Leaked Windows Defender 0-Day Vulnerability Actively Exploited in Attacks
Leaked Windows Defender zero-days are already being used in real attacks, and two of them still do not have a Microsoft patch. Huntress said threat actors are exploiting BlueHammer, RedSun, and UnDefend in live environments, while Microsoft has only fixed BlueHammer so far through CVE-2026-33825.
The most important point for defenders is this: BlueHammer is patched, but RedSun and UnDefend remain open. That means organizations that installed the April 2026 security updates reduced one part of the risk, but they still need monitoring and hardening for the other two techniques.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
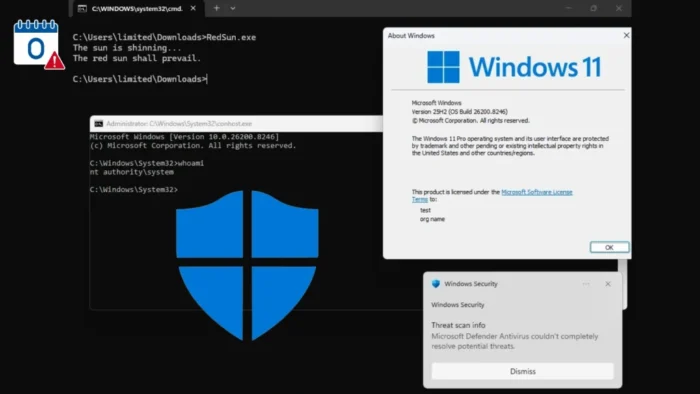
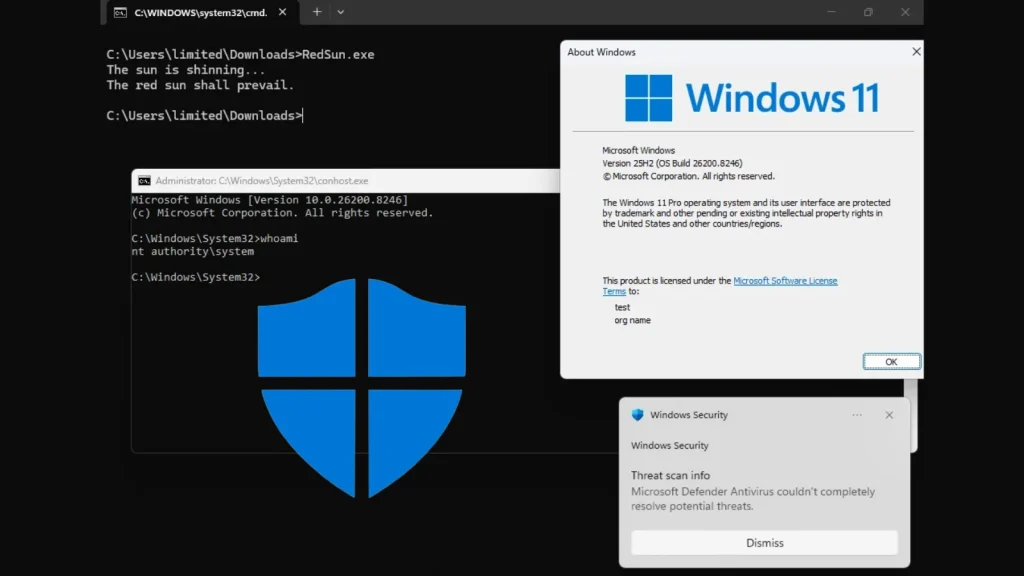
Huntress said the exploitation it observed did not look like random spray-and-pray abuse. The activity included binaries staged in low-privilege user folders, along with manual reconnaissance commands such as whoami /priv, cmdkey /list, and net group, which suggests hands-on-keyboard intrusion activity rather than simple automated testing.
What attackers are doing
BlueHammer is the only one of the three flaws that now has an official CVE and Microsoft patch. NVD describes CVE-2026-33825 as an elevation-of-privilege issue in Microsoft Defender that allows an authorized attacker to elevate privileges locally, with low privileges required and no user interaction.
Public reporting and researcher analysis describe BlueHammer as a local privilege escalation bug that abuses Defender’s privileged file operations rather than a kernel exploit. That matters because it lets an attacker move from a low-privilege account to SYSTEM by manipulating Defender’s remediation behavior, which makes it attractive after initial access has already been gained.
RedSun and UnDefend raise the pressure because Microsoft has not patched them yet. Huntress said it has seen all three exploitation techniques in the wild, and TechCrunch reported that Microsoft has only fixed BlueHammer so far.
Why RedSun and UnDefend matter more right now
RedSun is another local privilege escalation technique, but this one targets Defender’s real-time scanning and remediation path. Cyderes said the exploit works on Windows 10, Windows 11, and Windows Server 2019 and later, and can overwrite a system file by abusing Defender’s handling of flagged content.
UnDefend is different. Instead of giving SYSTEM access directly, it interferes with Defender’s update process and weakens the product’s ability to protect the host over time. That makes it a dangerous support tool for attackers who want to preserve access or reduce the chance of detection after landing on a machine.
Taken together, the three techniques create a practical attack chain. One exploit can raise privileges, another can do the same on systems the first one misses, and the third can degrade Defender’s protections while the attacker continues working inside the network. This is an inference based on Huntress’ observed activity and the technical descriptions of the three tools.
What Huntress saw in live incidents
Huntress said it saw binaries staged in user-writable directories, including Pictures folders and short subfolders inside Downloads, with names matching the public proof-of-concept tools such as FunnyApp.exe and RedSun.exe. In some cases, the binary had been renamed to z.exe, which shows attackers are already adjusting the public tooling for operational use.
The company also described detections tied to Defender’s own signatures and hunting rules. In one case, Defender quarantined BlueHammer as Exploit:Win32/DfndrPEBluHmrBZ, while another incident involved RedSun triggering an EICAR test-file alert and UnDefend running as Undef.exe with the -agressive argument.
Those details strengthen the case that this is not just online chatter around a leaked proof of concept. Huntress updated its blog on April 17 to note active threat activity involving BlueHammer, RedSun, and UnDefend, which puts the issue firmly in the category of real-world defender concern.
What organizations should do now
The first step is still patching Windows with the April 2026 security updates, because that closes BlueHammer. Microsoft added CVE-2026-33825 on April 14, and public guidance consistently says that patching removes the known fixable part of the current exposure.
The second step is hunting for execution from user-writable folders and suspicious recon commands. Huntress specifically called out executables launched from Pictures and Downloads paths, along with whoami /priv, cmdkey /list, and net group before or during exploitation attempts.
Security teams should also watch for EICAR drops by non-admin processes, odd Defender remediation behavior, and attempts to weaken Defender updates. Those signals matter more until Microsoft issues fixes for RedSun and UnDefend.
Key details at a glance
| Item | Details |
|---|---|
| Patched flaw | BlueHammer |
| CVE | CVE-2026-33825 |
| Patch status | Fixed in April 2026 updates |
| Unpatched flaws | RedSun and UnDefend |
| Exploitation status | Huntress says all three are being exploited in the wild |
| Main impact | Local privilege escalation to SYSTEM or degradation of Defender protection |
| Observed attacker behavior | Use of public PoC filenames, staging in user folders, manual recon commands |
FAQ
Yes. Microsoft fixed BlueHammer in the April 2026 security updates, and the issue is tracked as CVE-2026-33825.
Not yet, based on the public reporting and Huntress activity noted on April 17, 2026.
Yes. BlueHammer and RedSun are local privilege escalation techniques, which means an attacker needs a foothold on the machine first, even with low privileges.
Because local privilege escalation can turn a small foothold into full SYSTEM control. In enterprise attacks, that can be enough to dump credentials, install persistence, disable defenses, or pivot deeper into the network. This is an inference based on the vulnerability type and the recon activity Huntress described.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages