New VENOM phishing kit targets CEOs and CFOs with Microsoft login theft

A newly documented phishing platform called VENOM is targeting senior executives with attacks designed to steal Microsoft 365 credentials and session access, even when multi-factor authentication is enabled. Abnormal Security says the operation has been active since at least November 2025 and focuses on high-value roles such as CEOs, CFOs, and vice presidents.
The campaign stands out because it does not rely on a simple fake login page alone. Abnormal says VENOM uses highly tailored phishing emails, QR codes rendered in Unicode, filtering pages that try to block researchers and sandboxes, and live adversary-in-the-middle login theft that captures credentials, MFA input, and session tokens.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
That matters because Microsoft has repeatedly warned that both adversary-in-the-middle phishing and device code phishing can bypass traditional MFA protections and give attackers persistent access through stolen tokens. In other words, executives can still lose control of their accounts even when passwords change later.
How the VENOM attack works
Abnormal says the phishing emails impersonate Microsoft SharePoint document-sharing notifications and are crafted to look like internal business communication. The messages include fake email threads and random HTML clutter to look more convincing and to make automated analysis harder.
Instead of sending a standard clickable phishing link, VENOM includes a QR code rendered with Unicode characters. Abnormal says that trick helps the attackers evade some scanning tools and pushes the victim onto a mobile device, where visual cues and browser protections may be weaker.
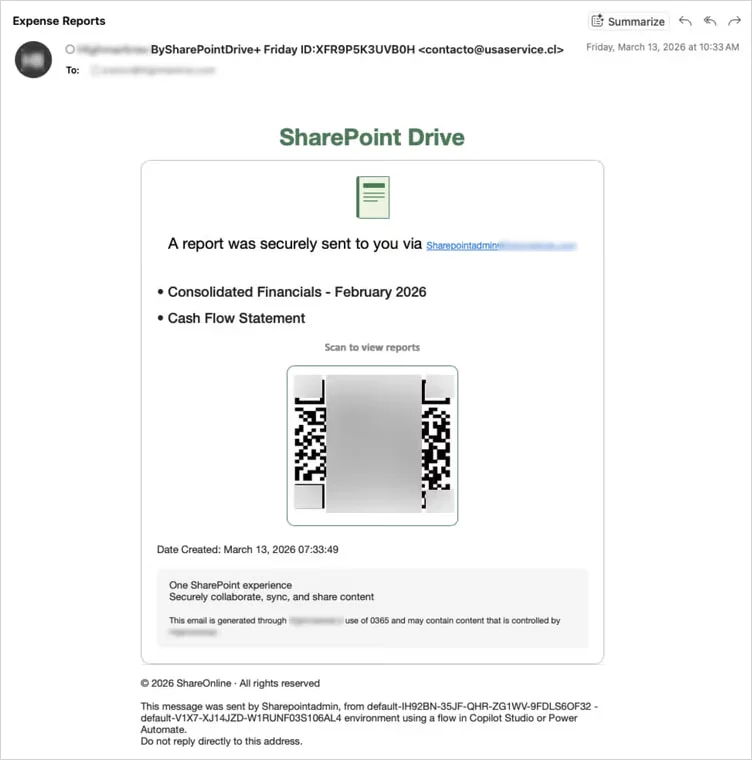
Source: Abnormal
The phishing URL also hides the target’s email address in the URL fragment after the hash symbol. Abnormal says fragments are not sent in normal HTTP requests, which can keep the victim’s address out of server-side logs and reputation systems.
Why executives are the main target
Abnormal describes VENOM as a closed-access phishing-as-a-service platform, not one openly advertised on common criminal forums. That suggests a more controlled operation aimed at high-value targets rather than mass phishing at scale.
The attackers appear to care most about access, not just passwords. In the AiTM flow, Abnormal says VENOM proxies a real Microsoft login process in real time, relays credentials and MFA codes to Microsoft APIs, and captures the resulting authenticated session.
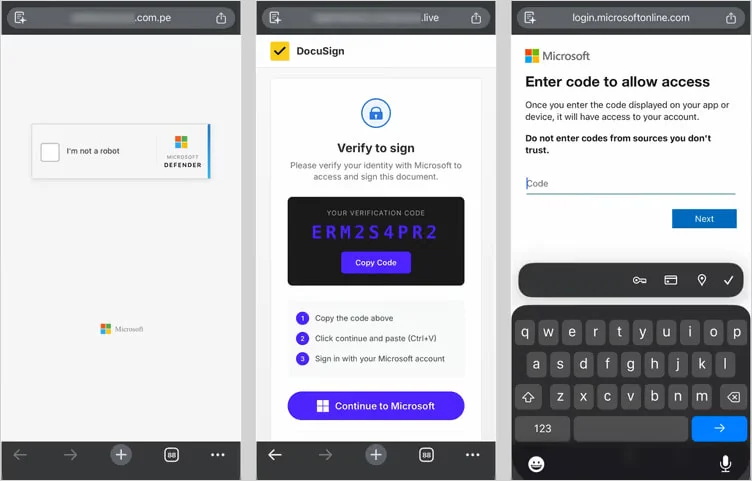
Source: Abnormal
Microsoft’s own guidance helps explain why this is dangerous for leadership teams. The company says adversary-in-the-middle phishing can intercept authentication traffic and bypass MFA, while device code phishing can capture access and refresh tokens that allow continued access to email and other cloud services.
VENOM also uses device-code phishing
Abnormal says VENOM does not stick to one method. In addition to AiTM phishing, the platform also uses device-code phishing, where a victim is tricked into approving Microsoft account access for an attacker-controlled device or application.
Microsoft has already described device-code phishing as a growing tactic in real-world attacks. In its February 2025 report on Storm-2372, Microsoft said attackers used fake meeting or messaging lures to get victims to complete a device code flow, which then handed over tokens instead of just passwords.
Microsoft’s broader identity-threat guidance says device-code phishing has spread across multiple threat actors because it resists some traditional defenses and can remain effective even after a user resets a password.
VENOM phishing campaign at a glance
| Item | Details |
|---|---|
| Platform name | VENOM |
| Reported by | Abnormal Security |
| Target roles | CEOs, CFOs, VPs, other senior executives |
| Main lure | Fake Microsoft SharePoint document-sharing emails |
| Delivery trick | Unicode QR codes and personalized phishing threads |
| Main techniques | Adversary-in-the-middle phishing and device-code phishing |
| Goal | Capture Microsoft credentials, MFA input, tokens, and persistent access |
Source: Abnormal Security analysis and Microsoft identity-security guidance.
What defenders should do now
- Move high-risk users to phishing-resistant authentication such as FIDO2 security keys or passkeys where possible. Microsoft and CISA both recommend phishing-resistant MFA against modern token-stealing attacks.
- Review whether device code flow is needed in your environment and disable or restrict it where it is not required. Microsoft specifically calls out device code abuse as a growing threat.
- Tighten conditional access and token-protection controls for executive accounts, especially around new device registration and risky sign-ins. Microsoft says attackers use stolen tokens for durable access beyond the original phish.
- Expand logging and monitoring in Microsoft 365 and Entra ID so teams can spot suspicious token use, rogue device registration, and anomalous sign-in behavior. CISA has published guidance on operationalizing expanded Microsoft cloud logs for this reason.
FAQ
VENOM is a phishing-as-a-service platform documented by Abnormal Security that targets senior executives and steals Microsoft account access through AiTM phishing and device-code phishing.
MFA still helps against many attacks, but Abnormal and Microsoft both say AiTM and device-code phishing can bypass or neutralize normal MFA flows by stealing tokens or relaying the authentication process live.
Abnormal says the QR code trick helps bypass some email-scanning controls and moves the victim to a mobile device, which can make the phishing flow harder to inspect.
Executive accounts often hold sensitive mail, approvals, deal discussions, and financial access. Abnormal says VENOM specifically targets C-suite roles, which suggests the operators want high-value cloud access rather than random account volume.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages