ResokerRAT turns Telegram into a stealth control channel for Windows attacks

A newly documented Windows remote access trojan called ResokerRAT uses Telegram’s Bot API as its command-and-control channel, giving attackers a way to control infected systems without relying on a custom server. That matters because Telegram traffic can blend in with normal web activity, which can make the malware harder to flag quickly on corporate networks.
K7 Security Labs said the malware can capture screenshots, log keystrokes, download more payloads, and weaken security settings after infection. The report says the malware also tries to gain higher privileges, block analysis tools, and maintain persistence on the compromised machine.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The short answer is yes, this is a serious Windows threat, especially for users who download unknown executables or open files from untrusted sources. ResokerRAT does not need a flashy exploit chain to cause damage because once it runs, it can hand broad remote control to the attacker.
How ResokerRAT works after infection
According to K7’s analysis, the malware starts with checks designed to frustrate security analysis before it fully connects to the attacker’s infrastructure. It creates a mutex to avoid multiple instances, checks for debugging, and can relaunch itself with administrator rights through ShellExecuteExA using the runas option.
K7 also says the malware scans for well-known analysis tools and can terminate them to reduce the chances of inspection. On top of that, it installs a keyboard hook through SetWindowsHookExW, a Windows API Microsoft documents for installing hook procedures that can monitor input events.
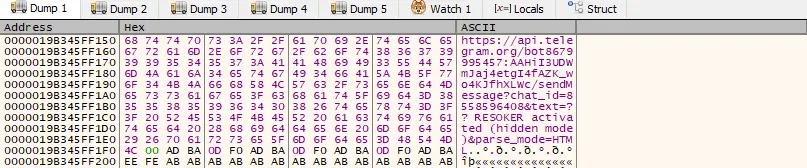
The malware’s most notable feature is the way it handles command-and-control traffic. Telegram’s official Bot API is HTTP-based, and K7 says ResokerRAT builds requests with a hardcoded bot token and chat ID, then polls Telegram for instructions instead of contacting a traditional attacker-owned server.
Why Telegram abuse makes this malware harder to spot
This design gives attackers an obvious advantage. Many security teams watch for suspicious command servers or strange outbound destinations, but Telegram API traffic can look less alarming if the environment already allows it. That can buy the attacker more time inside the network.
K7 says the malware can accept commands for screenshots, startup persistence, extra file downloads, and even weaker User Account Control behavior. The report specifically notes a /uac-min command that changes ConsentPromptBehaviorAdmin to 0, which can suppress prompts that normally warn users before privileged actions.
That means the malware is not just a data thief. It can also act as a staging point for follow-on compromise, giving attackers a way to expand access, pull more tools onto the host, and keep control after reboot.

ResokerRAT at a glance
| Item | Details |
|---|---|
| Malware family | Remote access trojan |
| Target | Windows systems |
| C2 method | Telegram Bot API |
| Reported by | K7 Security Labs |
| Key behaviors | Screenshot capture, keylogging, persistence, downloads, privilege escalation |
| Anti-analysis steps | Debugger checks, mutex creation, process termination |
| Admin abuse | Relaunch with runas, weaker UAC behavior |
| Main risk | Hidden remote control and data theft |
Indicators and notable capabilities
- Uses Telegram’s Bot API instead of a traditional C2 server.
- Creates
Global\ResokerSystemMutexto keep only one instance active. - Checks for debugging with
IsDebuggerPresent. - Attempts elevation with ShellExecuteExA and the
runasverb. - Installs a keyboard hook with SetWindowsHookExW.
- Can download additional files through hidden PowerShell commands.
- Can add itself to startup for persistence.
What defenders should do now
- Block or closely inspect outbound access to Telegram API endpoints where business use does not require them.
- Restrict PowerShell where possible and alert on hidden or suspicious PowerShell child processes.
- Watch for attempts to change UAC-related registry values, especially
ConsentPromptBehaviorAdmin. - Flag tools that create persistence through Run keys or relaunch themselves with elevated rights.
- Train users not to run executables from unknown sources, cracked packages, or unsolicited downloads.
FAQ
ResokerRAT is a Windows remote access trojan that uses Telegram’s Bot API to receive commands and send data back to attackers.
Telegram gives attackers a ready-made communications channel. Instead of maintaining their own server, they can hide activity behind traffic tied to a trusted public platform.
K7 says it can capture screenshots, log keystrokes, kill analysis tools, download more files, gain persistence, and weaken UAC protections.
They should monitor Telegram-related outbound traffic, limit risky scripting behavior, harden endpoint detection, and stop users from running untrusted executables.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages