New phishing attack via Google Storage deploys Remcos RAT
A newly documented phishing campaign is using Google Cloud Storage links to help deliver Remcos RAT, a remote access trojan that gives attackers long-term control over infected Windows systems. The main trick is simple: the lure starts on a trusted Google-owned domain, which can make the link look safer to users and sometimes harder for basic filters to flag.
That does not mean Google itself was hacked. Instead, attackers appear to be abusing legitimate cloud infrastructure to host or route victims through malicious content, a tactic security researchers have tracked in several phishing campaigns this year. Google’s own cloud documentation acknowledges that abuse and misuse can occur on Google Cloud and provides a process for reporting it.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The malware at the end of the chain is Remcos RAT, a commercially sold remote administration tool that threat actors have repeatedly repurposed for surveillance, credential theft, and persistent remote access. ANY.RUN describes Remcos as an actively maintained malware family that remains widely used in unauthorized intrusions.
How the phishing chain works
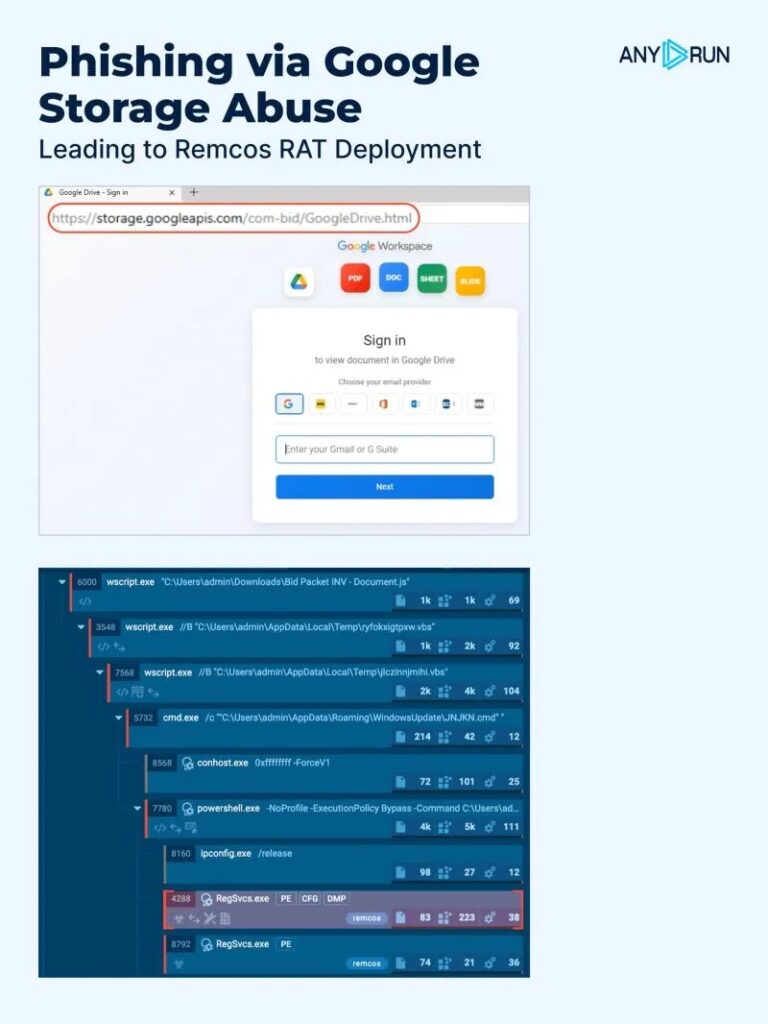
According to reporting on the campaign, the attack begins with a phishing email that links to a page hosted under storage.googleapis.com, Google Cloud Storage’s domain. Researchers say the page imitates a Google Drive sharing screen to make the victim think they are opening a familiar cloud document.
After the victim clicks, the flow moves into a multi-stage infection chain. The campaign reportedly uses a JavaScript redirect or automatic download to fetch an archive from attacker-controlled infrastructure, then relies on Windows scripting tools such as VBScript or PowerShell to continue the infection. That technique fits a broader Remcos trend seen in recent 2026 campaigns, where operators hide behind scripts, trusted binaries, and multi-stage loaders.
ANY.RUN’s recent Remcos reporting also shows the malware still appears in active live samples and sandbox runs in April 2026, which supports the view that Remcos remains a current threat rather than an aging one.
What attackers gain with Remcos
Once Remcos runs, the attacker can do far more than just collect a few files. ANY.RUN says the malware supports remote actions on infected machines and has long been associated with surveillance-style capabilities.
In many campaigns, Remcos operators use the malware to log keystrokes, capture screens, manage files, and maintain command-and-control access after the first compromise. Independent reporting on recent Remcos chains also notes process hollowing, obfuscated scripting, and persistence mechanisms designed to reduce detection by traditional file-based tools.
The bigger issue here is trust abuse. When attackers use a well-known cloud provider domain as the first visible step, users may lower their guard, and security teams may need stronger content inspection and behavioral detection to spot the real payload later in the chain.
Why trusted cloud domains keep showing up in phishing
Trusted infrastructure gives attackers a big advantage. Campaigns hosted on well-known domains can blend into normal traffic, especially when they imitate common services like Google Drive, document sharing, or cloud storage notifications. Recent phishing activity abusing Google-owned services has shown the same pattern across credential theft and malware delivery campaigns.
This does not point to a flaw in Google Cloud Storage itself. It points to a delivery tactic that relies on reputation and user familiarity. Google’s abuse documentation makes clear that cloud services can be misused and that abuse reports should be submitted when malicious content appears on hosted infrastructure.
For defenders, that means domain reputation alone is no longer enough. A googleapis.com link may still require scrutiny if it appears unexpectedly, arrives through phishing, or leads to content outside normal business workflows.
Remcos campaign at a glance
| Item | Verified detail |
|---|---|
| Initial lure | Phishing email |
| First visible host | Google Cloud Storage / googleapis.com |
| Impersonated service | Google Drive style document-sharing page |
| Delivery style | Multi-stage loader chain |
| Common execution tools | JavaScript, VBScript, PowerShell |
| Final malware | Remcos RAT |
| Likely impact | Remote control, surveillance, credential theft, persistence |
What security teams should do now
- Inspect unexpected Google Cloud Storage links, especially when they arrive through email and imitate shared documents.
- Enforce script control policies for VBScript and PowerShell where possible, since recent Remcos chains rely heavily on those tools.
- Use behavioral endpoint detection, not just domain or file reputation, because Remcos campaigns often use trusted infrastructure and multi-stage execution.
- Train users to verify unexpected shared-file emails through another channel before clicking. CISA says phishing remains a major path for malware delivery and credential theft.
- Report malicious content hosted on Google Cloud through Google’s abuse reporting channels if you identify active campaign infrastructure.
FAQ
Remcos is a remote administration tool that attackers often weaponize for unauthorized access, surveillance, and data theft. ANY.RUN describes it as an actively maintained malware family still widely used in real-world attacks.
There is no evidence in the reporting that Google itself was compromised. The campaign appears to abuse legitimate Google Cloud Storage hosting to make malicious links look more trustworthy.
Because the attacker uses a real Google-owned domain as the first step. That can make the lure appear legitimate and may reduce suspicion from both users and some basic filtering systems.
Disconnect the affected machine from the network, run an endpoint scan, review script execution logs, rotate credentials, and treat the event as a likely malware incident. This response follows standard phishing and malware guidance from CISA and the observed behavior of recent Remcos chains.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages