Fiber optic cables can be turned into covert microphones, NDSS 2026 researchers warn
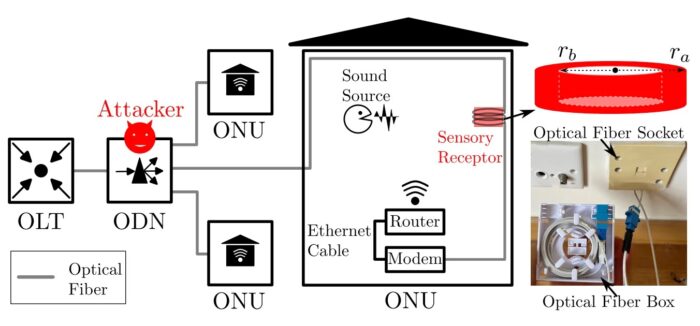
Ordinary fiber optic internet cables can be used to recover speech and other room sounds under the right conditions, according to research presented at NDSS 2026. The attack does not need a traditional microphone at the listening end. Instead, it relies on the fact that optical fibers physically react to sound-driven vibrations, which can then be measured with distributed acoustic sensing, or DAS.
The researchers behind the paper come from The Hong Kong Polytechnic University, The Chinese University of Hong Kong, and the Technological and Higher Education Institute of Hong Kong. Their NDSS paper says an attacker with access to one end of a telecom fiber can monitor sound-induced deformations at the other end and recover useful information from the original sound waves.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This does not mean every home fiber line instantly becomes a live bug. The paper describes a practical but targeted attack that needs physical access to fiber infrastructure and added sensing equipment. Still, the results raise real privacy concerns for homes, offices, and meeting rooms that use fiber-to-the-home connections.
How the attack works
The core idea is simple. Acoustic waves cause tiny deformations in optical fiber, and those deformations create phase shifts in Rayleigh backscattering. A DAS system can read those shifts and turn them into a recoverable sound signal.
The researchers also found that standard fiber by itself is not sensitive enough for clear airborne speech capture. To improve results, they built a “sensory receptor,” a hollow PET cylinder wrapped with optical fiber, which amplifies acoustic pressure fluctuations and makes speech recovery much more practical. The slides show test configurations using outer diameters of 65, 85, and 100 mm, with up to 15 meters of wrapped fiber.
That matters because the device can be integrated into normal-looking telecom hardware rather than a classic spy microphone. The paper frames this as a side-channel risk tied to real FTTH deployments, where attackers who can access one end of the fiber may be able to capture activity near the other end.
What the researchers demonstrated
| Capability | Reported result |
|---|---|
| Speech recovery | Word error rate stayed below roughly 20% at 2 meters on the best-performing model in the slide deck |
| Indoor localization | Average localization error of 0.77 m ± 0.17 m in a 27.04 m² room |
| Sound event detection | Fine-tuned model reached 0.43 accuracy at 2 m, above random guessing probability of 0.07 |
| Anti-jamming resilience | Optical fiber setup showed little degradation under ultrasonic jamming compared with conventional devices |
Source: NDSS 2026 paper page and presentation slides.
Why this matters now
The paper argues this issue matters more because FTTH deployment is already widespread. The NDSS presentation cites FTTH Council Europe data showing very high penetration in places such as the UAE, South Korea, China, Hong Kong SAR, and Singapore, with lower but still meaningful deployment in the United States and United Kingdom.
That broad rollout expands the number of environments where fiber lines run through private indoor spaces. In practical terms, the research points to a risk for executive rooms, corporate offices, government buildings, and homes where fiber slack, routing, and endpoint access may create opportunities for covert sensing.
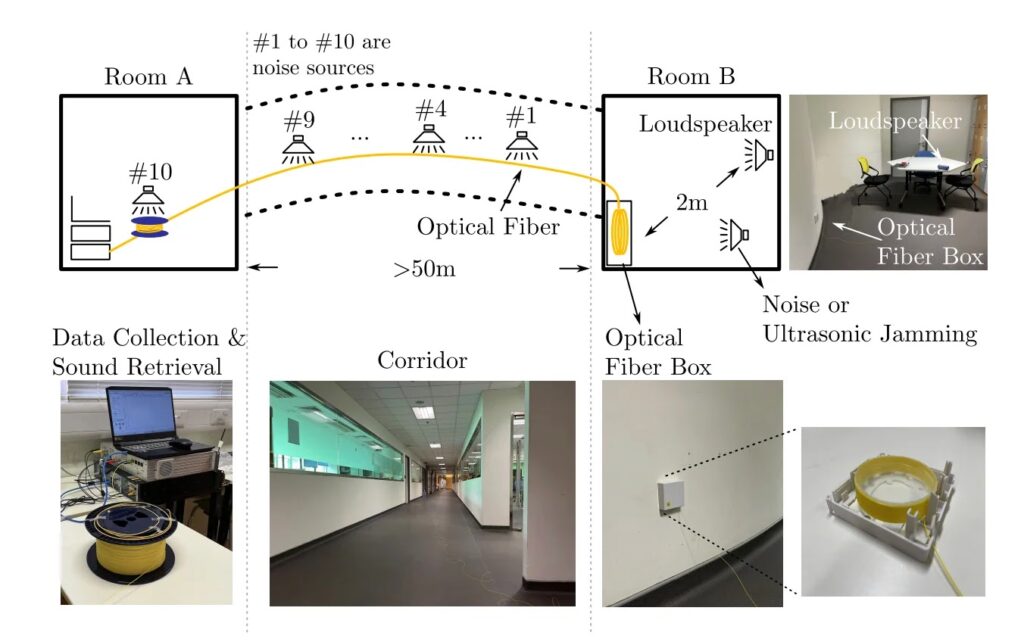
Another striking finding is that common ultrasonic jammers did not stop the fiber-based setup in the same way they disrupted regular microphones and voice recorders. In the presentation, the optical fiber system kept a low word error rate under jamming, while phones and compact recorders degraded sharply.
Key takeaways
- This is a side-channel attack against telecom fiber, not a software flaw in routers or ISPs.
- The attack appears practical only when an adversary can access fiber infrastructure and attach sensing gear.
- The research shows speech recovery, indoor localization, and sound-event detection are all possible.
- Traditional RF bug sweeps would not help much because this is not a radio transmitter. That point follows from the attack method described in the paper and slides.
Mitigations and practical defenses
The researchers proposed several mitigation ideas rather than a single fix. Their slides recommend polished connectors that introduce Fresnel reflection, optical isolators that prevent scattering from returning to an attacker, and installation practices that reduce excess cable length and avoid loops around resonant surfaces.
In real deployments, physical security matters just as much. Network operators and facility teams should pay close attention to who can access fiber endpoints, junction boxes, slack loops, and distribution hardware during installs, upgrades, and maintenance. That is an inference from the attack model in the paper, but it follows directly from the need to reach one end of the fiber and attach sensing equipment.
For high-security spaces, the bigger lesson is that fiber should no longer be treated as automatically safe from acoustic surveillance. The NDSS authors say their results raise important privacy concerns for fiber-optic communication networks, especially as FTTH becomes more common in modern buildings.
Suggested defensive steps
- Limit physical access to optical network terminals, distribution points, and indoor fiber boxes.
- Minimize excess fiber slack inside rooms and avoid routing cables against desks, walls, or other resonant surfaces.
- Consider polished connectors and optical isolators where the environment justifies extra protection.
- Add soundproofing in sensitive areas where fiber runs through boardrooms or secure offices.
- Review telecom maintenance processes so unauthorized hardware changes are easier to detect. This is a practical inference from the attack requirements.
FAQ
It showed that telecom optical fiber can be exploited for acoustic eavesdropping, including speech recovery, indoor localization, and sound-event detection, when paired with distributed acoustic sensing and a custom sensory receptor.
No. The attack needs targeted access and added sensing equipment. The paper shows practicality, not automatic mass surveillance on every fiber connection.
Because the attack does not rely on a standard microphone. The NDSS slides show much less degradation for the optical fiber setup than for phones and voice recorders under ultrasonic jamming.
Organizations with sensitive conversations and accessible fiber infrastructure, such as corporate offices, government sites, and diplomatic or executive spaces, face the clearest risk from this kind of side-channel attack. That conclusion follows from the paper’s threat model and reported results.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages