Hackers Abuse SS7 and Diameter Protocols to Track Mobile Users Worldwide

Sophisticated surveillance actors are abusing weaknesses in SS7 and Diameter, the signaling protocols that help mobile networks connect across borders, to track phone users without touching their devices. Citizen Lab says it identified two long-running campaigns that used global telecom infrastructure to locate targets and hide behind legitimate network entry points.
The investigation matters because these attacks can run almost invisibly from the user’s point of view. A target does not need to click a link, install an app, or answer a call. In some cases, the tracking request moves through telecom signaling systems that were designed to trust other operators.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
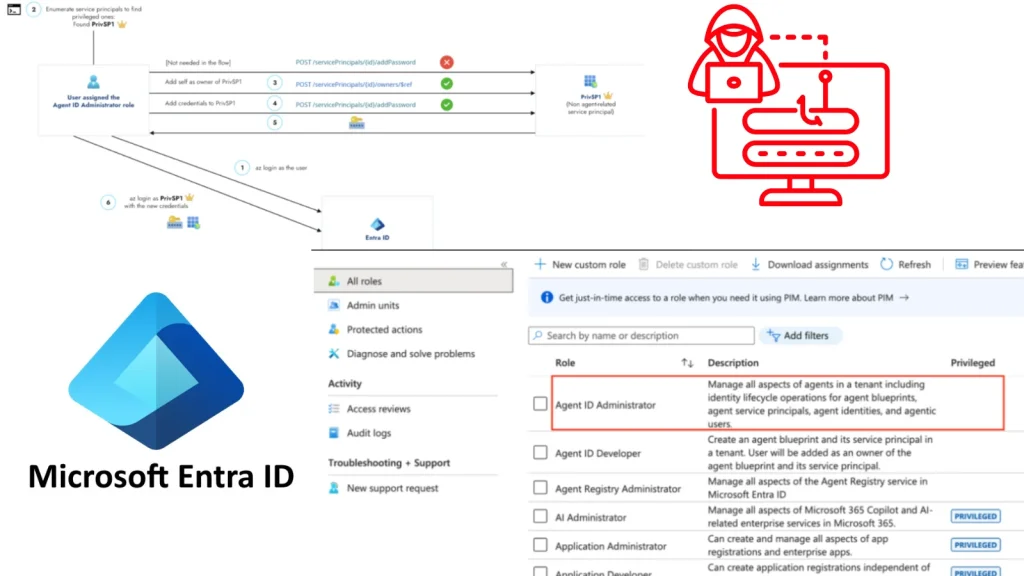
Citizen Lab named the two threat clusters STA1 and STA2. It did not publicly attribute them to a specific company, but said the evidence fits commercial telecom surveillance platforms that support government intelligence activity.
The attacks target the trust inside mobile networks
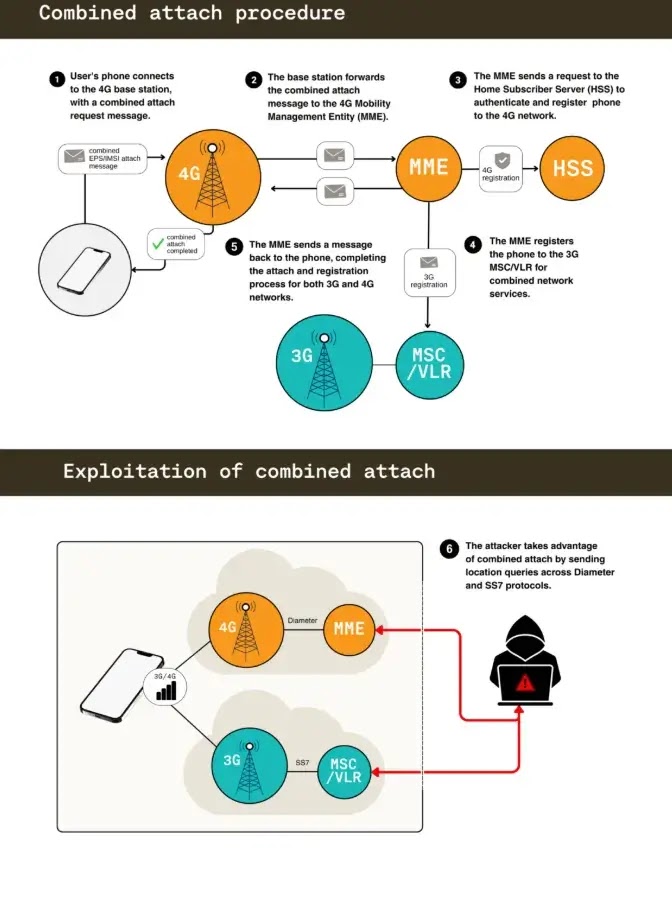
SS7 is used mainly in older 3G networks, while Diameter supports inter-operator signaling in 4G and most 5G networks. SS7 lacks strong authentication and encryption, and Citizen Lab says Diameter still has serious exposure because many operators have not implemented newer security protections properly.
The core problem is the global telecom interconnect system. More than a thousand mobile operators need to exchange signaling messages so phones can roam, receive texts, and connect across countries. That system was built around operator trust, but surveillance vendors can abuse access to look like legitimate carriers.
Citizen Lab says attackers can obtain indirect access through legitimate operators, third-party providers, commercial leasing arrangements, or intermediary services. Once inside, they can send tracking requests that appear to come from trusted networks.
How the SS7 and Diameter tracking works
| Protocol or method | Where it is used | How attackers abuse it |
|---|---|---|
| SS7 | Mainly 2G and 3G networks | Sends location queries through a trust-based signaling system |
| Diameter | 4G and most 5G signaling | Abuses weak or incomplete security implementations |
| Combined 3G and 4G registration | Roaming networks | Lets attackers move between protocol paths when one route fails |
| Hidden SIM commands | SIM Toolkit style attacks | Sends silent messages that can trigger location reporting |
| Third-party entry points | Interconnect and roaming providers | Helps surveillance actors mask the source of traffic |
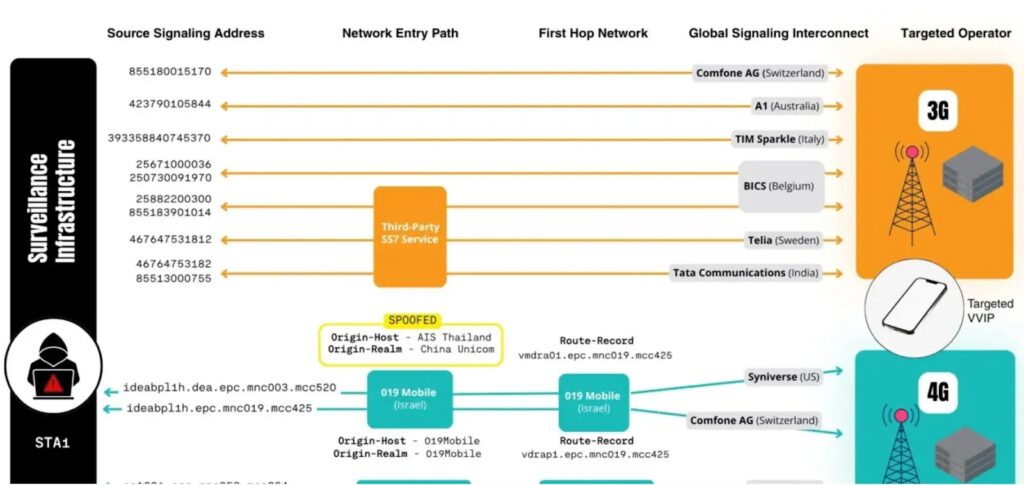
Citizen Lab found that STA1 relied on signaling routing manipulation. The actor used SS7 and Diameter paths, spoofed operator identities, and routed traffic through different network entry points to bypass defenses and hide attribution.
STA2 used a more direct device-linked method. Citizen Lab says this campaign sent malicious hidden SMS commands to a target’s SIM card, attempting to make the device collect and transmit location information without showing anything to the user.
STA1 used network spoofing to hide location tracking
Citizen Lab describes STA1 as a persistent and technically sophisticated telecom surveillance actor. The group showed a deep understanding of mobile signaling, roaming systems, and signaling firewall behavior.
STA1’s method focused on finding a working path through telecom defenses. If one protocol path failed, the actor could try another. This allowed the campaign to move between older SS7 weaknesses and newer Diameter signaling routes.
The report also says STA1 used several geographic entry points into the private signaling backbone. That matters because defenders may see traffic from legitimate-looking telecom identifiers rather than a clear malicious server.
STA2 used SIM messages as a tracking trigger
STA2 followed a different model. Instead of relying only on signaling queries inside the telecom backbone, it used hidden SMS messages aimed at the SIM card itself.
These messages do not appear like normal texts. They communicate with the SIM card and can carry commands that make the phone behave like a location tracking device. TechCrunch noted that this style of attack has been known for years under the SIMjacker label.
Citizen Lab says this kind of attack is entirely invisible to users. That makes personal detection almost impossible, especially when the target is a high-profile person rather than a broad population group.
The telecom providers named in the report
Citizen Lab found evidence pointing to platforms that leveraged operator networks based in Israel, the United Kingdom, and the Channel Islands. The report also says this does not automatically mean those operators knowingly participated in attacks. Access can come through third-party providers, leasing arrangements, or other intermediaries.
TechCrunch reported that the providers discussed in the research included Israeli operator 019Mobile, Tango Networks U.K., and Airtel Jersey, now owned by Sure. Citizen Lab linked these networks to surveillance entry or transit points inside the telecom ecosystem.
Sure CEO Alistair Beak told TechCrunch that Sure does not lease signaling access directly or knowingly to organizations for tracking individuals or intercepting communications content. He said the company monitors and blocks inappropriate signaling and suspends or terminates services when misuse is confirmed.
What Citizen Lab found
| Finding | Detail |
|---|---|
| Report name | Bad Connection |
| Publisher | Citizen Lab, University of Toronto |
| Publication date | April 23, 2026 |
| Threat clusters | STA1 and STA2 |
| Main protocols abused | SS7 and Diameter |
| Main purpose | Covert location tracking |
| Target profile | High-profile individuals, not general mass users |
| Attribution | Not publicly tied to a named company |
| Suspected model | Commercial telecom surveillance supporting government clients |
Citizen Lab said its investigation linked real-world attack traffic to mobile operator signaling infrastructure for the first time. That gives researchers a clearer view of how surveillance actors enter the global telecom ecosystem and use private operator networks to hide.
The report also found attack infrastructure associated with operators and identifiers across several countries, including the U.K., Israel, China, Thailand, Sweden, Italy, Liechtenstein, Cambodia, Mozambique, Uganda, Rwanda, Poland, Switzerland, Morocco, Namibia, Lesotho, and Jersey.
TechCrunch reported that Citizen Lab researcher Gary Miller said the evidence points to a deliberate and well-funded operation with deep integration into the mobile signaling ecosystem. He also said the two campaigns represent only a small part of the wider abuse seen globally.
Why ordinary users cannot easily detect this
Telecom-level surveillance does not look like ordinary phone hacking. It may not create a suspicious app, visible notification, strange message, or obvious login alert. The tracking can happen through signaling traffic exchanged between networks.
Citizen Lab says these campaigns usually target high-profile individuals and are not used for mass surveillance of regular users. The organization also said it has not identified cases of regular users being tracked in this specific investigation.
That does not make the issue small. It means the risk is concentrated around journalists, dissidents, public officials, executives, activists, diplomats, and others whose location may have intelligence value.
What mobile operators should fix
The main fix must come from the telecom industry, not individual users. Operators need stronger signaling firewalls, better screening of roaming and interconnect traffic, strict validation of signaling identifiers, and faster blocking of abusive network paths.
Operators also need to reduce reliance on legacy trust models. SS7 was built for a smaller and more trusted telecom world. That model no longer fits an ecosystem where commercial surveillance vendors can seek indirect access through operators or intermediaries.
For Diameter and 5G-era signaling, operators need to implement available security protections consistently. Citizen Lab says newer protocols are not enough if the industry does not deploy the safeguards they were designed to support.
Defensive priorities for telecoms and high-risk users
- Audit SS7 and Diameter traffic for abnormal location queries.
- Validate signaling identifiers against legitimate operator relationships.
- Monitor third-party interconnect providers more closely.
- Block suspicious routing paths that do not match expected roaming relationships.
- Apply stricter controls to Diameter security features.
- Investigate hidden SMS and SIM Toolkit command abuse.
- Share threat intelligence across operators and national regulators.
- Review commercial leasing and signaling access arrangements.
- Provide high-risk customers with stronger account and location privacy protections.
High-risk individuals should also reduce exposure where possible. They can use separate travel devices, limit SIM use during sensitive trips, avoid predictable movement patterns, and seek carrier support through security or government channels when they face serious targeting risk.
Still, users cannot fully solve protocol-level surveillance on their own. The attacks happen inside telecom infrastructure, so the strongest protections must come from operators, regulators, and the companies that manage international signaling access.
FAQ
SS7 is an older signaling protocol used mainly in 2G and 3G networks. Diameter is used for inter-operator signaling in 4G and most 5G networks. Both help mobile networks exchange information needed for roaming and connectivity.
Attackers can abuse trusted signaling connections to send location queries that appear to come from legitimate operators. In some cases, they can also use hidden SIM messages that trigger location reporting from the device.
STA1 and STA2 are the names Citizen Lab gave to two surveillance threat clusters. STA1 focused on telecom signaling manipulation, while STA2 used hidden SIM messages as part of its tracking method.
Citizen Lab said these campaigns typically target high-profile individuals and are not used for mass surveillance. It also said it has not identified cases of regular users being tracked in this investigation.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages