Salat Stealer uses QUIC, WebSocket, and TON blockchain fallback for stealthy remote control
A newly analyzed Windows malware family called Salat Stealer uses QUIC, WebSocket, HTTP/2, and TON blockchain fallback to keep remote control channels alive on infected systems. DarkAtlas researchers describe it as a Go-based remote access trojan with deep information-stealing and post-exploitation capabilities.
The malware can steal browser data, cryptocurrency wallet files, Discord and Steam tokens, screenshots, process lists, and keystrokes. It can also give attackers remote shell access, desktop streaming, webcam features, file delivery, command execution, and SOCKS proxy capabilities.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Salat matters because it combines credential theft with persistent remote access. Instead of acting like a basic infostealer, it works more like a full attacker toolkit that can stay on a Windows machine, receive commands, and adapt its communication path when infrastructure becomes unavailable.
Why Salat Stealer stands out
Many stealers focus on collecting passwords, cookies, and wallet files once, then leaving. Salat adds stronger remote-control features that can keep the victim machine useful to attackers after the first data theft stage.
DarkAtlas said the malware uses six string-obfuscation modes and a per-machine key derivation process. It creates a unique victim identity from the hostname, hardware ID, and a hardcoded salt, then uses that value as an agent ID in communications with its command server.
This design makes static analysis harder and helps the operator track infected machines more reliably. It also shows that the malware was built with long-term control in mind.
At a glance
| Detail | What researchers found |
|---|---|
| Malware name | Salat Stealer |
| Platform | Windows |
| Language | Go |
| Main role | Remote access trojan and infostealer |
| Communication methods | WebSocket, HTTP/2, HTTP/3, and QUIC |
| Backup infrastructure | TON blockchain lookup through DNS-over-HTTPS |
| Persistence methods | Hidden file copy, scheduled task, and registry Run key |
| Data at risk | Browser credentials, cookies, tokens, wallet files, screenshots, process lists, and keystrokes |
How Salat communicates with attackers
Salat probes several transport options before choosing how to reach its command server. It supports WebSocket, HTTP/2, HTTP/3, and QUIC, with a preference for WebSocket and QUIC because those protocols can blend into modern web traffic.
If one command server fails, the malware rotates through other hardcoded endpoints. DarkAtlas recovered five command server URLs from the sample, all using the same /sa1at/ path.
If all embedded servers fail, Salat attempts to retrieve fresh command infrastructure through the TON blockchain. It uses DNS-over-HTTPS queries to Cloudflare’s resolver, decodes TON smart contract data, verifies the result, and extracts a replacement server address.
Why TON fallback makes takedown harder
Traditional malware takedowns often focus on blocking or seizing known command servers. That becomes harder when the malware can pull replacement infrastructure from a decentralized blockchain source.
Salat still needs reachable servers to receive commands and exfiltrate data. However, the TON fallback gives operators a way to recover after defenders block the original infrastructure.
This makes network defense more difficult. Security teams need to watch for command traffic patterns, not only static domains or IP addresses.
What Salat can steal
- Chromium browser passwords, cookies, and encrypted values
- Firefox and Gecko browser data
- Discord tokens
- Steam tokens
- Cryptocurrency wallet files
- Screenshots
- Process lists
- Keystrokes
- Clipboard data
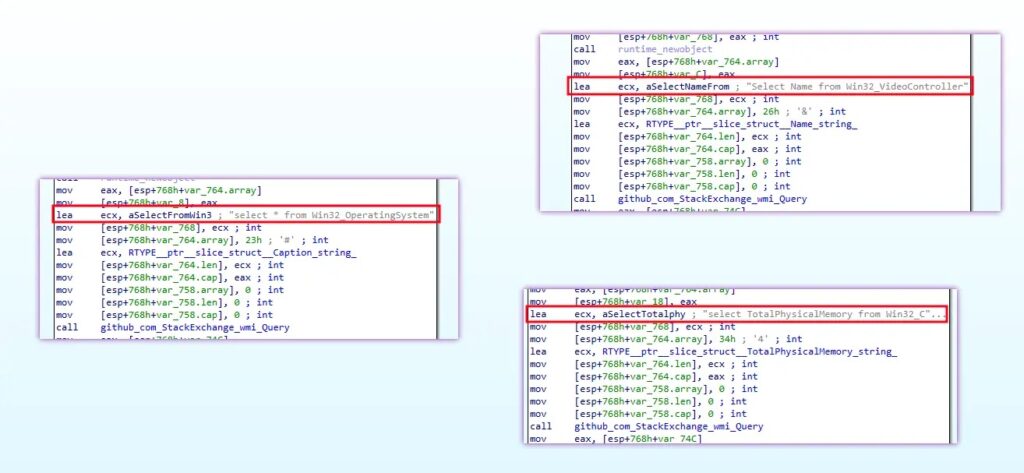
- System information such as CPU, GPU, RAM, operating system, and active window title
Remote control features increase the risk
Salat does not stop after stealing stored credentials. DarkAtlas found command handlers that support remote shell execution, file downloads, screenshots, data theft, proxying, and privilege escalation attempts.
The malware can also start WebSocket sessions that support remote interaction features, including desktop, shell, webcam, microphone, and file manager activity. That gives attackers a wider set of options after infection.
In a business environment, this can turn one infected endpoint into a foothold for deeper intrusion. Attackers may use stolen credentials, SOCKS proxying, or remote shell access to move further into the network.
Persistence methods used by Salat
Salat uses several persistence techniques to survive restarts. It can copy itself under a name that resembles a legitimate Windows process, then mark the file as hidden and system-protected.
DarkAtlas also found a scheduled task mechanism that runs at user logon and repeats every 30 minutes. This helps the malware restart even if the process stops.
The third persistence method uses the Windows registry Run key under the current user profile. That makes the malware launch automatically when the user signs in.
Defender checklist
- Monitor unusual outbound QUIC and WebSocket traffic from endpoints.
- Look for repeated connections to unfamiliar domains using the same path structure.
- Hunt for hidden executables named like Windows processes, such as explorer.exe or svchost.exe, outside normal system folders.
- Review scheduled tasks that run at logon and repeat every 30 minutes.
- Check the HKCU Run key for suspicious entries.
- Alert on unexpected access to browser credential stores and wallet directories.
- Watch for unusual DNS-over-HTTPS activity to Cloudflare from endpoints that do not normally use it.
- Update endpoint detection rules for Go-based malware and packed Windows RAT behavior.
Why businesses should care
Salat combines stealthy communication, persistence, credential theft, and remote control in one malware family. That combination creates risk for both individuals and organizations.
For home users, the biggest danger is theft of passwords, crypto wallets, and account tokens. For companies, the bigger problem is lateral movement, data theft, and attacker persistence inside the environment.
Security teams should treat Salat as more than a one-time stealer. Any confirmed infection should trigger credential rotation, endpoint isolation, forensic review, and a search for follow-on access.
FAQ
Salat Stealer is a Go-based Windows malware family that works as both an infostealer and a remote access trojan.
It can steal browser credentials, cookies, Discord tokens, Steam tokens, crypto wallet files, screenshots, process data, keystrokes, and other sensitive information.
It includes resilient command channels, TON blockchain fallback, persistence, keylogging, remote shell access, desktop and webcam features, and SOCKS proxy support.
DarkAtlas found support for WebSocket, HTTP/2, HTTP/3, and QUIC. The malware can also use TON blockchain data as a fallback method for finding fresh command infrastructure.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages