New LucidRook malware targets NGOs and universities in Taiwan

Cisco Talos says a newly identified malware family called LucidRook is being used in targeted attacks against Taiwanese non-governmental organizations and suspected universities. The company says it observed the campaign in October 2025 and linked it to a threat cluster it tracks as UAT-10362.
The attacks appear to be highly targeted rather than broad spam. Talos says the operators used spear-phishing emails, password-protected archives, decoy documents, and tailored infection chains built for Traditional Chinese language environments associated with Taiwan.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What makes LucidRook stand out is not just the target list. Talos says the malware acts as a modular Lua-based stager that can pull in and run additional payloads, which gives attackers a flexible way to adjust behavior after the initial compromise.
How the campaign works
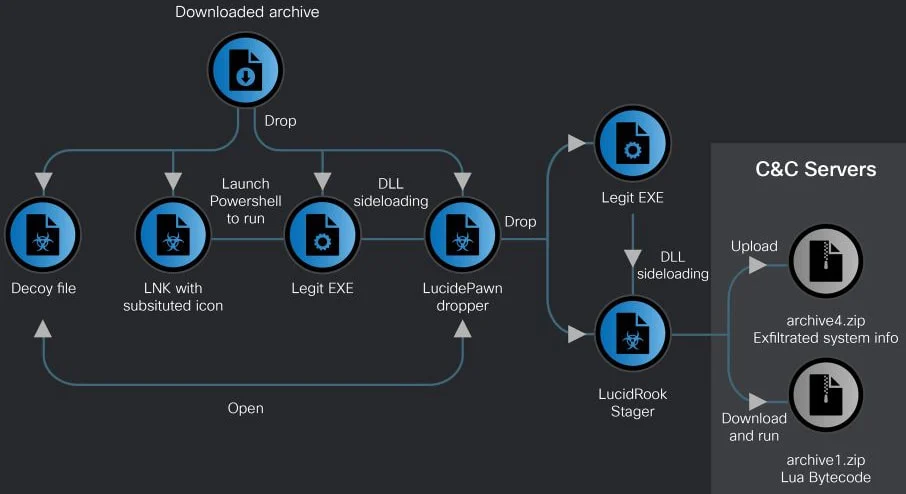
Cisco Talos says the phishing emails contained shortened links that led victims to encrypted RAR archives, with the password included in the email body. From there, the campaign used two separate delivery paths, one built around a malicious LNK file and another built around a fake executable disguised as security software.
In the LNK-based chain, Talos says the attackers used a shortcut file with a substituted PDF icon and a hidden folder structure designed to evade analysis. When clicked, the file launched a PowerShell component and then abused a legitimate DISM-related executable to sideload the LucidPawn dropper and, later, the LucidRook stager.
Talos says the malware also opened decoy files to distract the victim. One example was a document made to look like an official Taiwanese government notice to universities about travel approvals for trips to China.
Why LucidRook matters
Talos describes LucidRook as a sophisticated stager embedded inside a DLL that includes a Lua interpreter and Rust-compiled libraries. That design lets attackers deliver second-stage Lua bytecode payloads without changing the core malware every time, which can make incident response and forensic reconstruction harder.
Source: Cisco Talos
Cisco says LucidRook also uses layered anti-analysis logic, multi-language modular design, and stealth-focused payload handling. Talos says those traits, combined with the use of public or compromised infrastructure, suggest UAT-10362 has mature operational tradecraft.
The campaign also included a related tool called LucidKnight. Talos says LucidKnight likely serves as a reconnaissance tool and can exfiltrate collected system information through Gmail, which points to a broader and more flexible toolkit than a single malware loader.
What the malware does after infection
Talos says LucidPawn decrypts and drops a legitimate executable renamed as msedge.exe along with a malicious DismCore.dll file that sideloads LucidRook. It then sets persistence with a startup shortcut, helping the malware survive reboots.
According to Talos, LucidRook collects system details such as user and computer names, installed applications, and running processes. The report says the collected data is encrypted with RSA, packaged in password-protected archives, and sent to attacker-controlled infrastructure through FTP.
Talos says it could not recover a decryptable second-stage Lua bytecode payload, so the full post-infection actions remain unknown. That leaves an important gap in public visibility, but the report still concludes with medium confidence that the activity was part of a targeted intrusion campaign.
LucidRook campaign at a glance
| Item | Details |
|---|---|
| Malware | LucidRook |
| Related tools | LucidPawn, LucidKnight |
| Tracked actor | UAT-10362 |
| Primary targets | Taiwanese NGOs and suspected universities |
| First observed attack window | October 2025 |
| Delivery methods | Spear-phishing, password-protected archives, malicious LNK and EXE files |
| Notable feature | Embedded Lua interpreter for staged payload delivery |
| Data theft method | Encrypted archives exfiltrated via FTP |
Source: Cisco Talos.
Defensive takeaways
- Treat password-protected archives from unexpected emails as high risk, especially if the password is included in the message body.
- Watch for malicious LNK files that use substituted icons and hidden nested directories to disguise malware.
- Monitor for suspicious use of DISM-related binaries, sideloading behavior, and startup shortcut persistence.
- Review network activity tied to unusual FTP exfiltration or suspicious Gmail-based data exfiltration patterns.
FAQ
LucidRook is a newly identified Lua-based malware stager that Cisco Talos says was used in targeted attacks against Taiwanese NGOs and suspected universities.
Cisco Talos attributes the activity to a cluster it tracks internally as UAT-10362 and says the actor shows mature operational tradecraft.
Talos says victims receive spear-phishing emails that lead to password-protected archives containing either a malicious LNK file or a fake executable that starts the infection chain.
Talos says LucidRook embeds a Lua interpreter and uses staged Lua bytecode payloads, which lets attackers change behavior after infection without rebuilding the core loader.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more


User forum
0 messages