New Progress ShareFile bugs can let attackers take over servers without logging in

Organizations running the on premises ShareFile Storage Zones Controller should patch now. Two newly disclosed flaws in the 5.x branch can be chained to let an unauthenticated attacker reach restricted configuration pages and then achieve remote code execution on the server. Progress says customers should upgrade to version 5.12.4 or move to any 6.x release, which is not affected.
The bugs affect customer managed ShareFile Storage Zones Controller deployments, not the broader ShareFile cloud service in general. Progress and multiple security writeups describe the first issue as an authentication bypass and the second as an upload based code execution flaw that becomes far more dangerous when paired together.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
RunZero and other defenders rate the pair as critical. Public CVE records list CVE-2026-2699 with a CVSS score of 9.8 and CVE-2026-2701 with a CVSS score of 9.1, which puts this issue near the top of the patch queue for exposed servers.
Why this attack chain matters
Storage Zones Controller is the on premises component that lets companies keep files in their own infrastructure while still using ShareFile’s cloud managed workflow. That design makes these systems attractive targets because they often sit close to sensitive documents, identity systems, and business critical file sharing paths.
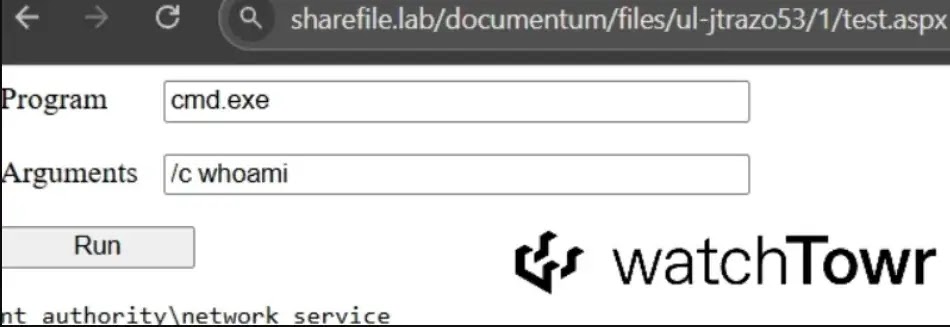
WatchTowr says the first flaw stems from execution continuing after a redirect on the Admin.aspx configuration page. In practice, the app sends a redirect to the login page, but the underlying page logic still runs, which can expose admin functionality to someone who never authenticated.
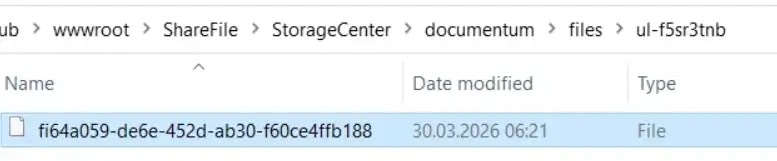
After that, the second flaw can allow a malicious archive to land in a server controlled path and be extracted into a web accessible location. WatchTowr showed that this chain can place an ASPX webshell in the ShareFile webroot and then execute code remotely on the target server.
What researchers and the vendor are saying
Progress publicly disclosed the issue on April 2, 2026, and security reporting says the company released the fix in ShareFile Storage Zones Controller 5.12.4 on March 10, before the public advisory went live. WatchTowr’s published timeline says it reported the bugs in February, Progress replicated the chain on February 18, and the embargo later lifted in April.
Progress also said it had not received reports of active exploitation at the time of disclosure. That is good news, but it should not slow patching, because public research and proof of concept details now make copycat exploitation much more likely.
Exposure could be broad. WatchTowr estimated that about 30,000 Storage Zones Controller instances were internet facing, while other reporting noted that Shadowserver observed roughly 700 exposed systems in its own view. Those numbers are measured differently, but both suggest there is a meaningful external attack surface.
Affected versions and fix guidance
| Item | Details |
|---|---|
| Affected product | Customer Managed ShareFile Storage Zones Controller 5.x |
| Fixed version | 5.12.4 |
| Unaffected branch | 6.x releases |
| CVE IDs | CVE-2026-2699 and CVE-2026-2701 |
| Severity | 9.8 and 9.1 CVSS, respectively |
What defenders should do right now
Patch any ShareFile Storage Zones Controller 5.x system immediately.
Move to version 5.12.4 at minimum, or migrate to a supported 6.x release if your environment allows it.
Review exposed systems for signs of abuse.
Look for suspicious configuration changes, unexpected files in web facing directories, and any ASPX files that do not belong in the webroot. That guidance follows directly from the demonstrated attack path published by researchers.
Limit internet exposure where possible.
If a Storage Zones Controller does not need to sit on the public internet, move it behind tighter access controls. Even where patching is complete, reducing exposure lowers risk from future flaws and opportunistic scanning. This is a defensive inference based on the fact that the chain requires network access to the affected instance.
FAQ
The biggest risk is full remote code execution on an exposed ShareFile Storage Zones Controller without valid credentials. Researchers showed the two bugs can be chained to place a webshell and run code on the server.
The public advisories focus on customer managed Storage Zones Controller deployments in the 5.x branch. They do not describe this as a general ShareFile cloud platform issue.
As of the public disclosures, Progress said it had not received reports of active exploitation. That statement could change later, so defenders should still treat the issue as urgent.
Progress says customers should upgrade to ShareFile Storage Zones Controller 5.12.4 or move to any 6.x release, which is not impacted by these vulnerabilities.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages