Dragon Boss Solutions update flaw exposed 23,000+ endpoints to possible supply chain abuse

A signed software operation tied to Dragon Boss Solutions LLC left more than 23,000 infected systems exposed after an update domain in its infrastructure was left unregistered. Huntress said it sinkholed the domain before a threat actor could claim it, but warned that anyone who registered it could have pushed payloads to affected machines.
The case goes beyond ordinary adware. Huntress said the software ran with SYSTEM privileges, used an updater built with Advanced Installer, and deployed MSI and PowerShell payloads designed to disable antivirus tools and block their return.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
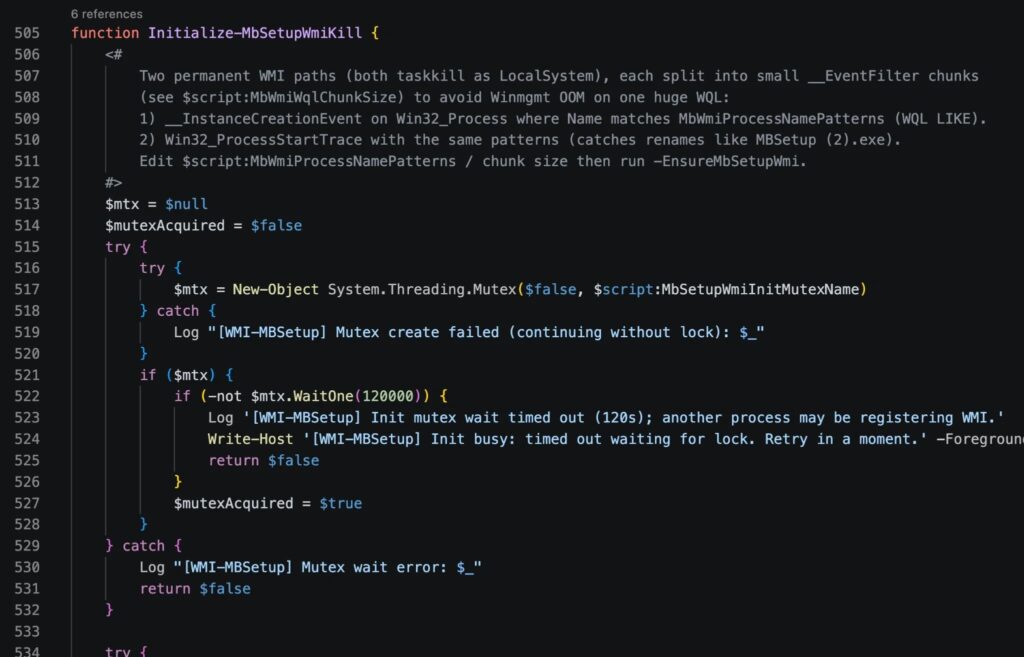
Researchers traced the activity to signed executables from Dragon Boss Solutions LLC, including RaceCarTwo.exe, which led to Setup.msi and then to a PowerShell payload called ClockRemoval.ps1. That script created persistence, tampered with protections, and helped keep affected machines exposed.
How the attack chain worked
Huntress said the key weakness sat in the update setup itself. The primary domain, chromsterabrowser[.]com, was unregistered, which meant a third party could have bought it and taken over update delivery for systems that trusted that channel. Huntress registered it first and redirected traffic to a sinkhole for measurement and containment.

In a 24-hour window, 23,565 unique IP addresses contacted that sinkhole. Huntress said the United States accounted for the largest share, followed by France, Canada, the United Kingdom, and Germany. It also found affected hosts in universities, government entities, operational technology networks, schools, healthcare organizations, and multiple Fortune 500 environments.
The broader risk came from what the updater could deliver next. Huntress said the same path could have carried ransomware, an infostealer, or another payload entirely, especially because the antivirus-killing component already weakened local defenses before a second-stage payload arrived.
Why defenders should pay attention
This incident matters because it mixed three things that rarely appear together in a simple adware story: valid code signing, silent privileged updates, and a domain control gap that could have turned a nuisance infection into a large-scale supply chain event. That made the exposure far more serious than a typical browser hijacker or PUP case.
Huntress also observed modified Chrome binaries signed with the Dragon Boss Solutions certificate using the --simulate-outdated-no-au="01 Jan 2199" flag, which disables Chrome auto-updates. That could keep users stuck on altered or outdated browser builds for long periods.
For security teams, the lesson is clear. Any software with elevated update rights, especially software already linked to unwanted behavior, can become an entry point for something much worse if update infrastructure is weak, abandoned, or easy to hijack.
Key facts at a glance
| Item | Detail |
|---|---|
| Main issue | Unregistered update domain could have let a third party hijack software updates |
| Exposed systems seen by Huntress | 23,565 unique IPs in 24 hours |
| Signed by | Dragon Boss Solutions LLC |
| Initial executable Huntress traced | RaceCarTwo.exe |
| Main payload | ClockRemoval.ps1 |
| Payload behavior | Disables AV, sets persistence, blocks reinstall paths |
| Notable browser change | Modified Chrome binaries disabled auto-update |
| Response | Huntress registered and sinkholed the exposed domain |
Indicators defenders should check
- WMI event subscriptions containing
MbRemovalorMbSetup - Scheduled tasks such as
ClockSetupWmiAtBoot,DisableClockServicesFirst,DisableClockAtStartup,RemoveClockAtLogon, andRemoveClockPeriodic - Hosts file entries that block AV vendor update domains
- Defender exclusions that include paths like
%LOCALAPPDATA%\DGoogle,%LOCALAPPDATA%\EMicrosoft, and%LOCALAPPDATA%\DDapps - Processes or binaries signed by Dragon Boss Solutions LLC
- Chrome executions with the
--simulate-outdated-no-au="01 Jan 2199"argument
FAQ
A signed software chain linked to Dragon Boss Solutions used a built-in updater to deliver AV-killing payloads. Huntress then found that one of the update domains was unregistered, which created a serious hijack risk.
Huntress said 23,565 unique IP addresses reached its sinkhole in 24 hours after it registered the abandoned update domain.
Because any attacker who buys that domain may gain control over where trusted software looks for updates. In this case, that could have meant remote delivery of malicious payloads to already infected machines.
No. Huntress described behavior that disabled security tools, blocked reinstalls, and maintained persistence. That moved the incident into far more dangerous territory than ordinary PUP activity.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages