Aqua Trivy Extension Hit by AI-Powered Supply Chain Attack
Threat actors compromised two versions of the Aqua Trivy VS Code extension on OpenVSX on February 27 and 28, 2026. They injected malicious code that hijacks local AI coding tools like Claude, Codex, Gemini, GitHub Copilot CLI, and Kiro CLI. Developers face risks of data theft without any visible alerts.
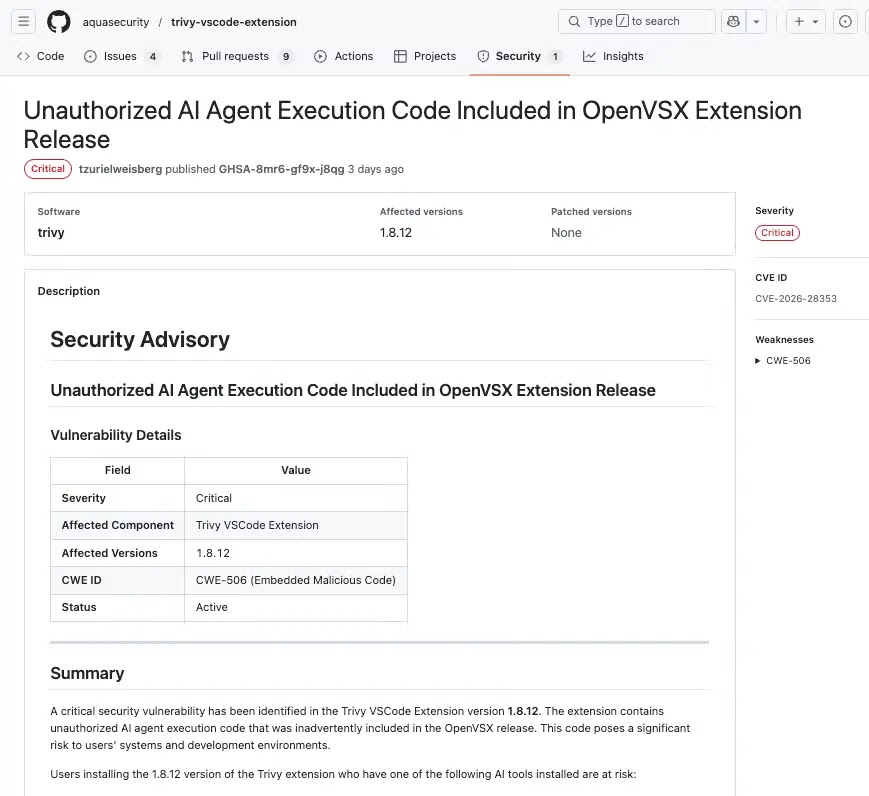
The attack targeted versions 1.8.12 and 1.8.13 under the aquasecurityofficial.trivy-vulnerability-scanner namespace. Socket.dev spotted the issue first and linked it to a broader campaign hitting GitHub Actions in open-source projects. StepSecurity confirmed attackers stole a token to take over Aqua’s Trivy GitHub repo, enabling the push to OpenVSX.
Both versions got pulled from OpenVSX on February 28 after disclosure. The code hid in the workspace activation function, running silently before normal Trivy scans. It used natural-language prompts to turn trusted AI agents into reconnaissance tools, skipping malware signatures that scanners catch.
Socket.dev Advisory: “Unauthorized AI execution in Aqua Trivy extension uses prompts to hijack local tools.”
OpenVSX Announced: “Malicious packages deleted after rapid disclosure.”
Attack Mechanics
Attackers ran AI commands with max permissions as detached processes. Output stayed hidden, so extensions worked normally.
- Version 1.8.12: 2,000-word prompt made AI scan for credentials, tokens, financial data, and comms. It exfiltrated via email or messaging.
- Version 1.8.13: AI gathered system info and tokens, saved to REPORT.MD, then pushed to posture-report-trivy repo via GitHub CLI.
Code used JavaScript comma operators and minified variables for stealth. Missing AI tools failed quietly.
Impact Comparison
| Version | Payload Focus | Exfiltration Method | AI Tools Targeted |
|---|---|---|---|
| 1.8.12 | Broad forensics (creds, files) | Email, messaging channels | Claude, Codex, Gemini, Copilot, Kiro |
| 1.8.13 | System info, auth tokens | GitHub repo push | Same as 1.8.12 |
This method leverages developer-trusted AIs, marking a new supply chain tactic.
Detection and Response Steps
Act fast if you use OpenVSX for Trivy.
- Uninstall versions 1.8.12 and 1.8.13.
- Check VS Code extension history for installs.
- Scan GitHub for posture-report-trivy repo or REPORT.MD commits.
- Review shell history for AI CLI calls with permissive flags.
- Rotate all creds: GitHub tokens, SSH keys, cloud APIs, env vars.
Audit AI logs for odd prompts. Versions before 1.8.12 match the clean GitHub repo.
Why Developers Should Care
Supply chain attacks grow in 2026 as open-source relies on registries like OpenVSX. This bypasses traditional defenses by using AI agents already on machines. Enterprises see rising installs of Trivy for vuln scanning. Quick patches limit damage, but awareness prevents repeats.
FAQ
1.8.12 and 1.8.13 from OpenVSX.
Inside workspace activation with silent, detached AI calls.
Credentials, tokens, system info, and sensitive files.
Yes, up to 1.8.11 and latest from GitHub.
Socket.dev and StepSecurity.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages