APT37 uses Facebook, Telegram, and a trojanized PDF installer in a new targeted intrusion campaign

North Korea-linked threat group APT37 has launched a new targeted intrusion campaign that starts on Facebook, shifts to Telegram, and ends with a trojanized PDF installer that quietly compromises the victim. Genians Security Center says the operation relied on trust-building, pretexting, and a tampered Wondershare PDFelement installer to deliver malware without raising immediate suspicion.
The campaign stands out because it uses common platforms that many targets already trust. According to Genians, the attackers first approached victims through Facebook friend requests, then moved to Messenger, and later shifted the conversation to Telegram once they had built enough rapport.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The lure focused on military and weapons-related content. The attackers claimed they were sharing encrypted PDF files and told victims they needed a special viewer to open them, a classic pretexting move designed to make the malicious installer feel necessary rather than suspicious.
How the social-engineering chain worked
Genians says the attackers used two Facebook accounts, “richardmichael0828” and “johnsonsophia0414,” both created on November 10, 2025, with profile locations set to Pyongyang and Pyongsong. Those accounts were used to identify and screen targets before the attackers began one-on-one conversations.
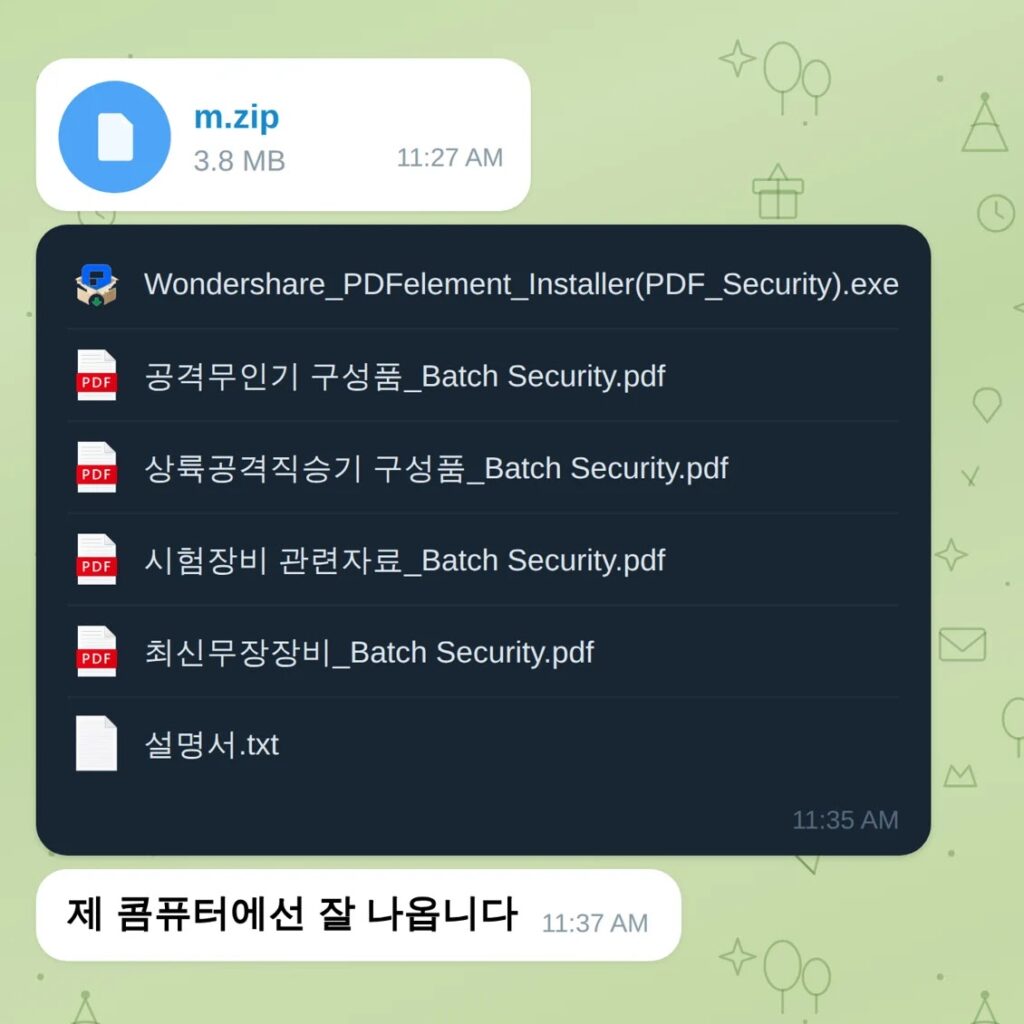
After the initial contact, the attackers gradually built trust through direct messages. Once the victim engaged, the conversation moved to Telegram, where the malicious files were delivered inside an encrypted archive along with a password shared separately.
Inside that archive, Genians found decoy PDF files, a fake guide, and a modified installer named “Wondershare_PDFelement_Installer(PDF_Security).exe.” The researchers say it closely resembled the official Wondershare installer but lacked a valid digital signature, a strong sign that the binary had been altered.
The installer looked normal, but the infection started immediately
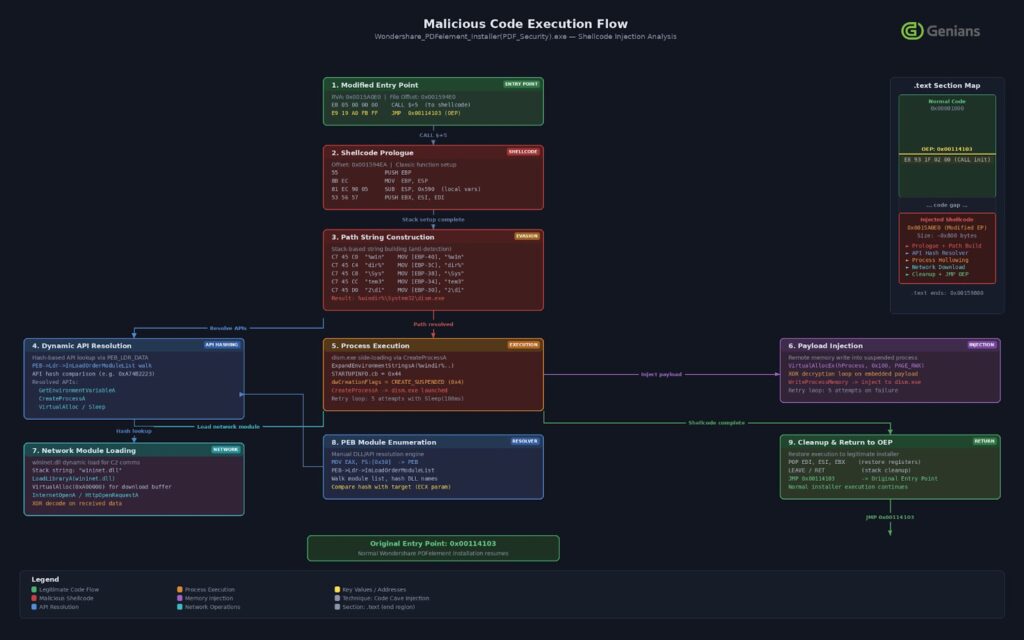
According to Genians, the attackers used PE patching, also called code-cave injection, to insert about 2 KB of shellcode into the installer’s .text section. The malware changed the program’s entry point so execution jumped to the malicious shellcode before returning to the normal installer flow.
That shellcode then created a suspended dism.exe process, decrypted the next-stage payload with a single-byte XOR key, and injected the code into memory with WriteProcessMemory before launching it with a remote thread. Genians says this let the attackers keep the early stages fileless and harder for traditional antivirus tools to catch.
After the malicious stages completed, the installer resumed normal PDFelement installation behavior. That meant the victim saw what looked like a standard software install, while the backdoor and follow-on components were already active in the background.
Command traffic hid behind legitimate-looking services
Genians says the malware contacted attacker-controlled infrastructure through the Seoul branch website of a Japanese real estate information service, which helped the traffic blend into routine browsing activity. The second-stage payload arrived disguised as a JPG image file retrieved from japanroom[.]com.
The researchers also say stolen data went out through Zoho WorkDrive using hardcoded OAuth2 tokens. The exfiltrated information reportedly included screenshots, documents such as DOC, XLS, PDF, and HWP files, plus audio recordings. Using a well-known cloud platform made the outbound traffic look less suspicious than a connection to an obviously malicious server.
The Hacker News, which summarized the same Genians research, says the malware delivered in this campaign was RokRAT, a malware family long associated with APT37 and known for espionage-focused collection and stealthy delivery. Genians’ public write-up focuses more heavily on the intrusion chain and delivery method than on a broad malware family profile, so the safest phrasing is that the campaign has been attributed to APT37 and publicly linked by follow-on reporting to RokRAT delivery.
Why this campaign matters
This campaign shows how much modern intrusion activity depends on patience and social engineering, not just malware. The attackers did not rely on spam blasts or crude phishing pages. They created believable personas, used trusted communication platforms, and wrapped the malware inside a familiar application flow.
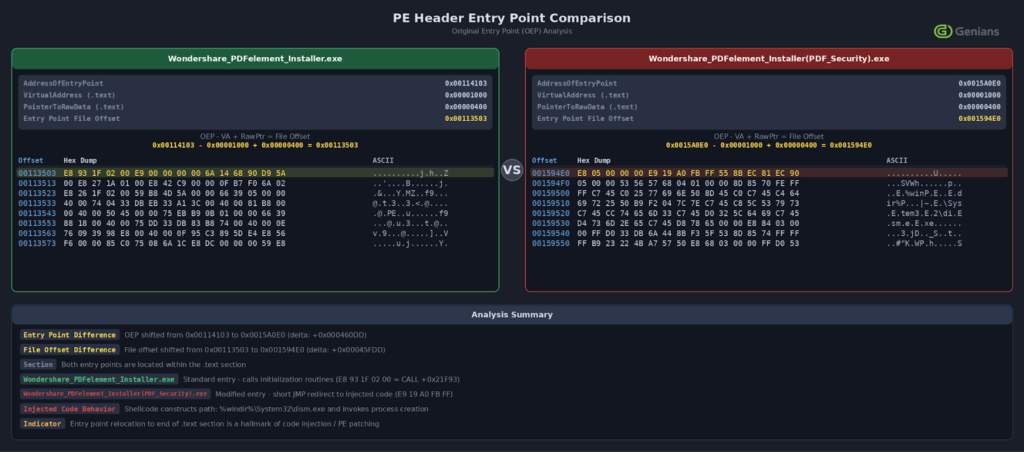
It also shows why signature checks still matter. Genians says the trojanized installer closely imitated the legitimate Wondershare PDFelement package, but the malicious file was not properly signed. A simple signature verification step could have raised a clear warning before execution.
For defenders, the technical lesson is just as important as the social one. A normal-looking installer that spawns dism.exe, injects shellcode, and starts cloud-bound exfiltration should never count as ordinary software behavior, even if the victim believes they are opening a trusted utility.
Key indicators and defensive priorities
| Area | What to watch |
|---|---|
| Social engineering | Unsolicited Facebook or Telegram conversations that shift toward sensitive subjects |
| Installer integrity | PDF or document viewer installers with modified names or missing signatures |
| Process behavior | Installers spawning dism.exe or other unexpected child processes |
| Payload delivery | JPG files or image paths used to deliver executable stages |
| Exfiltration | Unexpected Zoho WorkDrive activity, especially from sensitive endpoints |
The table above reflects the behavior described by Genians in its campaign analysis.
What organizations should do now
- Verify digital signatures on all software installers before users run them.
- Block users from installing software received directly through chat or messaging platforms unless IT has approved it.
- Alert on installer processes that spawn
dism.exeor other unusual Windows binaries. - Monitor for outbound traffic to cloud storage services such as Zoho WorkDrive from endpoints that do not normally use them.
- Train staff on social-engineering approaches that begin on social media rather than through email.
FAQ
APT37, also known as ScarCruft, is a North Korean state-linked threat group associated with espionage-focused campaigns and social-engineering-heavy delivery methods.
It relied on long-form trust building through Facebook and Telegram before delivering a tampered installer, which made the infection chain look far more personal and believable than a normal phishing email.
No. Genians says it closely resembled the official PDFelement installer and completed a normal-looking installation flow after the malicious actions ran.
Signature validation, abnormal child-process behavior from installers, and suspicious cloud-storage exfiltration are the clearest places to start.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages