Windows Snipping Tool flaw can leak credentials over the network after one click

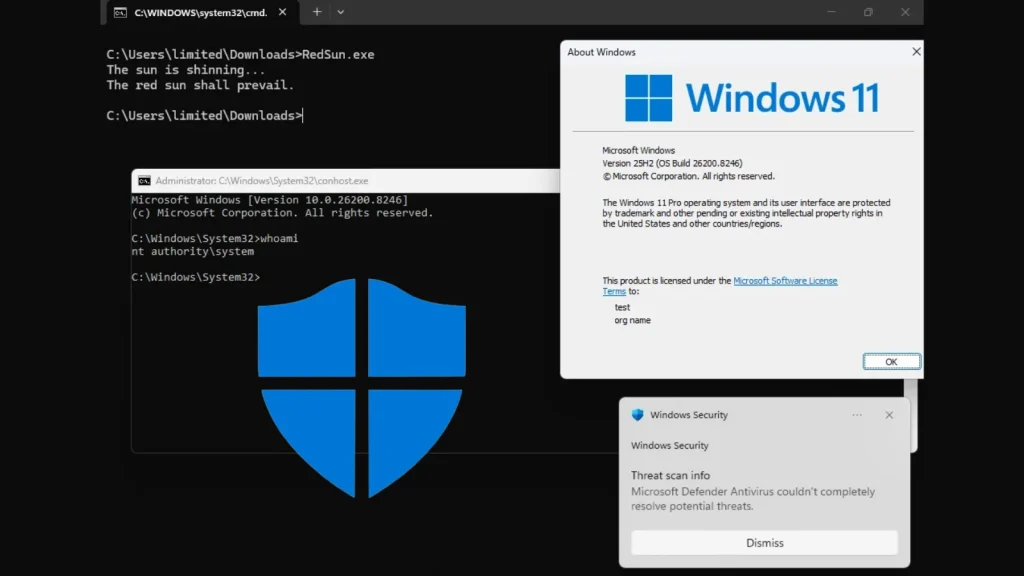
Microsoft has fixed a Windows Snipping Tool vulnerability that can expose a user’s authentication data over the network. The flaw, tracked as CVE-2026-33829, lets an attacker abuse the app’s deep-link handling so Snipping Tool reaches out to an attacker-controlled SMB server and leaks NTLM authentication material after the victim opens a crafted link.
The bug matters because Snipping Tool is a trusted Windows app, which makes the attack easier to disguise. A victim may see the tool open as expected while the credential leak happens in the background, giving the attacker a chance to capture the user’s Net-NTLM hash and use it in follow-on attacks.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Microsoft released the fix on April 14, 2026, as part of that month’s security updates. NVD lists the issue as medium severity with a CVSS 3.1 score of 4.3 and a vector that reflects network reachability, low attack complexity, and required user interaction.
How the Snipping Tool bug works
The vulnerability sits in the ms-screensketch URI scheme that Snipping Tool registers in Windows. BlackArrow’s disclosure says an attacker can abuse the filePath parameter to force an authenticated SMB connection to an arbitrary server because the app does not validate the supplied path well enough before making the request.
In practice, the trick is simple. An attacker sends a malicious link by email, chat, or a compromised webpage, the victim clicks it, Windows prompts to open Snipping Tool, and the app then tries to fetch the remote file over SMB. That outbound request can hand over the victim’s Net-NTLM hash without any obvious warning inside the app itself.
BlackArrow’s public proof of concept shows the exact attack path and even gives a sample ms-screensketch:edit link that points filePath to a remote SMB share. The researcher’s timeline says they reported the issue on March 23, 2026, and Microsoft shipped the fix on April 14, 2026.
Key details at a glance
| Item | Details |
|---|---|
| CVE | CVE-2026-33829 |
| Component | Windows Snipping Tool |
| Issue type | Spoofing over a network / exposure of sensitive information |
| Severity | Medium |
| CVSS 3.1 | 4.3 |
| User interaction | Required |
| Patch date | April 14, 2026 |
| Main risk | Leak of NTLM authentication material to an attacker-controlled SMB server |
The affected configurations published through NVD span multiple Windows 10 and Windows 11 branches, including Windows 10 1607, 1809, 21H2, and 22H2, plus Windows 11 23H2, 24H2, 25H2, and 26H1. The same record also lists older Windows Server branches, including Windows Server 2012 and 2012 R2.
NVD’s change record also shows the patched build cutoffs for several client branches, including Windows 10 22H2 up to but excluding build 10.0.19045.7184, Windows 11 23H2 up to but excluding 10.0.22631.6936, Windows 11 24H2 up to but excluding 10.0.26100.8246, and Windows 11 25H2 up to but excluding 10.0.26200.8246. That gives admins a quick way to verify whether a system still sits in the vulnerable range.
What admins and users should do now
The first step is obvious: install Microsoft’s April 2026 security updates on affected systems. If your environment still allows outbound SMB traffic to the internet, close that path at the perimeter because that is what makes this kind of hash-leak attack useful in the first place.
Security teams should also treat unexpected Snipping Tool launch prompts as suspicious, especially when they come from browser links or messages that claim a user needs to edit or crop an image. This bug does not need a complex exploit chain. It needs a believable pretext and one click.
Recommended actions
- Install the April 14, 2026 Microsoft security updates on all affected Windows systems.
- Block outbound SMB traffic, especially TCP port 445, at internet-facing boundaries.
- Warn users not to approve unexpected prompts that launch Snipping Tool from a browser or message.
- Review exposed systems against the build cutoffs listed in NVD’s affected configuration data.
FAQ
It is a Windows Snipping Tool vulnerability that can leak NTLM authentication data over the network when a victim opens a crafted link.
Yes. The victim must open a malicious link or page that triggers Snipping Tool through the ms-screensketch URI scheme.
The public disclosures describe credential leakage and spoofing risk, not direct code execution or system takeover by Snipping Tool alone. Attackers would need to chain the stolen authentication material into later steps.
Yes. Microsoft released a fix on April 14, 2026.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages