Hackers use fake security software to deliver LucidRook malware in Taiwan attacks
A newly documented malware campaign is targeting organizations in Taiwan with a fake security tool that looks legitimate at first glance. Cisco Talos says the operation uses spearphishing emails, password-protected archives, and a fake Trend Micro themed dropper to deliver a new malware family called LucidRook.
The targets appear selective, not random. Talos says the campaign focused on Taiwanese non-governmental organizations and suspected universities, with lures written in Traditional Chinese and decoy documents crafted to match the local context. One decoy was an official Taiwanese government letter sent to universities, which helped the phishing email look more believable.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This attack matters because it blends convincing social engineering with a technically solid infection chain. The operators hide malicious code inside a fake security product, then use DLL sideloading and encrypted staging to keep the malware quiet while it profiles the system and reaches out for the next payload.
How the LucidRook campaign works
According to Cisco Talos, the infection starts with a spearphishing email that pushes the victim toward a shortened URL. That link leads to a password-protected compressed archive containing a disguised shortcut file and decoy documents. Talos calls the initial dropper LucidPan.
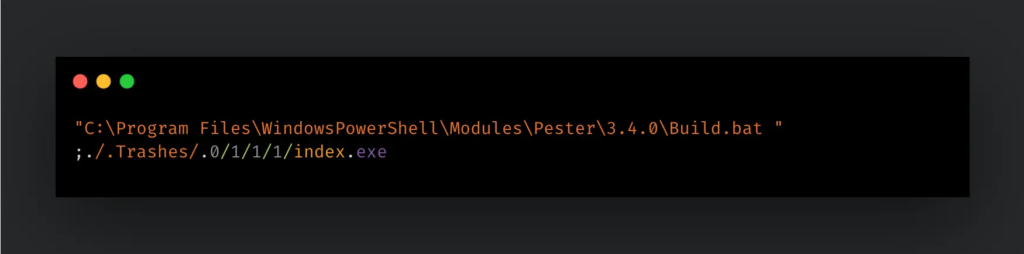
LucidPan impersonates a Trend Micro product by copying its icon and app name. When the victim opens the disguised LNK file, it launches a legitimate executable named index.exe, which then loads a malicious DismCore.dll placed next to it. Microsoft documents this family of abuse as DLL search order hijacking, where an app loads a malicious DLL from a location the attacker controls.
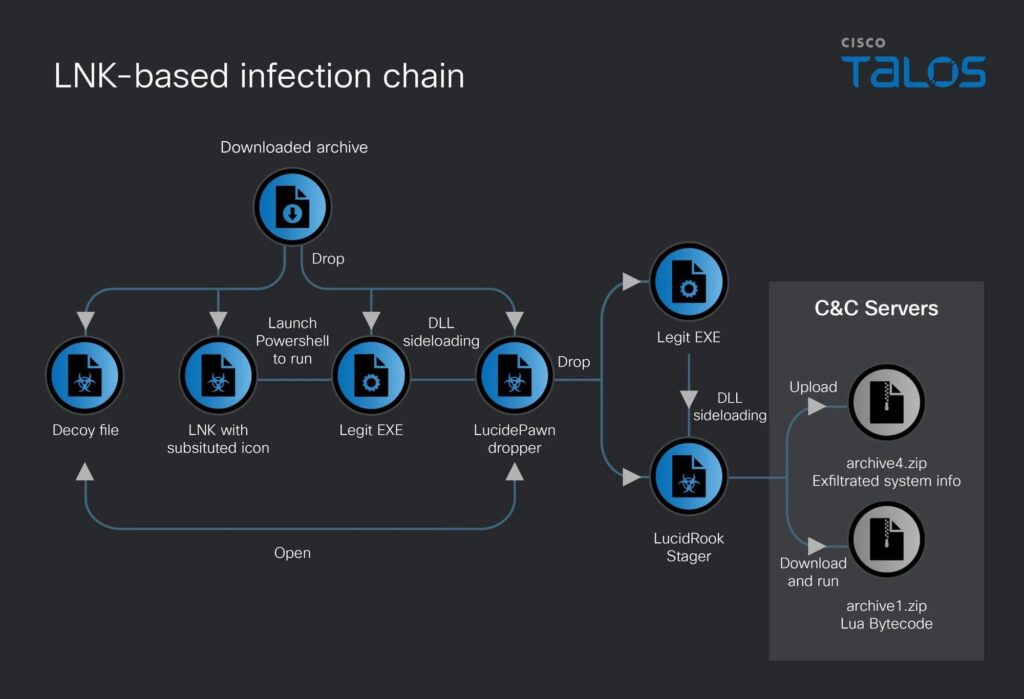
Talos says the malware stores components under %APPDATA%, creates persistence through a Startup folder shortcut, and uses msedge.exe naming to blend into normal activity. Before pulling the next stage, it gathers host details such as username, computer name, drives, running processes, and installed software.
What makes LucidRook notable
LucidRook is not a simple loader. Talos describes it as a stager built around a Lua interpreter and Rust-compiled libraries, which gives the malware a modular feel and makes analysis harder than with a basic single-binary implant. Researchers also found a related reconnaissance tool called LucidNight, suggesting the operators can survey a victim before deploying the full malware chain.
The malware also uses layered obfuscation and encrypted local packaging. Talos says it stores collected information in encrypted files named 1.bin, 2.bin, and 3.bin, then places them into a password-protected archive using RSA keys before moving data out of the system.
Another unusual detail is the infrastructure choice. Talos says the attackers used compromised FTP servers belonging to Taiwanese printing companies, and that those servers had credentials publicly exposed on their own websites. The malware then used those servers to upload stolen data and retrieve an encrypted Lua bytecode payload.
Why defenders should take this seriously
Cisco Talos assesses with medium confidence that this was a targeted intrusion, not broad opportunistic malware. That matters because tailored phishing, local language lures, and trusted branding usually raise the success rate against organizations that handle sensitive information.
The use of DLL sideloading also increases the risk of missed detection. Microsoft warns that when an application loads a DLL without a fully qualified path, an attacker who controls part of the search path can place a malicious copy there. That lets the malware ride along with a legitimate executable instead of standing out as a separate suspicious process.
At the email layer, the campaign follows a pattern security agencies have warned about for years. CISA says phishing often tries to get people to open harmful links, emails, or attachments that can infect a device or steal information. Password-protected archives add another layer because they can reduce the visibility of content at the mail gateway.
LucidRook at a glance
| Item | Verified detail |
|---|---|
| Malware family | LucidRook |
| Initial dropper | LucidPan |
| Related tool | LucidNight |
| Main targets | Taiwanese NGOs and suspected universities |
| Delivery method | Spearphishing emails with shortened URLs and password-protected archives |
| Disguise | Fake Trend Micro themed application |
| Execution trick | DLL search order hijacking via index.exe loading malicious DismCore.dll |
| Persistence | Startup folder LNK and files under %APPDATA% |
| Exfiltration path | Compromised FTP servers tied to Taiwanese printing companies |
What organizations should do now
- Tighten email filtering and isolate password-protected archives from unexpected senders. Talos and CISA both point to phishing as the first stage worth blocking early.
- Hunt for suspicious LNK execution, unexpected binaries under
%APPDATA%, and DLL sideloading behavior involving trusted executables. - Review exposed FTP credentials and remove any public credential disclosure immediately. Talos tied this campaign to compromised FTP infrastructure used for exfiltration and payload retrieval.
- Deploy Cisco Talos detection content, including the IOCs and Snort rules published for LucidRook and LucidPan.
- Train users to distrust branded security tools that arrive through email links instead of official vendor channels.
FAQ
LucidRook is a newly documented malware family that Cisco Talos says targeted organizations in Taiwan through spearphishing and a fake security software lure. Talos describes it as a Lua-based stager with Rust components and layered obfuscation.
Cisco Talos says the campaign targeted Taiwanese non-governmental organizations and suspected universities. The Traditional Chinese lures and government-themed decoys support that assessment.
The victim opens a password-protected archive, launches a disguised shortcut, and triggers a legitimate executable that sideloads a malicious DLL. Microsoft’s DLL security guidance explains how this kind of attack works when software loads DLLs from unsafe paths.
Trusted security branding lowers suspicion. In this case, Talos says the attackers copied the icon and name of a Trend Micro product to make the dropper look routine.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages