Researcher releases BlueHammer exploit code for Windows Defender flaw, raising risk of full system compromise

A publicly released exploit called BlueHammer has exposed an unpatched Windows local privilege escalation flaw that can let a low-privileged user gain NT AUTHORITY\SYSTEM or, in some cases, elevated administrator rights. Security researchers say the issue affects modern Windows systems and abuses Microsoft Defender’s update process rather than a browser or remote service.
The exploit matters because attackers do not need a kernel bug or memory corruption chain to use it. Cyderes says BlueHammer abuses legitimate Windows features, including Microsoft Defender’s update workflow, opportunistic locks, the Windows Cloud Files API, and Volume Shadow Copy Service, then chains them in a way that leaks sensitive data and enables privilege escalation.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Current reporting says the exploit code is already public and has been independently tested by outside researchers. BleepingComputer and Cyderes both say vulnerability researcher Will Dormann confirmed the proof of concept works, although reliability can vary depending on the target system and account state.
How BlueHammer works
BlueHammer is a local privilege escalation issue, so it does not give attackers initial remote access by itself. Instead, it becomes dangerous after an attacker already lands on a machine through phishing, malware, a stolen account, or another entry point.
Cyderes says the exploit targets Defender’s signature update process and uses a race condition plus path confusion to redirect privileged file operations. The published analyses say this can expose the Security Account Manager, or SAM hive, which stores password hash material for local accounts.
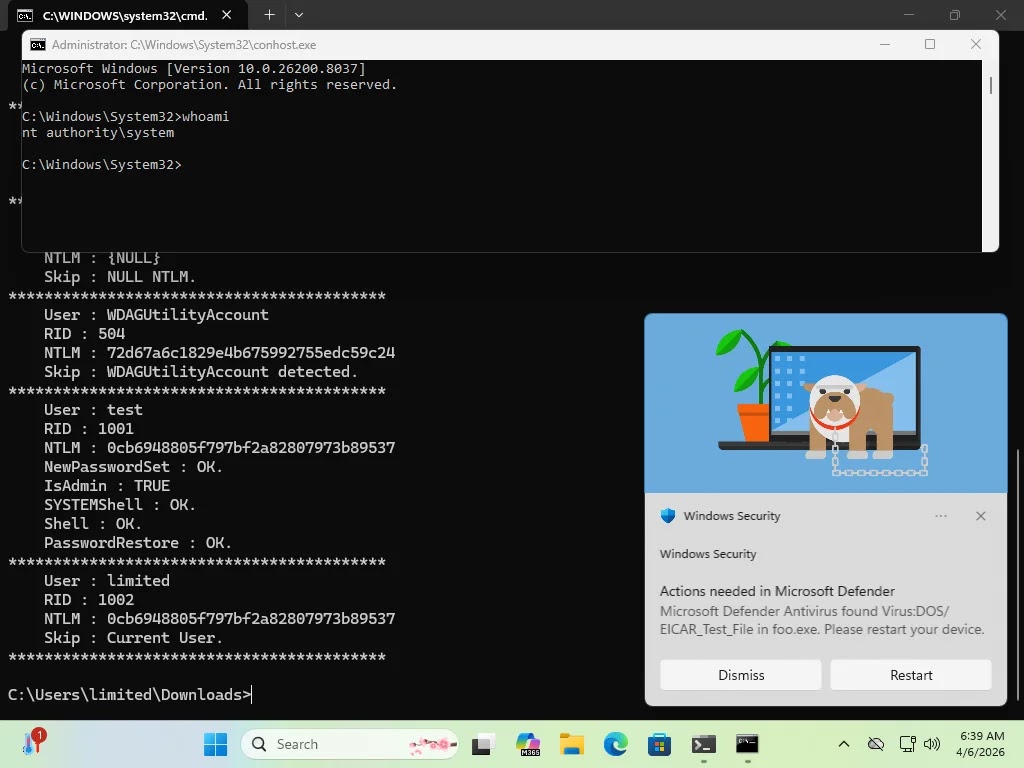
Once the SAM data is exposed, the attacker can use it to move higher in the privilege chain. Reports say the public proof of concept can, under the right conditions, end with SYSTEM-level execution on Windows or elevated administrator access on some Windows Server systems.
BlueHammer at a glance
| Item | Details |
|---|---|
| Exploit name | BlueHammer |
| Vulnerability type | Local privilege escalation |
| Affected area | Microsoft Defender update process |
| Public exploit code | Yes |
| Patch available | No public patch reported as of April 8, 2026 |
| Main risk | SYSTEM or elevated administrator access after local foothold |
Why the disclosure is getting attention
The researcher behind BlueHammer, known publicly as Chaotic Eclipse or Nightmare-Eclipse in different reports, said frustration with Microsoft’s handling of the disclosure played a role in the public release. Coverage from BleepingComputer, TechRadar, and other outlets says the researcher criticized Microsoft’s vulnerability response process and pointed to a difficult disclosure experience.
Still, the more important issue for defenders is the exploit itself. Because the flaw remains unpatched and the code is public, security teams have to assume attackers may test or adapt it quickly, especially in post-compromise scenarios where local privilege escalation can turn a minor breach into full machine control.
The exploit also appears to work against fully updated systems in at least some cases. Cyderes says BlueHammer affects modern Windows builds and does not rely on old unsupported configurations, which raises the pressure on defenders to lean on hardening and detection while waiting for Microsoft to act.
Why defenders should care
- The exploit code is public, which lowers the barrier for copycat abuse.
- The issue can lead to NT AUTHORITY\SYSTEM access after only a low-privilege foothold.
- It targets a trusted Microsoft Defender workflow, not a random third-party utility.
- A local privilege escalation bug like this can fit neatly into ransomware or post-exploitation chains.
What organizations should do now
Until Microsoft ships a fix, defenders should focus on reducing post-compromise paths and watching for suspicious behavior around Defender updates. Cyderes recommends monitoring for symbolic link creation in Defender-related directories, unusual reparse points, access to Volume Shadow Copy paths, and temporary files that resemble copied SAM artifacts.
Microsoft’s own Defender guidance also points to hardening steps that matter here. Microsoft says tamper protection helps protect certain security settings from being disabled or changed, and it recommends keeping Defender security intelligence and platform updates current. Microsoft also documents that tamper protection and DisableLocalAdminMerge can help protect antivirus exclusions from unauthorized local changes in managed environments.
That will not patch BlueHammer, but it can make follow-on abuse harder. Teams should also limit local admin rights, strengthen endpoint monitoring, and review any signs of odd SYSTEM-level process spawning, especially on machines where an attacker may already have user-level access. This recommendation is based on the exploit’s published local privilege escalation chain and Microsoft’s documented defender hardening features.
Recommended actions
| Priority | Action | Why it matters |
|---|---|---|
| High | Limit unnecessary local administrator accounts | Reduces the value of stolen local credential material |
| High | Monitor Defender update folders for reparse points or symbolic links | Helps spot the exploit chain early |
| High | Watch for unusual access to VSS-backed paths and SAM-like files in temp locations | May reveal credential leakage attempts |
| Medium | Enable tamper protection where supported | Helps stop changes to protected Defender settings |
| Medium | Use DisableLocalAdminMerge in managed environments | Protects antivirus exclusions from local modification |
| Medium | Keep Defender platform and intelligence updates current | Maintains Microsoft’s latest defensive improvements |
What this means for Windows users
BlueHammer does not appear to be a wormable internet bug that anyone can use remotely without first getting onto the device. Even so, it is serious because modern attacks rarely stop at initial access. Attackers often combine a local foothold with privilege escalation to disable defenses, move laterally, and deploy ransomware.
The case also puts extra scrutiny on Microsoft Defender’s trusted update path. When attackers can twist a built-in security workflow into an escalation mechanism, defenders need to monitor the surrounding behavior, not just malware signatures or exploit kits. That is an inference supported by the published exploit analyses and Microsoft’s tamper-resilience guidance.
For now, organizations should assume BlueHammer will stay on attackers’ radar until Microsoft issues a patch or advisory. Public exploit code, working proof of concept results, and the lack of a fix create exactly the kind of window threat actors look for.
FAQ
BlueHammer is a publicly released exploit for an unpatched Windows local privilege escalation flaw tied to Microsoft Defender’s update process. Researchers say it can let a low-privileged local user gain SYSTEM or elevated administrator access.
No evidence in current reporting suggests that. BlueHammer is described as a local privilege escalation issue, which means an attacker needs a foothold on the machine first.
I could not find a Microsoft security advisory or patch for BlueHammer as of April 8, 2026. Current reporting consistently describes the issue as unpatched and without a public CVE assignment.
Published analyses say it abuses Microsoft Defender’s signature update workflow and combines that with other legitimate Windows components such as Volume Shadow Copy Service and opportunistic locks.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages