Venom Stealer turns ClickFix pages into a full data theft pipeline, researchers say

Venom Stealer is a malware-as-a-service tool that uses ClickFix social engineering pages to trick victims into launching the infection themselves. BlackFog says the platform goes beyond basic password theft by combining staged delivery, credential harvesting, wallet targeting, and continued post-infection monitoring in one operator-controlled workflow.
According to BlackFog, the malware is sold under the handle “VenomStealer” through a subscription model that ranges from $250 per month to $1,800 for lifetime access. The same report says the service includes Telegram-based licensing, a 15% affiliate program, and a native C++ payload compiled for each operator from the web panel.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
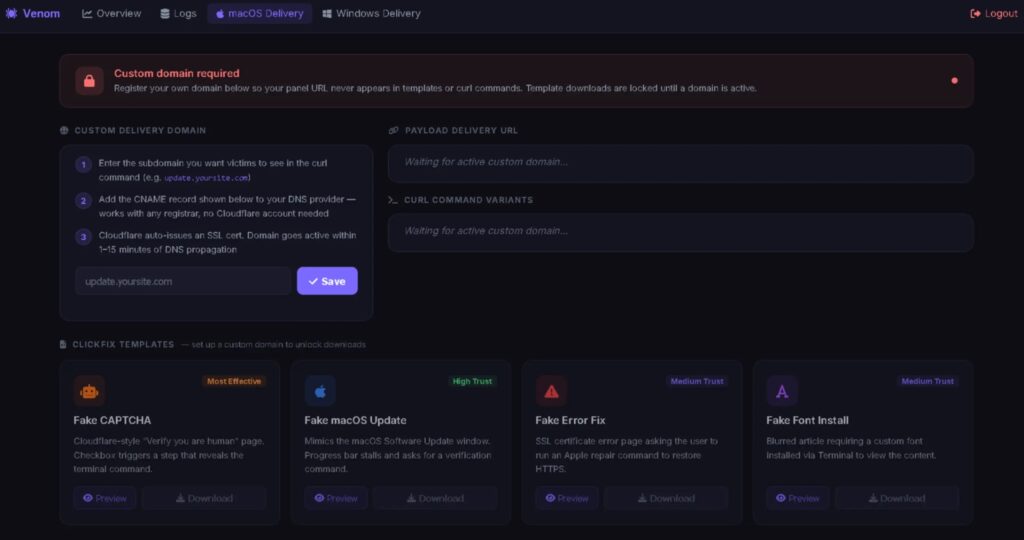
The delivery method is what makes the campaign especially effective. BlackFog says operators get ready-made ClickFix templates for Windows and macOS, including fake Cloudflare CAPTCHA pages, fake OS update prompts, fake SSL certificate warnings, and fake font install pages. Those lures try to get the victim to open Run on Windows or Terminal on macOS, paste a command, and execute it manually.

Why Venom Stealer stands out
Many infostealers focus on grabbing saved passwords and session data, then exiting. BlackFog says Venom keeps working after the first theft by maintaining what it describes as a continuous exfiltration pipeline rather than a one-time collection event.
BlackFog also says the malware immediately targets Chromium- and Firefox-based browsers, collecting saved passwords, cookies, browsing history, autofill data, and cryptocurrency wallet material from every profile it can reach. The report adds that system fingerprinting and browser extension inventories are gathered as well, giving operators a broad picture of the infected host.
Another notable claim in the report involves Chrome credential access. BlackFog says Venom abuses the CMSTPLUA COM interface to elevate privileges silently and retrieve the key needed to decrypt Chrome’s v10 and v20 credential storage without showing a UAC prompt.
How the post-infection monitoring works
BlackFog says Venom does not stop after the first data dump. Instead, it stays on the machine and watches Chrome’s Login Data file every 30 seconds so it can capture newly stored credentials after the initial infection.
That means the risk continues even after the victim notices something is wrong. If a user changes passwords on the same compromised machine and Chrome saves the new credentials, BlackFog says Venom can steal those updated secrets as well.

The report also says wallet theft is heavily automated. BlackFog claims any discovered cryptocurrency wallet data is sent to a server-side GPU cracking engine, and that the tool targets wallet ecosystems including MetaMask, Phantom, Exodus, and Electrum across nine blockchain networks. A March 9 update reportedly added a file password and seed finder that scans the local filesystem for wallet recovery material.
Venom Stealer at a glance
| Item | Reported detail |
|---|---|
| Malware family | Venom Stealer |
| Business model | Malware-as-a-service |
| Pricing | $250/month to $1,800 lifetime |
| Delivery method | ClickFix social engineering pages |
| Main lure types | Fake CAPTCHA, fake OS update, fake SSL error, fake font install |
| Main targets | Browser credentials, cookies, autofill, wallet data |
| Persistence behavior | Continues monitoring Chrome’s Login Data file |
| Claimed update pace | Multiple updates in March 2026 |
Source basis: BlackFog research.
What defenders should focus on
- Train users to treat any page that asks them to paste commands into Run, PowerShell, Command Prompt, or Terminal as highly suspicious. BlackFog says Venom relies on that exact interaction model.
- Restrict PowerShell where appropriate and consider limiting access to the Run dialog for standard users through Group Policy. These are mitigation steps BlackFog specifically recommended.
- Watch outbound traffic closely, because BlackFog says the threat depends on continuous data leaving the endpoint rather than a single short exfiltration burst.
- Treat a host as compromised until rebuilt if Venom is suspected, since the reported 30-second polling of Chrome’s credential store means password resets on the same device may not help. This is an inference based on BlackFog’s described behavior.
- Review the sample text you provided here for comparison:
FAQ
Venom Stealer is a malware-as-a-service platform that BlackFog says combines ClickFix delivery with credential theft, wallet targeting, and ongoing post-infection data collection.
In BlackFog’s description, ClickFix refers to fake web pages that trick users into launching commands themselves, which helps the malware avoid some behavior-based defenses because the action appears user-initiated.
BlackFog says it does not just steal data once. It keeps monitoring the machine for new credentials and adds wallet-focused modules that support broader financial theft.
The report says it supports both Windows and macOS for ClickFix delivery, and steals from Chromium- and Firefox-based browsers after infection.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages