CUPS flaw chain can let remote attackers gain code execution and root-level impact
A newly disclosed CUPS vulnerability chain can let an unauthenticated remote attacker reach code execution on vulnerable, network-exposed print servers and then escalate that access into a root-level file overwrite. The chain involves CVE-2026-34980 and CVE-2026-34990, and the disclosures currently affect OpenPrinting CUPS 2.4.16 and earlier.
The first bug, CVE-2026-34980, affects CUPS setups that expose a shared PostScript queue over the network. Ubuntu’s security notice says an unauthorized client can send a Print-Job to that queue without authentication, abuse how a newline survives escaping and reparsing, and then make the server execute an attacker-chosen existing binary as the lp service user.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
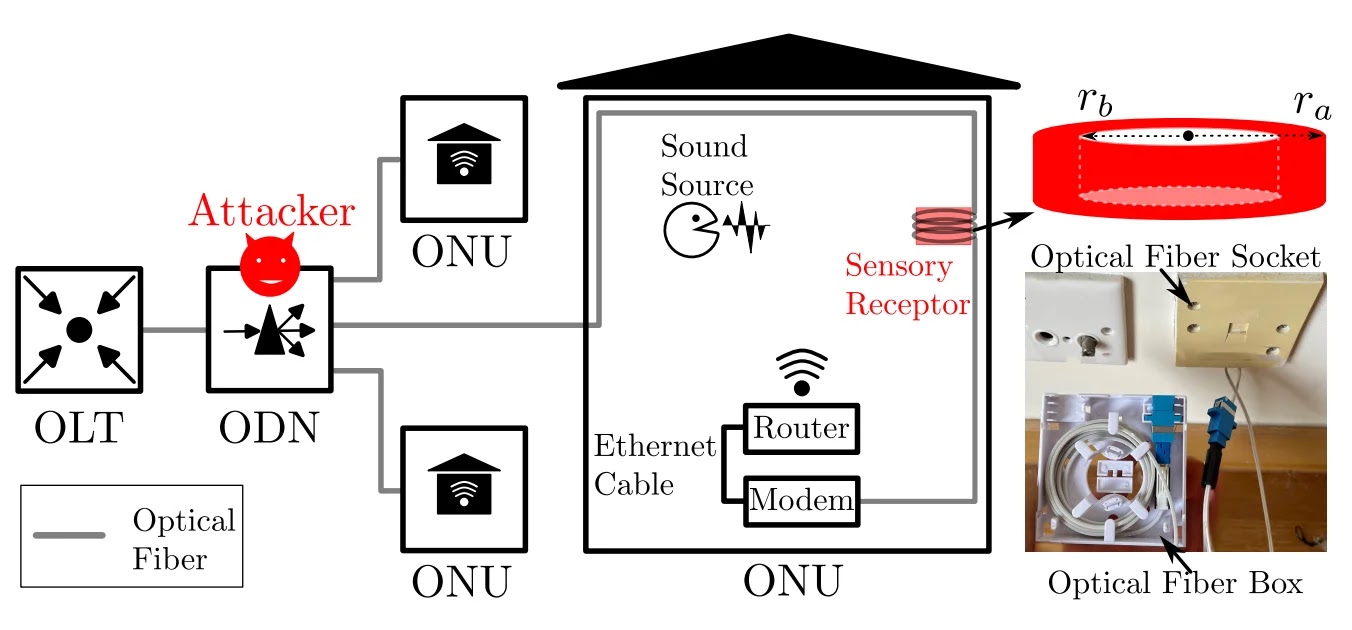
]The second bug, CVE-2026-34990, is a local privilege escalation issue. The OpenPrinting advisory says a local unprivileged user can trick cupsd into authenticating to an attacker-controlled localhost IPP service with a reusable Authorization: Local ... token, then use that token to drive /admin/ requests and persist a file:///... queue that can overwrite files as root.
How the chain works
The remote part of the chain depends on a specific deployment choice. Ubuntu says CVE-2026-34980 requires a network-exposed cupsd instance with a shared PostScript target queue, which is not the default setup for most ordinary desktops but can exist on print servers and other deliberately shared environments.
If an attacker gets that first stage, they can reach code execution as lp, not immediately as root. The OpenPrinting advisory for CVE-2026-34990 then describes how a low-privilege local foothold can become an arbitrary root file overwrite by abusing temporary printer creation and localhost authentication behavior.
That means the most alarming version of this story is a chain, not a single standalone unauthenticated root RCE bug. Public disclosures describe it as unauthenticated remote access to lp code execution that can be chained with a local privilege escalation flaw to produce root-level impact on affected systems.
At a glance
| CVE | What it does | Access needed | Stated impact |
|---|---|---|---|
| CVE-2026-34980 | Lets an unauthorized client abuse a shared PostScript queue | Remote, if CUPS is network-exposed with shared PostScript queue | Code execution as lp |
| CVE-2026-34990 | Abuses localhost auth and temporary printers | Local unprivileged access | Arbitrary root file overwrite |
Patch status and exposure
At the time of publication, both public records I checked say there are no publicly available patches. Ubuntu states that directly for CVE-2026-34980, and the NVD entry for CVE-2026-34990 repeats the same status for that flaw.
That does not mean every Linux or Unix-like system is equally exposed. The remote bug needs a network-exposed CUPS service with a shared PostScript queue, while the privilege-escalation step needs local access after the first foothold. The OpenPrinting advisory also notes the chain can produce remote root file overwrite only when the first advisory’s prerequisites are met.
Security controls can reduce the damage. The researcher write-up and vendor references say AppArmor, SELinux, or similar confinement can limit what a compromised CUPS process can modify, which can sharply reduce the blast radius even if an attacker reaches the service.
What admins should do now
- Do not expose
cupsdto the internet. Ubuntu lists this as the main mitigation, especially for shared PostScript queues. - Disable or avoid shared legacy PostScript queues unless you truly need them.
- Restrict access to localhost printing and printer administration where possible.
- Keep CUPS under AppArmor, SELinux, or another mandatory access control policy.
- Watch for unusual printer creation,
file:///device URIs, and suspicious print-job behavior on exposed servers. This point is an operational inference from the published exploit path.
Why this matters
CUPS often runs quietly in the background, so many teams do not monitor it as closely as internet-facing web services. But on systems that expose print services to a network, especially in office or enterprise environments, the service can become a real attack surface. That makes configuration review just as important as patching.
The current disclosures also show that the worst-case headline needs context. The chain can lead to root-level impact, but only after the attacker meets the specific conditions required for both flaws. Saying only “remote root RCE in CUPS” skips over those prerequisites and overstates how broadly the chain applies.
FAQ
No. The public advisories describe a chain. CVE-2026-34980 needs a network-exposed CUPS server with a shared PostScript queue, and CVE-2026-34990 is a local privilege escalation that turns that foothold into root-level file overwrite.
The public records I checked describe OpenPrinting CUPS 2.4.16 and earlier as affected.
The current Ubuntu and NVD records say no publicly available patches were available at publication time.
Do not expose cupsd to the internet, especially if you use shared PostScript queues, and keep the service confined with AppArmor or SELinux where possible.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages