such as login and other user actions while PTK scans in the browser and reports findings back into ZAP.
The same post says this is an early step toward more automation. Future work is expected to include auto-launched browsers, scripted journeys, and more continuous streaming of client-side findings into ZAP.
So the immediate gain is not just more findings. It is a cleaner testing loop where browser-native issues stop living outside the main AppSec workflow.
Quick facts
- ZAP add-on version: 0.3.0.
- PTK version mentioned by ZAP: 9.8.0.
- Supported ZAP-launched browsers: Chrome, Firefox, Edge.
- New core workflow: browser findings appear as native ZAP alerts.
- Selectable scan rule packs: SAST, IAST, DAST.
FAQ
The biggest change is that OWASP PTK findings can now appear directly as ZAP alerts. The release also adds selectable rule packs and an optional auto-start scan setting for ZAP-launched browsers.
Yes. The add-on still installs the PTK extension automatically in Chrome, Firefox, and Edge when those browsers launch from ZAP.
Because many risks in modern apps happen inside the browser runtime through DOM changes, client-side rendering, and JavaScript behavior that a proxy does not fully see on its own. The ZAP team calls this out directly in its release walkthrough.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages