Lotus Wiper destroys drives and deletes files in targeted attack on Venezuela’s energy sector

Lotus Wiper is a destructive malware strain, not ransomware. Kaspersky says it targeted an organization in Venezuela’s energy and utilities sector, where it wiped physical drives, deleted files across affected volumes, and removed recovery options, leaving systems in an unrecoverable state.
The malware appears highly targeted. Kaspersky says the artifacts were uploaded from a machine in Venezuela in mid-December 2025, while the malware itself was compiled in late September 2025, which suggests the attackers prepared the operation months before deployment.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Researchers did not find ransom notes, payment instructions, or any extortion mechanism in the code. That point matters because it places Lotus Wiper in the same destructive category as past wipers used to sabotage operations rather than earn money.
Why Lotus Wiper stands out
Kaspersky says the malware disguised itself as legitimate HCL Domino components using filenames such as nstats.exe, nevent.exe, and ndesign.exe. That choice suggests the attackers had already gained access to the victim environment and staged the malicious files before launching the wipe.
The timing also adds weight to the case. SecurityWeek, citing Kaspersky, says the attack surfaced during a period of heightened geopolitical tension in the Caribbean in late 2025 and early 2026, although Kaspersky did not publicly attribute the operation to a known threat actor.
In practical terms, Lotus Wiper aims to destroy both data and the paths that might restore it. Kaspersky says it removes recovery mechanisms, overwrites the contents of physical drives with zeros, and systematically deletes files across all affected volumes.
How the attack chain works
The infection chain begins with a batch file named OhSyncNow.bat, which acts as the trigger for the destructive sequence. According to Kaspersky, the script typically works from C:\lotus and tries to disable the legacy Interactive Services Detection service, UI0Detect, to reduce visible warnings that suspicious background activity is taking place.
That detail points to older Windows systems. Kaspersky notes that Microsoft removed UI0Detect beginning with Windows 10 version 1803, so the presence of code that targets the service suggests the attackers expected legacy machines in the victim environment.
The batch script also checks for a remote XML file named OHSync.xml on the domain’s NETLOGON share. If that file exists, it acts like a network-wide trigger and launches a second batch script, notesreg.bat, across systems in the domain.
What happens before the wipe
Kaspersky says notesreg.bat appears designed to run only once. It enumerates local user accounts, changes passwords to random strings, marks accounts inactive, disables cached logins, logs off active users, and shuts down network interfaces with netsh.
The preparation phase also abuses native Windows tools. The script uses diskpart clean all against logical drives, which overwrites disk contents with zeros, and Kaspersky observed the broader attack chain relying on built-in utilities to blend into normal administration activity.
After that, Lotus Wiper decrypts its own executable with XOR and begins the final destructive phase. Kaspersky says the malware enables administrative privileges, deletes Windows System Restore points through srclient.dll, fills sectors with zeros through low-level disk I/O controls, and creates a giant file with fsutil to consume remaining free space.
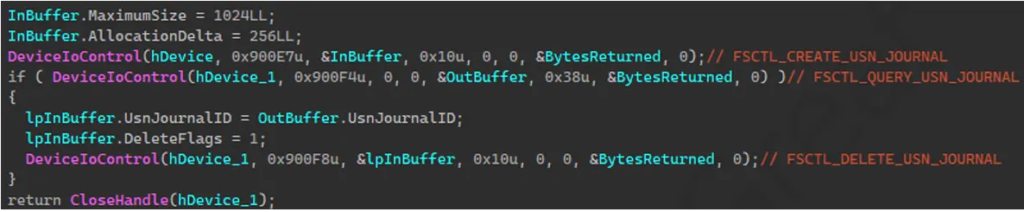
How Lotus Wiper destroys data
Once active, the malware does not just remove files from view. Kaspersky says it zeroes file content with FSCTL_SET_ZERO_DATA, renames files using random hexadecimal strings, and then deletes them, making recovery much harder.
If a file is locked and cannot be removed right away, Lotus Wiper uses MoveFileExW to schedule deletion on the next reboot. That extra step helps the malware finish cleanup even when processes keep files open during the initial attack window.
SecurityWeek’s summary of the Kaspersky report notes that the combined effect is severe: overwritten drives, erased recovery options, and systematic file destruction that can leave critical systems unusable after a single coordinated operation.
Lotus Wiper at a glance
| Detail | Verified information |
|---|---|
| Malware name | Lotus Wiper |
| Primary target | An organization in Venezuela’s energy and utilities sector |
| Main goal | Destruction, not extortion |
| Earliest compile time noted | Late September 2025 |
| Artifact upload noted | Mid-December 2025 from a machine in Venezuela |
| Key trigger | OHSync.xml on the NETLOGON share |
| Main tools abused | diskpart, fsutil, netsh, MoveFileExW, srclient.dll |
| Final effect | Wipes drives, deletes files, removes recovery paths |
The table reflects details reported by Kaspersky and summarized by follow-up coverage.
What defenders should watch for
- Unauthorized changes on domain shares, especially
NETLOGON, because the attack uses a remote XML flag file as a trigger. - Suspicious use of native tools such as
diskpart,fsutil,netsh, androbocopyin unusual sequences. - Signs of credential abuse, account deactivation, forced password changes, or token manipulation on legacy Windows systems.
- Attempts to clear recovery points or rapidly consume all free disk space.
- Any environment that still depends on older Windows features like
UI0Detect, since that may signal exposure to this attack chain.
FAQ
Lotus Wiper is a destructive malware strain that wipes drives, deletes files, and removes recovery mechanisms instead of demanding a ransom.
Kaspersky says the malware targeted an organization in Venezuela’s energy and utilities sector.
No. Researchers found no ransom note, no payment flow, and no extortion component in the malware.
The attack chain uses batch scripts and a trigger file on the domain NETLOGON share, which suggests the attackers already had access and staged the operation before launching it.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages