Phorpiex botnet keeps evolving as operators push ransomware, sextortion, and crypto-clipping malware
The Phorpiex botnet is not new, but it remains highly active and adaptable. New research from BitSight says the long-running botnet, also known as Trik, now supports several criminal operations at once, including ransomware delivery, sextortion spam, and cryptocurrency wallet hijacking through crypto-clipping malware.
BitSight says it is currently tracking around 125,000 Phorpiex infections on a daily average, with roughly 70,000 of those belonging to the peer-to-peer botnet component. The most affected countries in its current data are Iran, Uzbekistan, China, Kazakhstan, and Pakistan.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What keeps Phorpiex dangerous is its resilience. BitSight says the latest Twizt variant combines traditional command-and-control infrastructure with a peer-to-peer architecture, which means the botnet can keep operating even if defenders disrupt part of its backend.
How Phorpiex is making money now
BitSight says the botnet monetizes infections in several ways at once. Its researchers say they observed Phorpiex delivering mass ransomware, running large-scale sextortion email campaigns, and performing crypto-clipping activity that swaps cryptocurrency wallet addresses on infected systems.
The ransomware activity has drawn particular attention. BitSight says that in October 2025, operators used Phorpiex to deliver LockBit Black ransomware to machines confirmed to be inside Windows domains or corporate environments. Older reporting from Proofpoint also documented Phorpiex distributing LockBit Black at very high volume in 2024, which helps show this botnet’s ransomware role is not new.
BitSight also says that in January 2026, the botnet delivered a ransomware strain resembling the Global family against systems in China, then followed with another campaign that hit victims across 21 countries. The report says each spam wave can target between 2 million and 6 million email addresses.
Why the Twizt variant is harder to disrupt
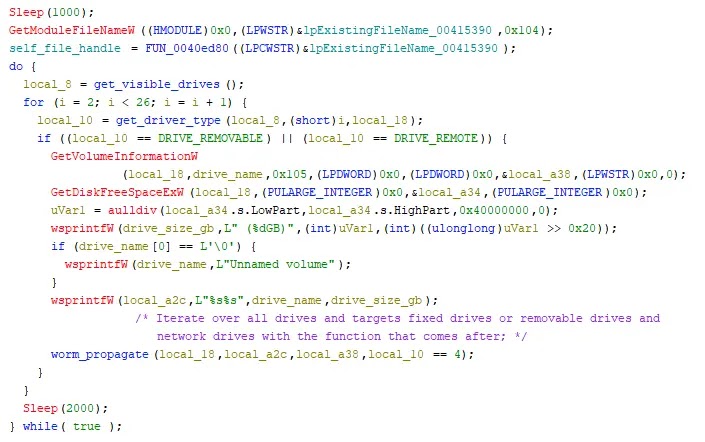
Phorpiex has survived for years because it does more than send spam. BitSight says the malware keeps persistence by copying itself into system directories and writing autorun registry keys so it relaunches after reboot.
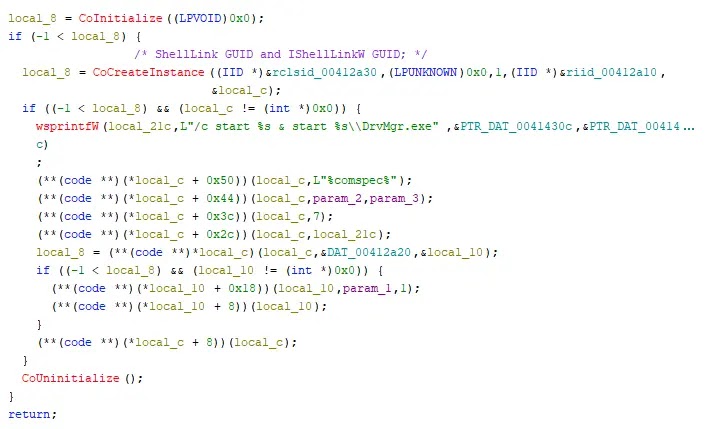
The malware also spreads through removable drives and shared folders. BitSight says infected systems can drop a hidden executable named DrvMgr.exe along with a disguised shortcut file, which helps the botnet move to other machines when users connect an infected drive elsewhere.
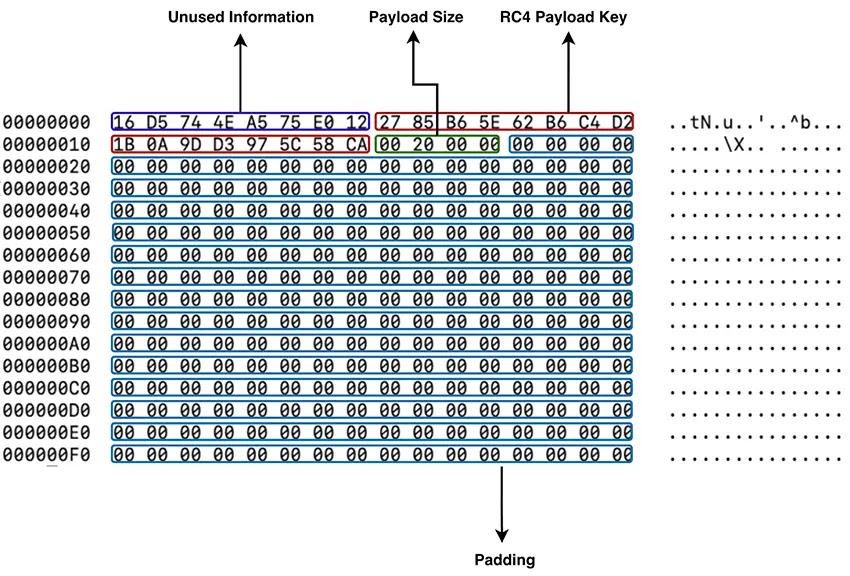
For stealth, BitSight says Phorpiex adds itself to the Windows Firewall allowed-program list under the name “Microsoft Corporation,” uses API hashing to hide the Windows functions it calls, and encrypts botnet commands inside an RSA-protected header. Together, those features make analysis and takedown efforts harder.
Phorpiex at a glance
| Item | Current reported detail |
|---|---|
| Malware family | Phorpiex, also known as Trik |
| Active variant highlighted | Twizt |
| Daily average infections | About 125,000 |
| P2P portion | About 70,000 infections |
| Main criminal uses | Ransomware, sextortion, crypto-clipping |
| Most affected countries | Iran, Uzbekistan, China, Kazakhstan, Pakistan |
| Noted ransomware campaigns | LockBit Black in late 2025, Global-like strain in early 2026 |
| Propagation methods | Spam, USB drives, shared folders, LNK files |
Source basis: BitSight research and supporting historical reporting.
- Block known Phorpiex command-and-control infrastructure and watch for suspicious outbound traffic patterns tied to botnet activity. BitSight specifically recommends blocking known C2 IPs.
- Monitor for unexpected autorun registry changes, suspicious use of
DrvMgr.exe, and unusual shortcut files on USB drives or shared folders. - Restrict USB device access on corporate systems where possible, because BitSight says the malware still uses removable media for propagation.
- Use layered email filtering and phishing defenses, since the botnet still relies heavily on mass email campaigns to deliver ransomware and sextortion messages.
- Review malware samples and wallet indicators published under the
dropped-by-phorpiextag on MalwareBazaar if your team is doing threat hunting or incident response. This recommendation comes from BitSight’s public write-up.
FAQ
Phorpiex is a long-running botnet, also known as Trik, that has been active for years and is now associated with ransomware delivery, sextortion spam, and crypto-clipping malware.
Twizt is a Phorpiex variant that uses both command-and-control servers and a peer-to-peer botnet model, which helps it stay active even if part of its infrastructure goes offline.
BitSight says it tracks about 125,000 infections on a daily average, with around 70,000 tied to the P2P portion of the botnet.
BitSight says the botnet supports ransomware delivery, sextortion campaigns, and crypto-clipping, which hijacks copied wallet addresses during cryptocurrency transactions.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages