Deep#Door malware uses Python backdoor to steal passwords, cloud tokens and SSH keys

Security researchers have detailed a new Windows malware framework called Deep#Door that combines a Python-based backdoor with broad credential theft and surveillance features.
The malware uses an obfuscated batch script to deploy an embedded Python payload. This design helps it reduce external downloads, hide activity, and keep its attack chain compact.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Once active, Deep#Door can steal browser passwords, cloud credentials, SSH keys, Wi-Fi credentials, clipboard data, screenshots, webcam images, microphone recordings, and system information.
What is Deep#Door?
Deep#Door is a Python-based remote access trojan analyzed by Securonix Threat Research. It targets Windows systems and gives attackers persistent remote control after the initial script runs.
The infection starts with a batch file named install_obf.bat. The script disables security controls, extracts an embedded Python payload named svc.py, and prepares the system for long-term access.
Securonix said the malware does not appear to be part of a large public campaign at this stage. Current evidence suggests limited or targeted use, but the framework could be adapted by other attackers.
At a glance
| Category | Details |
|---|---|
| Malware name | Deep#Door |
| Platform | Windows |
| Main language | Python |
| Initial loader | Obfuscated batch script |
| Observed loader name | install_obf.bat |
| Embedded payload | svc.py |
| C2 method | bore.pub TCP tunneling service |
| Main risks | Credential theft, surveillance, remote access, persistence, and lateral movement |
How the attack starts
The attack begins when a victim runs the malicious batch file. Securonix assessed that the file may be delivered through common methods such as phishing, although the full distribution method remains unclear.
Unlike many loaders, Deep#Door does not need to fetch its main backdoor from an external server. The Python implant is already embedded inside the batch file.
The loader reads its own contents, extracts the hidden payload, writes it to the system, and executes it. This self-contained method can reduce network indicators during the early stage of infection.
Why the embedded Python payload matters
Embedding the implant inside the loader gives attackers a smaller and quieter delivery chain. Security tools may miss the attack if they only look for executable downloads or suspicious remote payload retrieval.
Python also gives the malware flexibility. Attackers can add functions, run commands, collect data, and perform surveillance without relying on a traditional compiled Windows executable.
This makes Deep#Door part of a wider trend where attackers use scripts, interpreted languages, and trusted system components to blend into normal activity.
Deep#Door capabilities
- Remote command execution
- Reverse shell access
- System reconnaissance
- Keylogging
- Clipboard monitoring
- Screenshot capture
- Webcam capture
- Microphone recording
- Browser credential theft
- Cloud credential theft
- SSH key extraction
- Windows Credential Manager access
How Deep#Door stays on a system
Deep#Door uses several persistence methods so it can survive reboots and cleanup attempts. It creates Startup folder scripts, Registry Run entries, scheduled tasks, and optional WMI event subscriptions.
The malware also includes watchdog behavior. If a persistence mechanism gets removed, the implant can recreate it, making full remediation harder for security teams.
This matters because removing the visible script or killing one process may not end the compromise. Defenders need to inspect all persistence locations and verify that the malware cannot restart.
How it weakens Windows defenses
Before and during deployment, Deep#Door tampers with several Windows security and logging features. Securonix reported activity linked to Windows Defender tampering, SmartScreen bypass, PowerShell logging suppression, event log clearing, and firewall logging changes.
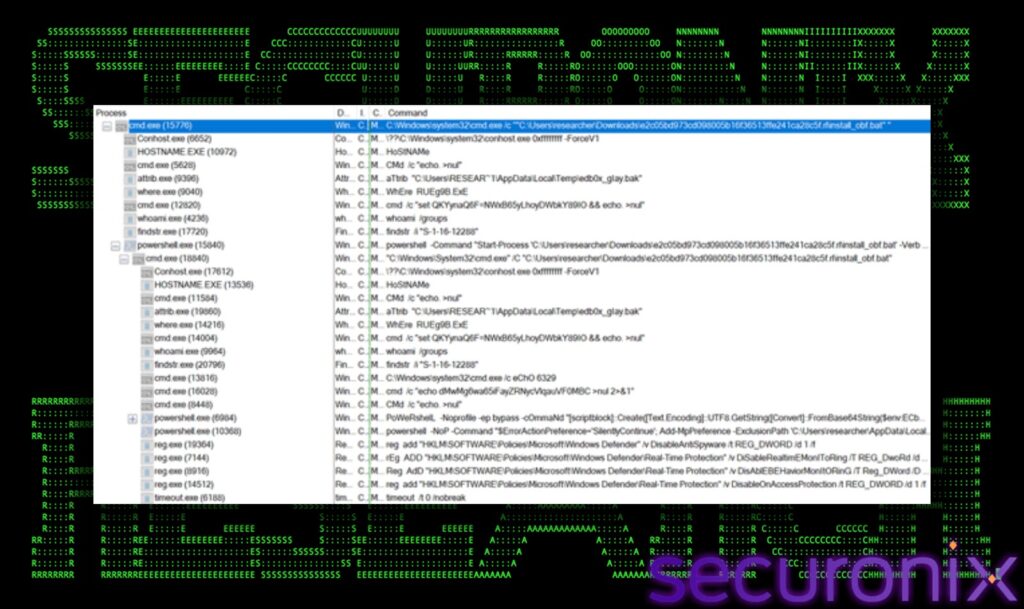
The malware also uses anti-analysis checks, including sandbox, debugger, and virtual machine detection. These checks help it avoid running in research environments.
Deep#Door further uses AMSI and ETW patching, ntdll unhooking, command-line wiping, and timestamp changes. These techniques can reduce visibility for endpoint tools and make forensic analysis more difficult.
Defense evasion techniques
| Technique | Purpose |
|---|---|
| AMSI patching | Reduces script inspection by Windows security controls. |
| ETW patching | Limits telemetry that defenders use for detection. |
| ntdll unhooking | Attempts to remove security tool hooks from system functions. |
| SmartScreen bypass | Weakens Windows download and execution warnings. |
| Event log clearing | Removes evidence of execution and system changes. |
| Command-line wiping | Hides runtime arguments from security tools and investigators. |
Credential theft is the biggest risk
Deep#Door targets data that attackers can reuse after the malware is removed. That includes browser credentials, cloud tokens, SSH keys, Wi-Fi credentials, and Windows Credential Manager entries.
Browser-stored passwords can give attackers access to email, admin portals, cloud dashboards, developer tools, and internal services. Cloud tokens can create an even bigger risk if they allow direct access to AWS, Azure, or Google Cloud resources.
SSH keys are also dangerous because they may unlock remote servers without a password. If attackers steal them, they can move deeper into infrastructure and maintain access through legitimate authentication.
What data Deep#Door targets
| Data type | Why attackers want it |
|---|---|
| Browser passwords | They can unlock personal, business, and admin accounts. |
| Browser cookies | They may help attackers reuse active sessions. |
| Cloud credentials | They can expose cloud consoles, storage, workloads, and secrets. |
| SSH keys | They can give attackers direct access to servers. |
| Wi-Fi credentials | They can help with local network access and future intrusion attempts. |
| Clipboard data | It may contain copied passwords, tokens, commands, or documents. |
Public tunneling makes C2 harder to spot
Deep#Door communicates through bore.pub, a public TCP tunneling service. This lets attackers reach compromised systems without exposing a dedicated command-and-control server.
Using a public tunneling service can help malicious traffic blend with legitimate traffic. It can also make infrastructure takedown harder because the attacker does not need to maintain a normal C2 host.
Securonix recommends monitoring for unusual TCP connections across dynamic port ranges, especially repeated attempts around ports 41234 through 41243.
Why defenders should take it seriously
Deep#Door combines several high-impact capabilities in one framework. It can persist, steal credentials, monitor users, execute commands, and weaken host telemetry.
The malware also creates risk after the infected machine is cleaned. Stolen cloud tokens, passwords, browser sessions, and SSH keys may continue to give attackers access unless organizations rotate them.
That means response teams should treat a Deep#Door infection as an identity and infrastructure incident, not only as a malware cleanup task.
What organizations should do now
- Block or closely monitor script files from email, shared links, and untrusted downloads.
- Investigate suspicious .BAT, .CMD, PowerShell, and Python execution.
- Enable PowerShell Script Block Logging and command-line process logging.
- Monitor Startup folders, Registry Run keys, scheduled tasks, and WMI event subscriptions.
- Watch for Python execution from unusual locations such as local app data folders.
- Alert on Defender tampering, AMSI patching, ETW patching, and event log clearing.
- Monitor outbound traffic to tunneling services such as bore.pub.
- Rotate browser passwords, cloud tokens, SSH keys, and Wi-Fi credentials after suspected compromise.
- Use endpoint detection tools that can flag behavior, not only known file hashes.
FAQ
Deep#Door is a Python-based Windows backdoor and credential stealer analyzed by Securonix Threat Research. It can persist on a system, run attacker commands, monitor users, and steal sensitive credentials.
The infection starts when a user runs an obfuscated batch script. The script extracts an embedded Python payload and sets up persistence on the Windows machine.
Deep#Door can target browser passwords, browser cookies, cloud credentials, SSH keys, Wi-Fi credentials, and Windows Credential Manager data.
It uses bore.pub, a public TCP tunneling service, to support remote access. This can make its traffic harder to separate from legitimate tunneling activity.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages