Microsoft says Jasper Sleet uses fake IT worker identities to infiltrate cloud environments
Microsoft has warned that Jasper Sleet, a North Korea-aligned threat actor, is using fake IT worker identities to get hired into real companies and gain trusted access to cloud environments. According to Microsoft Threat Intelligence, the group abuses remote hiring, digital onboarding, and cloud-connected business tools to move inside organizations without relying on a traditional network intrusion.
The campaign turns the hiring process into a security problem. Microsoft says these operatives use stolen or fabricated identities, AI-assisted deception, and external infrastructure to pass screening, complete onboarding, and then access services such as Microsoft Teams, SharePoint, OneDrive, Exchange Online, and HR systems.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This matters because the threat can look like ordinary employment activity at first. Instead of breaking into a company from the outside, Jasper Sleet can enter through legitimate job offers, then operate with the permissions, devices, and collaboration tools a normal employee would receive.
How the fake worker scheme works
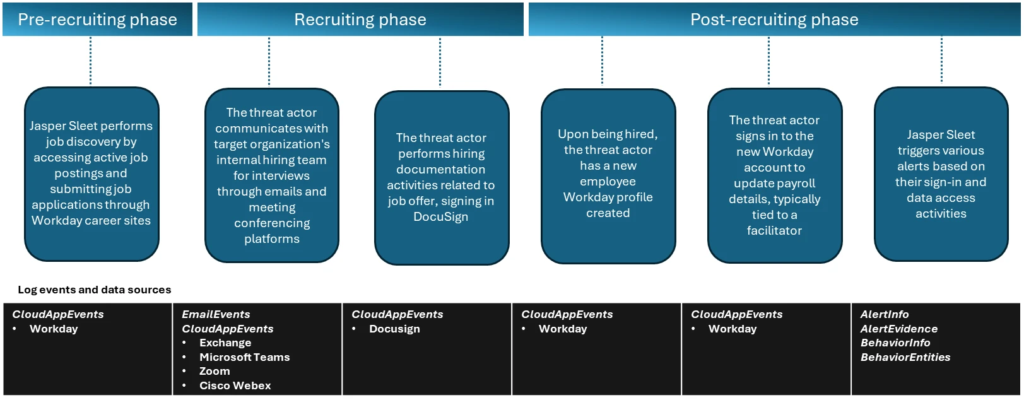
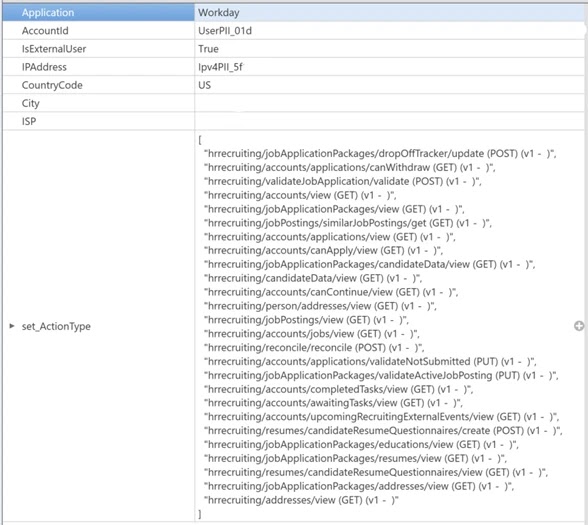
Microsoft says Jasper Sleet starts in the pre-recruitment phase by reviewing public job listings and external career portals, including organizations that use platforms such as Workday. The company says the actor has made programmatic calls to Workday Recruiting Web Services endpoints exposed through external career sites to gather information on job postings, applications, and questionnaires.
Microsoft also says the group uses generative AI to study role requirements and build more convincing fake personas. In earlier and related reporting, Microsoft described AI use for creating culturally plausible identities, generating polished resumes and profile photos, reducing language barriers, and helping operatives stay employed after they are hired.
During recruitment, the actor communicates through common business tools such as email, Microsoft Teams, Zoom, and Cisco Webex. Microsoft says the pattern becomes suspicious when multiple external accounts repeatedly access the same recruiting API endpoints or when newly created employee identities begin showing impossible-travel alerts and logins from known malicious infrastructure soon after onboarding.
What happens after the actor gets hired
Once inside, the threat shifts from deception to access abuse. Microsoft says Jasper Sleet signs into newly created enterprise accounts, updates payroll details, and begins working through internal cloud tools like a normal employee. That gives the actor a direct path to sensitive files, collaboration data, internal communication, and business workflows.
Microsoft has specifically highlighted sign-ins tied to new hires that originate from anonymous proxies or geographically inconsistent locations. It says spikes in impossible-travel alerts during the first months after onboarding can serve as an early warning that the identity behind the account is not genuine.
The risk does not stop at data access. Microsoft says these operations can support revenue generation for the North Korean regime and, in some cases, enable data theft, extortion, or follow-on compromise inside the victim organization.
Why cloud and HR platforms sit at the center
Microsoft’s report shows that this threat sits between HR, IT, and security. The actor abuses hiring software and external career portals before the organization even creates an internal account, then pivots into cloud productivity suites and enterprise workflows after onboarding.
That makes the problem broader than a standard phishing campaign. A fake applicant may pass through recruiters, interviewers, payroll staff, hiring managers, and IT onboarding teams before security teams see any alert. By then, the actor may already have a valid account, approved access, and enough business context to blend in.
Microsoft’s earlier Jasper Sleet reporting also shows that the group adapts over time. The company previously documented tactics such as fraudulent identities, facilitators, laptop farms, and AI-assisted communication, which suggests the fake-worker model has become more systematic and harder to spot with basic screening alone.
Jasper Sleet activity at a glance
| Area | Microsoft findings |
|---|---|
| Threat actor | Jasper Sleet, a North Korea-aligned actor |
| Main tactic | Posing as remote IT workers using fake or stolen identities |
| Entry point | External career portals and digital hiring workflows |
| Platform highlighted | Workday Recruiting Web Services endpoints |
| Post-hire access | Teams, SharePoint, OneDrive, Exchange Online, payroll systems |
| Key warning signs | Repeated API calls, suspicious external accounts, impossible-travel alerts, proxy use |
The details in the table come from Microsoft’s April 21, 2026 blog on detection strategies against infiltrating IT workers.
What organizations should do now
- Treat recruiting and onboarding as part of the security perimeter, not only an HR workflow.
- Review Workday and other external recruiting platform telemetry for repeated API access from unusual external accounts.
- Enable Microsoft Defender for Cloud Apps connectors for services such as Workday, DocuSign, Zoom, and Cisco Webex to improve visibility across the hiring chain.
- Investigate impossible-travel alerts, proxy-based access, and geographic anomalies tied to new hires.
- Train hiring teams to look for interview red flags such as inconsistent background details, reluctance to appear clearly on camera, or unusual urgency around payroll setup.
FAQ
Jasper Sleet is a North Korea-aligned threat actor that Microsoft has linked to fake remote IT worker operations and related cloud infiltration tactics.
Microsoft says the actor studies job postings, abuses external recruiting workflows, uses fake or stolen identities, completes hiring and onboarding steps, and then signs into internal cloud services as a legitimate employee.
Microsoft observed suspicious programmatic access to Workday Recruiting Web Services endpoints through external career sites, which helped the actor gather hiring-related information and refine applications.
Microsoft points to repeated API calls from external accounts, sign-ins from suspicious infrastructure, anonymous proxy usage, and impossible-travel alerts tied to newly hired employees.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages