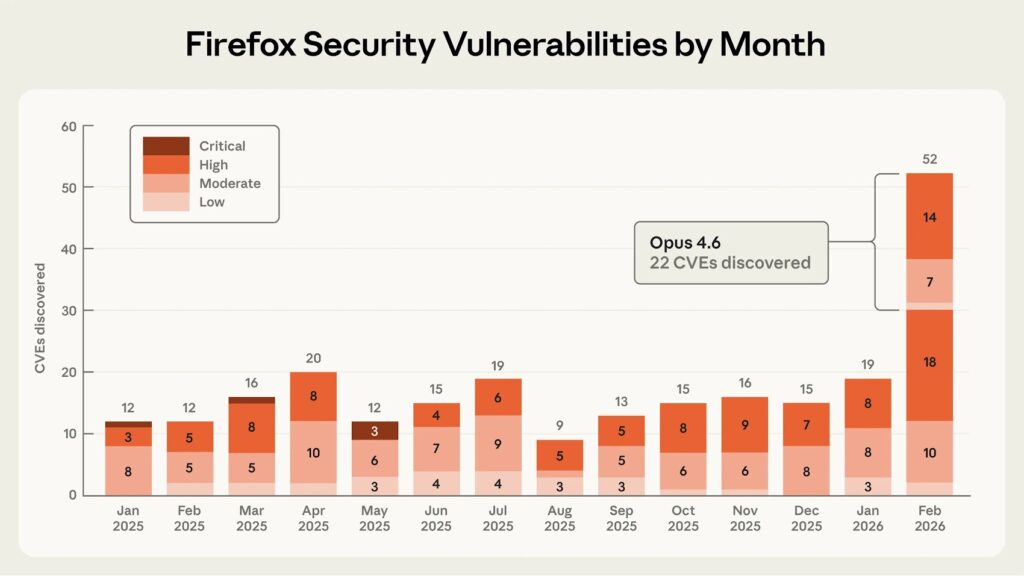
Anthropic says Claude Opus 4.6 helped uncover 22 Firefox vulnerabilities, and Mozilla has already patched them

Anthropic says its Claude Opus 4.6 model found 22 previously unknown vulnerabilities in Firefox during a two-week collaboration with Mozilla. Mozilla says all 22 security bugs are now fixed in the latest version of the browser, and the joint effort also surfaced 90 additional non-security bugs, most of which are already fixed too.
The headline number matters, but the bigger story is speed. Anthropic says Claude found its first use-after-free issue in Firefox’s JavaScript engine after about 20 minutes of exploration. The company then scaled the effort across nearly 6,000 C++ files and submitted 112 unique reports to Mozilla.
Mozilla treated the results seriously because the submissions came with reproducible test cases and candidate patches. According to Mozilla’s engineering post, its team validated the findings quickly, landed fixes within hours in some cases, and ultimately issued 22 CVEs tied to the collaboration.
The companies also say this work shows where AI helps most right now. Anthropic found that Claude performed much better at discovering flaws than at turning them into working exploits. After several hundred exploit-generation attempts that used about $4,000 in API credits, the model succeeded in only two cases, and those worked only in a stripped-down test environment without some modern browser protections.
What happened
Anthropic says Mozilla classified 14 of the 22 vulnerabilities as high severity. That made the Firefox test notable enough for Anthropic to describe it as nearly one-fifth of all high-severity Firefox vulnerabilities remediated in 2025. Mozilla then shipped fixes in Firefox 148, which was released on February 24, 2026.
Mozilla says the collaboration also uncovered 90 other bugs beyond the 22 security-sensitive issues. Some overlapped with problems that fuzzing often finds, such as assertion failures. Others involved logic errors that Mozilla says its fuzzers had not previously caught.
Why this matters for browser security
Firefox is one of the most heavily tested open-source codebases on the web, which makes it a useful stress test for new defensive tooling. Anthropic says it picked Firefox for exactly that reason, arguing that a mature, widely deployed browser provides a harder and more realistic target than smaller open-source projects.
That point cuts both ways. On one side, defenders now have a faster way to spot dangerous bugs in large codebases. On the other, the same research suggests AI can lower the cost of vulnerability discovery much faster than it lowers the cost of safe remediation. Mozilla says this kind of large-scale AI-assisted analysis now belongs in the security engineer’s toolbox, while Anthropic says the find-and-fix cycle needs to speed up before attackers benefit from the same shift.
Key facts at a glance
| Detail | Verified information |
|---|---|
| Bugs found in Firefox | 22 vulnerabilities in two weeks |
| High-severity issues | 14, according to Mozilla’s severity assignment |
| Other bugs found | 90 additional bugs, most already fixed |
| Firefox version with fixes | Firefox 148, released February 24, 2026 |
| Scope of Anthropic review | Nearly 6,000 C++ files and 112 unique reports |
| First bug discovery time | About 20 minutes |
| Exploit testing result | Two successful cases after several hundred runs, only in a reduced-security test setup |
How Anthropic says Claude worked
Anthropic says Claude performed best when paired with a “task verifier,” which checked whether the model’s output actually achieved the goal. In practice, that meant giving the agent real-time feedback while it explored the codebase, then using automated checks to confirm whether a proposed fix removed the vulnerability without breaking normal functionality.
That setup matters because AI-generated security reports often create extra triage work for maintainers. Mozilla acknowledged that skepticism in its own post, but said Anthropic’s reports stood out because they included minimal test cases, detailed proof-of-concept material, and candidate patches that engineers could verify quickly.
What users and developers should take away
For Firefox users, the immediate message is simple. Update the browser, because Mozilla says the 22 security-sensitive bugs tied to this effort are already fixed in the latest release.
For developers, the lesson is more strategic. AI can already speed up code review and vulnerability discovery in mature software projects. It still struggles much more with reliable exploitation in real-world conditions, but the gap is not wide enough for security teams to ignore. Anthropic’s own write-up says crude exploit generation succeeded in limited tests, which makes faster patching and better internal verification more important, not less.
Quick takeaways
- Anthropic says Claude Opus 4.6 found 22 Firefox vulnerabilities in two weeks.
- Mozilla says all 22 are fixed and tied the work to 22 CVEs.
- Mozilla also says the project uncovered 90 more non-security bugs.
- Anthropic says Claude found bugs far more effectively than it built working exploits.
- Firefox 148, released on February 24, 2026, includes the relevant security fixes.
FAQ
Yes. Anthropic says Claude Opus 4.6 found 22 vulnerabilities during a two-week collaboration with Mozilla, and Mozilla confirmed the 22-CVE outcome in its own post.
Mozilla assigned 14 of the 22 vulnerabilities a high-severity rating. Anthropic says that total was nearly one-fifth of all high-severity Firefox vulnerabilities remediated in 2025.
Yes. Mozilla says the bugs are fixed in Firefox 148, announced on February 24, 2026, and Anthropic says most remaining issues from the broader report set will be fixed in upcoming releases.
In limited testing, yes, but only rarely. Anthropic says Claude succeeded in two cases after several hundred runs, and those exploits worked only in a test environment with some protections removed.
The official posts do not make that claim. They show that AI can accelerate discovery and triage when researchers and browser engineers validate the findings, reproduce them, and patch them responsibly.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages