China-aligned attackers use ShadowPad and proxy tools in Asia espionage campaign
A China-aligned threat cluster is targeting government agencies, critical infrastructure, defense-linked organizations, and technology companies across Asia and beyond.
Trend Micro tracks the activity under the temporary name SHADOW-EARTH-053. Researchers say the group has been active since at least December 2024 and has focused on espionage against high-value organizations.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign uses old but still dangerous Microsoft Exchange and IIS vulnerabilities, web shells, ShadowPad implants, proxy tools, credential theft utilities, and built-in Windows tools to stay inside victim networks.
What Trend Micro found
Trend Micro said SHADOW-EARTH-053 has targeted organizations across at least eight countries. Most observed victims were in South, East, and Southeast Asia, with one European NATO government also in scope.
The affected footprint includes Pakistan, Thailand, Malaysia, India, Myanmar, Sri Lanka, Taiwan, and Poland. The victims included government entities, critical infrastructure, defense-adjacent technology providers, and transportation organizations.
Researchers assessed that the activity aligns with China’s broader strategic interests. The target profile points to cyberespionage and possible intellectual property theft rather than financially motivated cybercrime.
At a glance
| Category | Details |
|---|---|
| Threat cluster | SHADOW-EARTH-053 |
| Tracking status | Temporary intrusion set designation |
| Assessed alignment | China-aligned |
| Activity start | At least December 2024 |
| Main targets | Government, critical infrastructure, defense-linked technology firms, and transportation |
| Targeted regions | South, East, and Southeast Asia, plus one European NATO state |
| Main malware | ShadowPad |
| Main access vector | Unpatched Microsoft Exchange and IIS servers |
Old Exchange flaws remain the entry point
The attackers relied on N-day vulnerabilities in internet-facing Microsoft Exchange and IIS servers. Trend Micro specifically mentioned the ProxyLogon chain, including CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065.
Microsoft released patches for these Exchange vulnerabilities in 2021. Even so, exposed and unpatched Exchange servers remain useful to espionage groups because they often sit at the edge of enterprise networks.
After exploitation, the attackers deployed GODZILLA web shells to maintain remote access. These web shells allowed command execution, reconnaissance, and further payload deployment inside compromised environments.
How the attack chain works
- Attackers scan for exposed Microsoft Exchange or IIS servers.
- They exploit known vulnerabilities where systems remain unpatched.
- They deploy GODZILLA or similar web shells for persistent access.
- They conduct reconnaissance through IIS worker processes and command-line tools.
- They deploy ShadowPad through DLL sideloading.
- They use proxy and tunneling tools to hide communication.
- They harvest credentials and move laterally through the network.
ShadowPad is the main backdoor
ShadowPad sits at the center of the campaign. It is a modular backdoor first associated with APT41 in 2017 and later seen across several China-aligned intrusion sets.
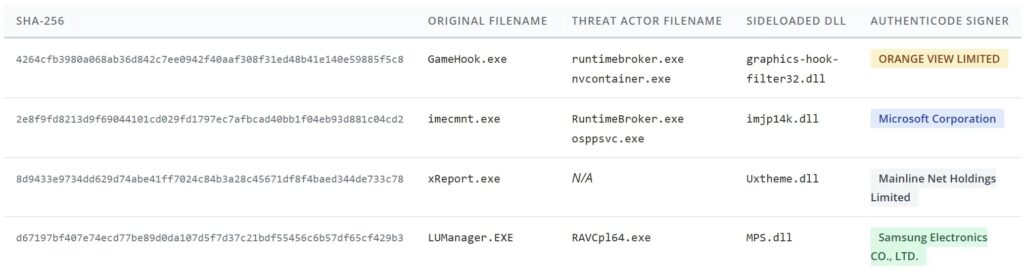
In this campaign, the attackers used DLL sideloading to run ShadowPad. They placed a malicious DLL next to a legitimate signed executable so the trusted program would load the attacker’s code.
Trend Micro observed legitimate executables from vendors such as Toshiba, Samsung, and Microsoft being abused in this way. The attackers also renamed files to make them look like normal Windows processes.
The registry loader adds stealth
One notable technique involved a registry-based ShadowPad loader. Instead of storing the payload directly inside the malicious DLL, the loader retrieved encrypted shellcode from a machine-specific registry key under HKEY_CURRENT_USER\Software.
This approach complicates forensic recovery because analysts cannot fully understand the payload by reviewing the DLL alone. They also need the related registry data from the infected machine.
Persistence was created through a scheduled task named M1onltor. Trend Micro said the task ran the sideloaded binary every five minutes with the highest available privileges.
Tools used in the campaign
| Tool or technique | Role in the campaign |
|---|---|
| ShadowPad | Main modular backdoor for long-term access. |
| GODZILLA web shell | Persistent command execution after server compromise. |
| IOX proxy | Proxying and covert network access. |
| GOST | Tunneling traffic through SOCKS5 and other protocols. |
| Wstunnel | Tunneling traffic over HTTPS and WebSocket channels. |
| WMIC | Lateral movement and remote command execution. |
| Mimikatz | Credential harvesting. |
| Evil-CreateDump | Dumping process memory to extract credentials. |
| RingQ | Packing malicious binaries to reduce detection. |
Proxy tools help attackers blend in
The attackers used IOX, GOST, and Wstunnel to create covert communication paths. These tools can tunnel traffic through common protocols and make malicious activity look less obvious on busy networks.
Proxy and tunneling tools matter in espionage campaigns because they help operators maintain access without relying on a single direct command-and-control path.
The group also used domains that impersonated products, security companies, or DNS-related services. This type of infrastructure naming can reduce suspicion during quick log reviews.
WMIC supported lateral movement
SHADOW-EARTH-053 used Windows Management Instrumentation Command-line, or WMIC, to move across compromised networks and deploy backdoors on additional systems.
Trend Micro also observed the attackers pushing web shells to internal Exchange servers by using existing administrative credentials. That suggests the group continued collecting credentials as it expanded inside victim environments.
Credential tools such as Mimikatz and Evil-CreateDump were used through IIS worker processes, which should stand out in endpoint telemetry because web server processes normally should not spawn credential-dumping activity.
A related cluster overlaps with the same victims
Trend Micro also identified a related cluster tracked as SHADOW-EARTH-054. Nearly half of SHADOW-EARTH-053’s targets showed overlap with this cluster.
The two groups shared tool hashes, initial access methods, and overlapping techniques. However, Trend Micro said available evidence points to independent exploitation of the same vulnerabilities rather than direct operational coordination.
SHADOW-EARTH-054 also showed connections to activity tracked by other vendors as CL-STA-0049, REF7707, and Earth Alux, adding another layer to the China-aligned espionage landscape.
Why defenders should take this seriously
The campaign shows how long-patched vulnerabilities can remain useful to advanced attackers. ProxyLogon became public in 2021, yet it still appears in active espionage operations years later.
Exchange and IIS servers are especially valuable because they often face the internet and connect deeply into internal networks. Once attackers gain access, they can stage web shells, steal credentials, and reach other systems.
For government and critical infrastructure organizations, this creates a long-term risk. Espionage groups may stay quiet for months before deploying final implants or expanding access.
Recommended defenses
- Patch Microsoft Exchange and IIS systems immediately.
- Remove internet exposure where public access is not required.
- Use IPS or WAF virtual patching when immediate patching is not possible.
- Monitor web directories for new or modified .aspx, .ashx, and .jsp files.
- Inspect IIS worker processes for command shells, reconnaissance tools, and credential dumping.
- Watch staging directories such as C:\Users\Public, C:\ProgramData, C:\PerfLogs, and C:\Windows\Temp.
- Audit scheduled tasks, especially tasks that run every few minutes with high privileges.
- Hunt for DLL sideloading using signed executables from trusted vendors.
- Monitor for IOX, GOST, Wstunnel, Mimikatz, and Evil-CreateDump activity.
- Review outbound traffic from Exchange and IIS servers for unusual proxy or tunnel behavior.
Detection areas to review
| Area | What to look for |
|---|---|
| Exchange and IIS logs | Suspicious access patterns, web shell uploads, and unusual HTTP handlers. |
| Web directories | New files named like error.aspx, signout.aspx, warn.aspx, tunnel.ashx, or other unexpected scripts. |
| Processes | w3wp.exe spawning cmd.exe, PowerShell, nslookup, nltest, or credential tools. |
| Persistence | Scheduled tasks such as M1onltor and repeated execution every few minutes. |
| Registry | Unusual encrypted payload data under HKEY_CURRENT_USER\Software. |
| Network traffic | Unexpected SOCKS5, HTTPS tunnel, proxy, or external C2 communication from servers. |
FAQ
SHADOW-EARTH-053 is a temporary name Trend Micro uses for a China-aligned intrusion cluster targeting government, critical infrastructure, defense-linked, technology, and transportation organizations.
ShadowPad is a modular backdoor associated with China-aligned threat activity. It can help attackers maintain access, load plugins, and conduct long-term espionage inside compromised networks.
The attackers exploited known vulnerabilities in internet-facing Microsoft Exchange and IIS servers, including the ProxyLogon Exchange vulnerability chain.
They remain dangerous because some organizations still run exposed systems without the required patches. Attackers continue scanning for these systems because they provide direct access to valuable networks.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages