HumanitarianBait campaign uses GitHub Releases to host Python infostealer payloads

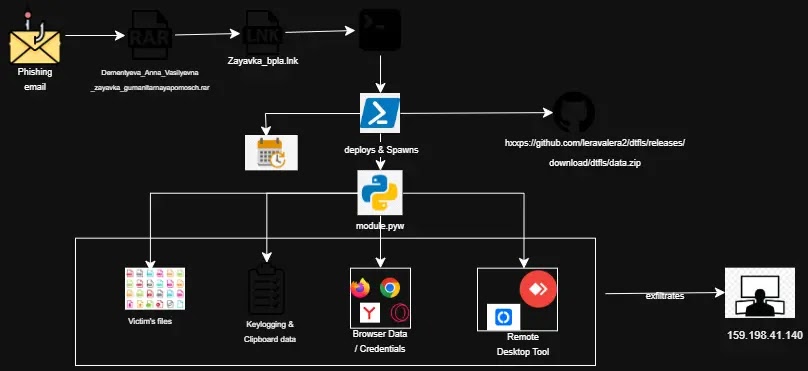
A cyberespionage campaign named HumanitarianBait is using fake humanitarian aid documents to deliver a Python-based infostealer on Windows systems. The attack hides a malicious shortcut inside a RAR archive and uses GitHub Releases to host the payload.
Cyble Research and Intelligence Labs says the campaign uses Russian-language lures that appear to target Russian-speaking individuals or organizations. The lure shows a believable aid request document while the malware installs in the background.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign stands out because the attacker uses trusted infrastructure to reduce suspicion. GitHub hosts the payload files, while the malware builds a local Python environment in the victim’s AppData folder and runs without a traditional executable implant.
How the attack starts
The infection begins with a phishing email that carries a compressed RAR archive. Inside the archive is a Windows LNK shortcut disguised as a humanitarian aid request form.
When the victim opens the shortcut, PowerShell reads hidden content embedded inside the LNK file and executes it directly in memory. The malware also opens a decoy Russian-language PDF so the victim believes they only opened a normal document.
Cyble also observed a secondary survey-themed lure, which suggests the attacker is testing or refining different delivery methods. Attribution remains unclear, but the language and theme point toward Russian-speaking targets.
At a glance
| Category | Details |
|---|---|
| Campaign name | HumanitarianBait |
| Research source | Cyble Research and Intelligence Labs |
| Initial delivery | Phishing email with a RAR archive |
| Malicious file type | Windows LNK shortcut |
| Lure theme | Russian-language humanitarian aid request |
| Payload hosting | GitHub Releases |
| Malware type | PyArmor-packed Python infostealer and RAT |
| Persistence | Windows Scheduled Task named WindowsHelper |
| Known C2 server | 159.198.41[.]140 |
Why GitHub Releases helps the attacker
The attacker stores the malicious data.zip payload in GitHub Releases rather than placing the code directly in a repository. This helps malicious downloads blend into normal GitHub traffic.
Cyble says the same GitHub account also hosts clean files, including a Python embedded runtime and pip installer. That makes the full download chain look closer to a normal developer setup process.
The attacker repeatedly republished the payload with changing hashes. That points to active campaign maintenance and makes hash-only detection less reliable.
The malware builds its own Python environment
After execution, the malware creates a self-contained Python environment inside the user’s AppData directory. The folder is named WindowsHelper, which makes it look like a normal Windows component at first glance.
This setup does not require administrator access. The malware can run from a user-writable location and avoid some controls that focus mainly on system directories.
Two VBScript launchers run the payload silently through pythonw.exe, which helps hide visible windows. A scheduled task then restarts the implant at short intervals and keeps it active after reboot.
What the implant can steal
The Python implant functions as a surveillance tool, not just a basic password stealer. It can collect browser credentials, cookies, keystrokes, clipboard data, screenshots, Telegram session data, and sensitive local files.
Cyble says the malware targets Chrome, Edge, Brave, Opera, Yandex Browser, and Firefox. It can decrypt Chromium browser data by extracting the local master key and handling several Chrome encryption formats.
The implant can also install RustDesk or AnyDesk silently. This gives the attacker live remote desktop access to the infected system without showing the victim an obvious setup window.
Key capabilities
- Steals stored browser passwords and session cookies.
- Captures keystrokes continuously.
- Monitors clipboard contents.
- Takes desktop screenshots.
- Collects Telegram session data.
- Searches local files for sensitive information.
- Uploads stolen data to an attacker-controlled server.
- Silently installs remote desktop tools for interactive access.
Why detection is difficult
HumanitarianBait uses several layers of evasion. The LNK file contains embedded content that PowerShell reads from a specific offset, which can confuse automated tools that do not analyze the original shortcut file properly.
The payload is protected with PyArmor v9.2 Pro, a commercial obfuscation tool that makes Python code harder to decompile and review. This slows static analysis and can delay detection.
The campaign also uses trusted platforms and common tools. GitHub, Python, VBScript, PowerShell, scheduled tasks, RustDesk, and AnyDesk can all appear legitimate in the right context, so defenders need behavior-based monitoring.
What security teams should monitor
- RAR archives containing Windows LNK files.
- PowerShell execution launched from shortcut files.
- Large or unusual LNK files with embedded content.
- New folders named WindowsHelper under AppData.
- Unexpected Python embedded environments in user directories.
- VBScript launchers such as run.vbs or launch_module.vbs.
- Scheduled tasks named WindowsHelper or tasks that run every few minutes.
- Downloads from unusual GitHub Release assets.
- Silent installation or execution of RustDesk and AnyDesk.
- Outbound traffic to 159.198.41[.]140.
How users can reduce risk
Users should treat unexpected compressed files with caution, especially when they contain shortcuts or files with unclear extensions. Humanitarian aid themes can feel urgent, but that urgency is exactly what attackers use to push victims into opening attachments quickly.
Windows users should enable file name extensions in File Explorer. This makes it easier to spot suspicious files that pretend to be documents but are actually shortcuts or scripts.
Organizations should also audit scheduled tasks and user-writable scripting environments. A new recurring task that launches Python, VBScript, or PowerShell from AppData deserves immediate investigation.
Practical mitigation steps
- Block known indicators of compromise at the network and endpoint level.
- Inspect inbound email archives for LNK files.
- Limit script execution from user-writable directories where possible.
- Monitor PowerShell, VBScript, and Python activity from AppData.
- Review GitHub Release downloads from endpoints that do not normally use developer tools.
- Enable file name extensions in Windows.
- Audit Task Scheduler for unknown recurring jobs.
- Restrict unauthorized remote access tools such as RustDesk and AnyDesk.
- Rotate browser-stored credentials after suspected exposure.
- Rebuild affected systems if full compromise cannot be ruled out.
The bigger security lesson
HumanitarianBait shows why phishing attacks no longer need flashy malware files to succeed. A shortcut file, a trusted hosting platform, and a local scripting environment can create a complete surveillance chain.
The campaign also shows why defenders need to look beyond domains and file hashes. The attacker can update release assets and change payload hashes while keeping the same general behavior.
Security teams should focus on the full chain: phishing archives, LNK execution, PowerShell activity, Python environment creation, scheduled task persistence, browser data theft, and remote access tool abuse.
Summary
- HumanitarianBait uses Russian-language humanitarian aid lures to deliver malware.
- The attack starts with a RAR archive containing a malicious Windows LNK file.
- PowerShell executes hidden content from the shortcut while a decoy document opens.
- The payload is hosted in GitHub Releases and protected with PyArmor.
- The malware builds a local Python environment named WindowsHelper.
- The implant can steal browser data, cookies, keystrokes, screenshots, Telegram sessions, and sensitive files.
- Security teams should monitor LNK files, GitHub Release downloads, scheduled tasks, and scripting activity from AppData.
FAQ
HumanitarianBait is a cyberespionage campaign that uses fake Russian-language humanitarian aid documents to deliver a Python-based infostealer and RAT on Windows systems.
The malware can steal browser passwords, session cookies, keystrokes, clipboard data, screenshots, Telegram session data, and sensitive files from the local system.
The attacker uses GitHub Releases to host payload files on trusted infrastructure. This can make malicious downloads look like normal GitHub traffic.
The malware arrives through a phishing email with a RAR archive. The archive contains a malicious Windows LNK shortcut that starts the infection chain when opened.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages