Adobe breach claim puts 13 million support tickets and employee records in focus

Adobe has not publicly confirmed a new breach, but a threat actor calling himself “Mr. Raccoon” claims to have stolen 13 million support tickets, about 15,000 employee records, internal documents, and Adobe’s HackerOne submissions. Right now, the claim remains unverified, and most public reporting traces back to International Cyber Digest and follow-up coverage rather than a confirmed Adobe disclosure.
That distinction matters. A breach claim can still signal real risk, especially when the alleged data includes support records and bug bounty submissions, but readers should not treat the full scope as established fact until Adobe, HackerOne, or another independent source confirms it. Cybernews reported that Adobe had not addressed the claims as of its coverage and said it reached out to the company for comment.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
If the claim proves accurate, the exposure could be serious. Support tickets often contain names, email addresses, account details, product issues, and conversation history, while bug bounty submissions can include technical vulnerability reports that attackers could study for unpatched or poorly understood weaknesses. Adobe’s own public materials show it runs a bug bounty and vulnerability disclosure process through HackerOne, which makes the alleged reference to HackerOne submissions especially sensitive.
What the attacker claims happened
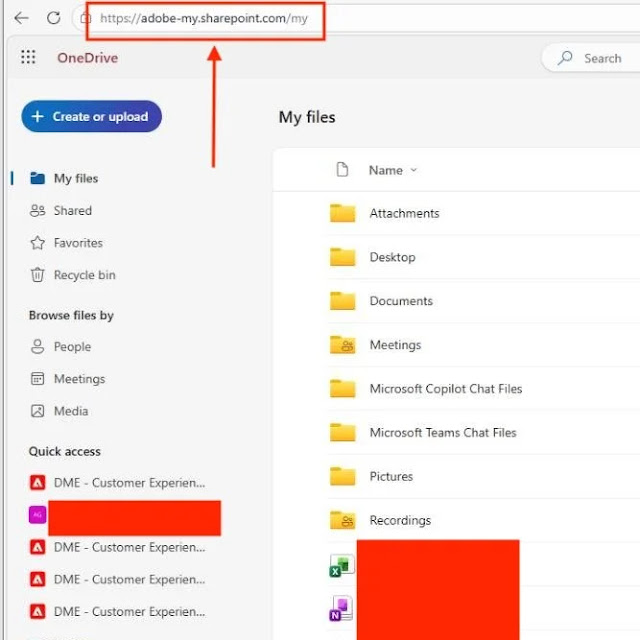
According to the public allegation, the intrusion began through a third-party BPO provider rather than Adobe directly. The reported attack chain says a malicious email infected a support worker’s machine with a remote access tool, after which the attacker moved deeper by compromising additional accounts and abusing support-side access.
The central claim is that the attacker could export large volumes of support tickets in one request from an agent-facing environment. If that description holds up, it would point to a major access control problem around data export permissions, rate limiting, or monitoring inside a support workflow. At this stage, though, no official Adobe advisory has confirmed that such a weakness existed.
Public Adobe security pages show the company maintains a Product Security Incident Response Team, a Trust Center, and active bug bounty intake channels. Those pages outline Adobe’s formal security reporting process, but I could not find a public Adobe breach statement tied to this “Mr. Raccoon” claim on Adobe’s official newsroom, Trust Center, or PSIRT pages during this check.
Why this alleged leak would matter
If customer support data got exposed at this scale, the fallout would reach beyond Adobe. Support systems often hold long conversational histories, case attachments, internal notes, and account identifiers, which can help criminals build highly convincing phishing lures or impersonation attempts against both customers and staff. This type of data also gives attackers context they can reuse in later fraud and social engineering campaigns.
The alleged inclusion of employee records raises a second concern. Employee contact data and organizational details can make follow-on phishing, credential theft, or help desk impersonation much easier, especially if an attacker already understands how contractors, managers, and internal tools connect across a support operation. That risk grows when a third-party provider sits inside the workflow.
Then there is the HackerOne angle. Adobe’s official bug bounty program pages confirm the company uses HackerOne for public vulnerability disclosure and rewards. If unpublished submissions were actually taken, the incident could create a window where attackers gain insight into reported security flaws before fixes, mitigations, or coordinated disclosure steps finish.
Quick breakdown
| Item | Current status |
|---|---|
| Company named in claim | Adobe |
| Threat actor alias | “Mr. Raccoon” |
| Alleged exposed data | 13 million support tickets, 15,000 employee records, internal documents, HackerOne submissions |
| Claimed initial access | Third-party BPO environment |
| Official Adobe confirmation found | No public confirmation found during this check |
| Independent verification | Limited |
| Main public sources so far | International Cyber Digest and follow-up reports |
What to watch next
- A direct statement from Adobe confirming, denying, or narrowing the claim
- Any notice from HackerOne about affected submissions or researcher communications
- Signs of leaked ticket data, employee records, or internal documents appearing on criminal forums
- Updated guidance for Adobe customers, support staff, or researchers
- Evidence of third-party vendor compromise rather than a direct Adobe network intrusion
FAQ
A threat actor claims Adobe data was stolen, but Adobe has not publicly confirmed the breach during this check.
I did not find a public Adobe confirmation on Adobe’s official security or trust pages related to this claim.
The public claim mentions support tickets, employee records, internal documents, and HackerOne submissions. That scope remains unverified.
Support records can contain personal data, account details, issue histories, and context that attackers can reuse in phishing or fraud.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages