Microsoft locks VeraCrypt and WireGuard out of Windows signing, stalling critical updates

Microsoft has suspended developer access tied to VeraCrypt and WireGuard, leaving both projects unable to sign Windows drivers and ship new Windows builds. For users, the immediate risk is simple: if either project needs to push an urgent fix, the update path on Windows is blocked until Microsoft restores access or provides another route.
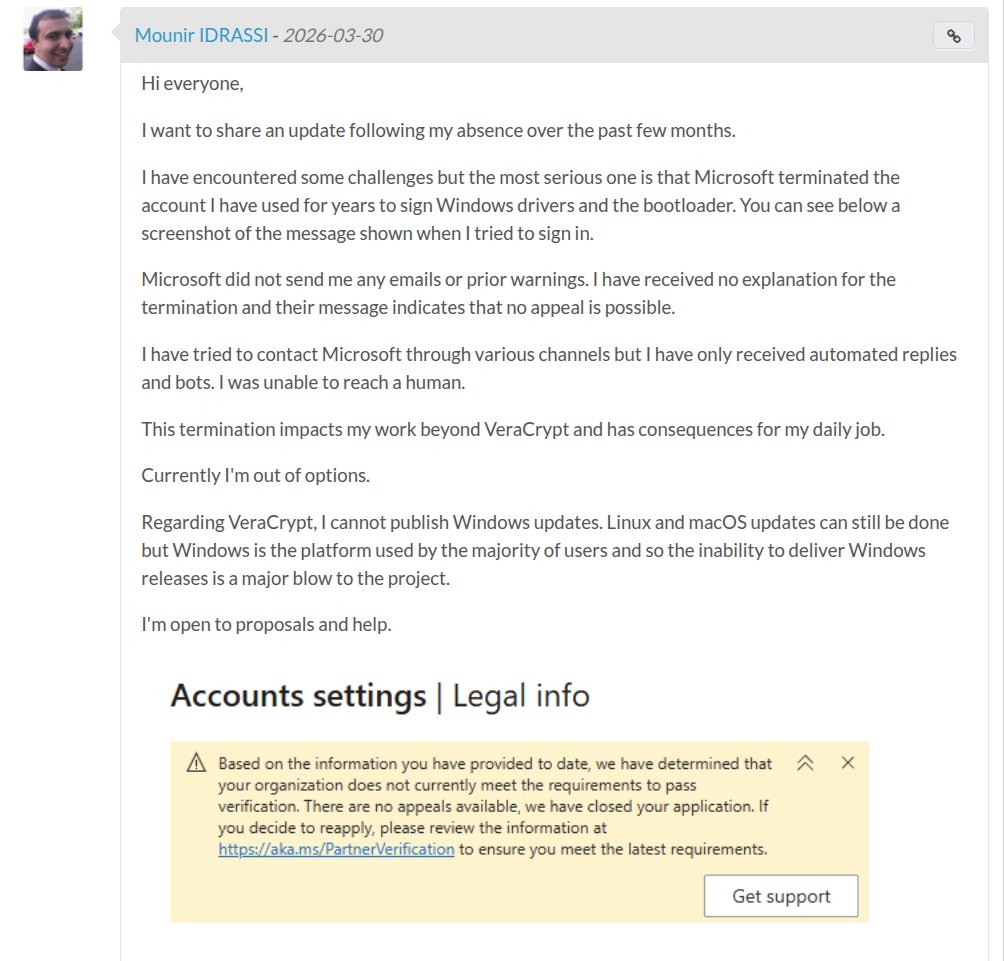
VeraCrypt developer Mounir Idrassi said Microsoft terminated the account he had used for years to sign Windows drivers and the bootloader. He said he received no warning emails and no clear explanation, and added that repeated attempts to reach support only led to automated replies.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
WireGuard creator Jason Donenfeld reported a similar lockout. He said the suspension stopped a Windows release from shipping and warned that a future security emergency could leave him unable to deliver a fix to users who depend on signed Windows drivers.
Why this matters for Windows users
This is not a minor account issue. Windows driver distribution depends on Microsoft’s signing and hardware submission pipeline, and Microsoft’s own documentation shows that developers must register through the Windows Hardware Developer Program and meet Partner Center requirements to submit and certify drivers. When that access breaks, new signed builds stop moving.
VeraCrypt faces a bigger deadline than a delayed feature update. Idrassi said users who rely on VeraCrypt system encryption could hit boot issues later in 2026 because Microsoft plans to revoke the older certificate authority used to sign the VeraCrypt bootloader, which means a newer Microsoft-signed bootloader becomes necessary.
The broader concern is supply-chain fragility. Two well-known open-source security tools, both trusted by privacy-focused users and organizations, ended up stuck behind account controls that appear to have changed faster than Microsoft’s support and notification process could handle. That creates real exposure even when the software itself has no known flaw.
What likely triggered the suspensions
Microsoft has not published a detailed public explanation for these individual cases, but the timing lines up with Partner Center security changes that rolled out in late 2025 and early 2026. Microsoft announced mandatory MFA for all Partner Center pages, with API enforcement starting April 1, 2026, and warned partners to adopt the changes promptly to avoid disruptions.
Microsoft’s own support replies also point affected developers to Partner Center legal and verification status pages, where pending or rejected verification can restrict hardware access. In other words, the likely trigger was not a malware finding against VeraCrypt or WireGuard, but an identity or compliance issue inside Partner Center’s verification flow. That remains an inference based on Microsoft’s published policy timeline and support guidance, not a confirmed cause from Microsoft for these exact accounts.
What developers object to most is the way this unfolded. Idrassi said he saw no warning and no meaningful human support path, while Donenfeld described a 60-day appeals process that makes little sense for security software that may need to ship an emergency fix fast.
Snapshot of the issue
| Project | What was blocked | Immediate impact | Bigger risk |
|---|---|---|---|
| VeraCrypt | Driver and bootloader signing path | No new Windows releases | System-encryption users could face boot issues once older signing trust is revoked later in 2026 |
| WireGuard for Windows | Driver signing and Windows update delivery | Planned Windows update stalled | Security fix delivery could fail during a future urgent vulnerability |
| Partner Center ecosystem | Account access tied to verification and MFA rules | Developers get locked out of hardware workflows | Critical open-source tools depend on one vendor-controlled release gate |
Facts in the table above reflect developer statements, Microsoft documentation, and current reporting available on April 9, 2026.
Microsoft has now responded
The story drew attention inside Microsoft after developers and media pushed it into public view. VeraCrypt’s SourceForge thread shows that Scott Hanselman contacted Idrassi directly, and later updates from media reports say Microsoft acknowledged the issue and started working to restore affected accounts.
That is the good news. The bad news is that this response appears to have come only after public escalation. The episode still raises a hard question for the Windows ecosystem: should critical security tools depend on a process where developers may lose release access first and get human help only after public pressure builds?
For now, users do not need to panic, and there is no sign that VeraCrypt or WireGuard themselves were compromised. The real problem sits in the update pipeline. Until Microsoft fully restores access, Windows users remain dependent on a blocked signing chain for future releases.
Key takeaways
- Microsoft account controls, not software flaws, appear to have stopped new Windows releases for VeraCrypt and WireGuard.
- Microsoft’s Partner Center changes make MFA and verification compliance essential for continued access.
- VeraCrypt faces a time-sensitive bootloader signing issue later in 2026 if the lockout continues.
- Microsoft says it is working on fixes, but the incident exposed weak communication and slow escalation paths.
FAQ
No public evidence shows that Microsoft banned the projects themselves. The available evidence points to developer account suspension or verification failure inside Partner Center, which still blocks Windows release signing in practice.
Yes, existing signed builds continue to work. The bigger issue affects future updates, especially if a security fix or bootloader refresh becomes necessary.
On Windows, signed drivers and related submission workflows help prove software origin and let the OS load kernel-level components safely. Without that signing path, developers cannot deliver normal Windows releases to end users.
Yes, current reporting says Microsoft has acknowledged the issue and is working to restore the affected accounts. VeraCrypt’s developer also said he had seen positive signs after Microsoft VP Scott Hanselman reached out.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages