Boggy Serpens steps up attacks on diplomats and critical infrastructure, Unit 42 says

Boggy Serpens, the Iranian cyberespionage group also known as MuddyWater, has intensified operations against diplomats, energy firms, maritime organizations, and financial entities in a multi-wave campaign that shows a clear shift toward stealth, persistence, and trusted-account abuse. Unit 42 says the group, which it assesses as linked to Iran’s Ministry of Intelligence and Security, has expanded targeting across the Middle East, Europe, Central Asia, and South America.
The latest assessment shows a threat actor that no longer relies mainly on broad, noisy phishing. Instead, Unit 42 says Boggy Serpens now favors longer campaigns, tailored lures, hijacked legitimate mailboxes, and custom malware built for persistence. Researchers also say the group has adopted Rust-based tooling and AI-assisted malware development to speed up creation of new implants and make analysis harder.
One of the clearest examples came in a campaign against a UAE-based marine and energy company that ran across four attack waves from August 2025 through February 2026. Unit 42 says that operation reflected a focused effort to infiltrate regional maritime and engineering infrastructure rather than a simple one-off phishing run.
What changed in this Boggy Serpens campaign
Unit 42 says Boggy Serpens has moved from high-volume spear phishing and living-off-the-land tooling toward what it calls a “trusted relationship compromise” model. In practice, that means the attackers hijack legitimate internal or partner accounts, then use that trust to send convincing messages that slip past reputation-based filtering.
The group’s older operations often leaned on tools such as Atera, ScreenConnect, SimpleHelp, LaZagne, and CrackMapExec. The newer campaigns still use social engineering, but the payloads and staging methods now look more deliberate. Unit 42 says the actor is pairing account compromise with custom malware families, anti-analysis techniques, Telegram API usage, HTTP-based command and control, and even tailored UDP traffic.
Researchers also flagged overlap with Evasive Serpens, also known as Lyceum or APT34, in early 2025 operations. That overlap suggests resource sharing or coordination inside the broader Iranian cyber ecosystem.
Diplomats were not random targets
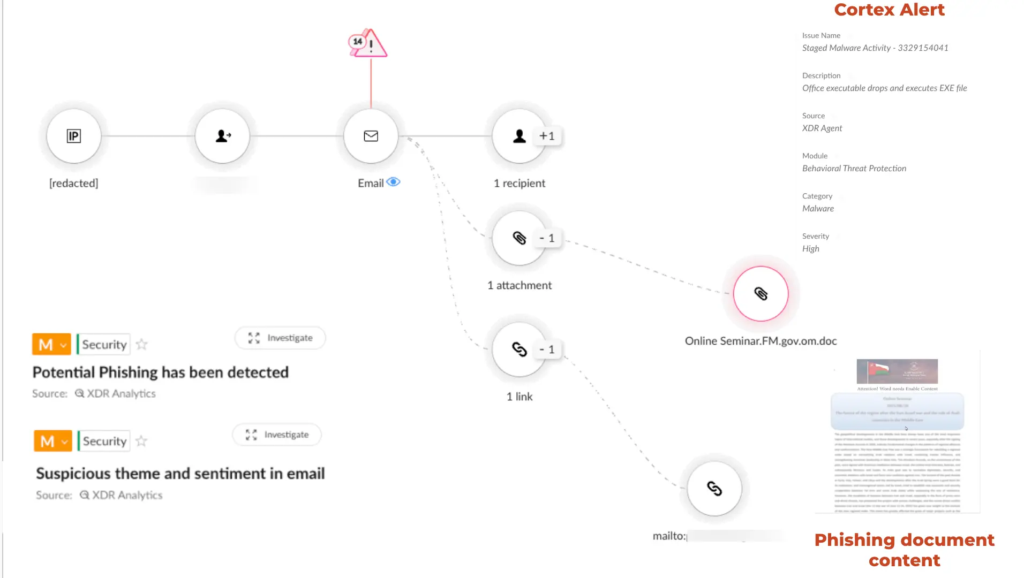
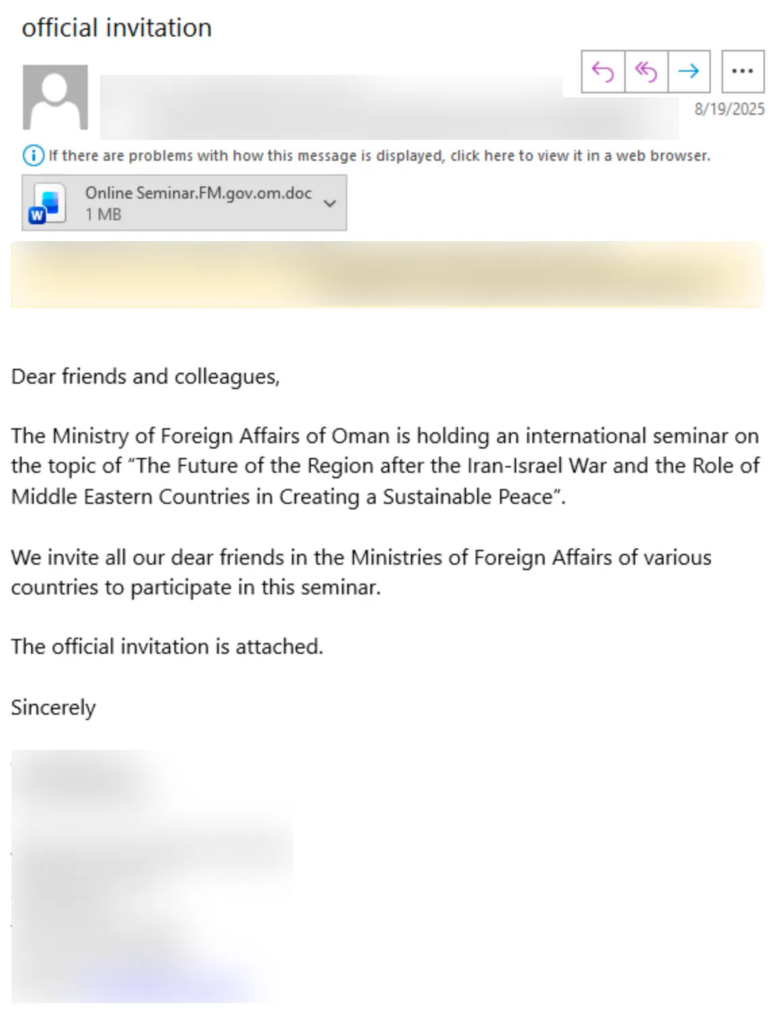
According to Unit 42, Boggy Serpens used a compromised mailbox at Oman’s Ministry of Foreign Affairs in August 2025 to send fake diplomatic invitations tied to a “Sustainable Peace” seminar. Those emails went to foreign ministries, embassies, and international organizations, turning a real government account into a delivery mechanism for espionage lures.
That detail matters because messages from a hijacked official mailbox carry far more credibility than standard phishing emails. Unit 42 says this same broad tactic also appeared in campaigns involving telecommunications and Israeli targets, where the group sent messages themed around cybersecurity guidance and HR content from trusted accounts inside a victim environment.
How the infection chain works
Unit 42 describes a two-stage social engineering process. First, the attackers send a message from a real compromised account, which helps the email bypass many standard reputation checks. Then the attachment itself pushes the user to click “Enable Content,” often by claiming the file was created in an older version of Microsoft Office.
The attached file may look like a blurred Word document, a fake airline ticket, or a forged financial spreadsheet. Once the victim enables macros, the VBA code runs in the background, drops the next-stage payload, and then reveals a normal-looking document to reduce suspicion.
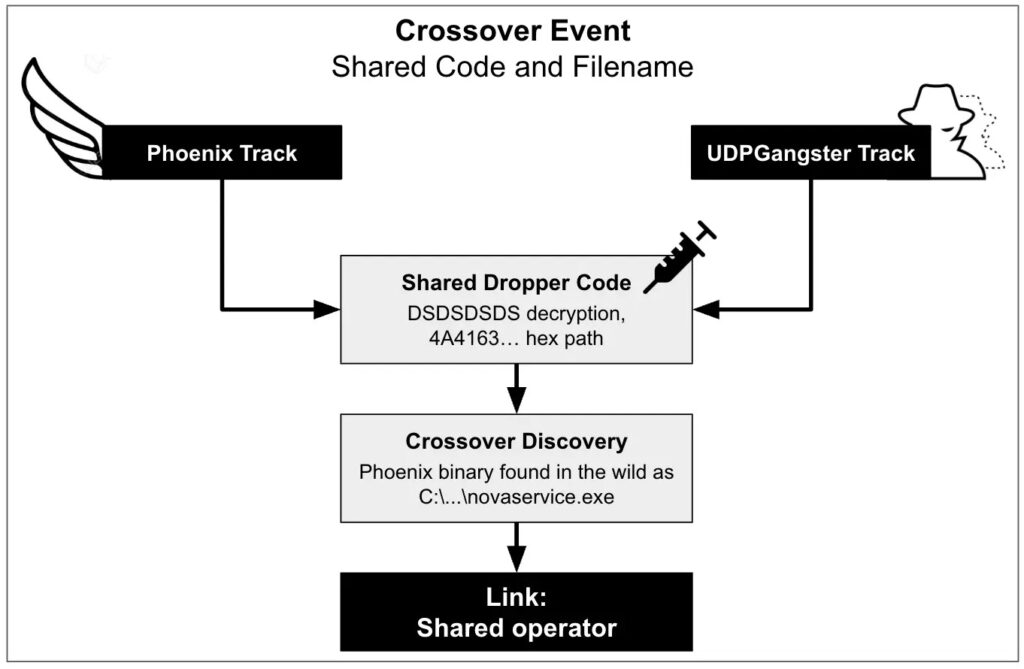
Unit 42 says its forensic work identified two related builder tracks tied to the same development pipeline. One delivered fuller backdoors, including BugSleep and a newly identified Nuso HTTP backdoor. The other deployed a lighter implant over UDP. Shared artifacts, including the same decryption key and file path, pointed to a common origin.
Sectors and regions hit
The targeting is broad, but it is not unfocused. Unit 42 says recent operations have affected entities in Israel, Hungary, Turkey, Saudi Arabia, the UAE, Turkmenistan, Egypt, and South America. The sectors include government, diplomatic institutions, aviation, maritime operations, energy, and finance.
That spread fits a wider pattern seen in Iranian state-backed cyber activity. In a June 2025 threat brief, Unit 42 described Boggy Serpens as a cyberespionage actor that provides stolen data and access to the Iranian government and other threat actors, with initial access often coming through spear phishing and exploitation of known vulnerabilities.
Campaign snapshot
| Item | What Unit 42 reported |
|---|---|
| Actor | Boggy Serpens, also known as MuddyWater |
| Attribution | Assessed subordinate element of Iran’s MOIS |
| Main targets | Diplomats, government, maritime, energy, finance, aviation |
| Notable tactic | Hijacked legitimate email accounts for trusted delivery |
| Malware trend | Rust-based tools, AI-assisted development, custom backdoors |
| Notable operation | Four attack waves against a UAE marine and energy entity from August 2025 to February 2026 |
What defenders should watch for
- Emails sent from legitimate but compromised internal or partner accounts
- Office attachments that ask users to enable macros to display content
- Unusual UDP beaconing or non-standard outbound traffic patterns
- Signs of process injection, registry modification, or staged malware loaders
- Repeated phishing themes tied to diplomacy, HR, travel, finance, or cybersecurity guidance
These defensive priorities come directly from the tactics Unit 42 described in the campaign analysis.
What organizations should do now
- Enforce strong macro restrictions across Microsoft Office
- Require multifactor authentication on all email accounts
- Monitor for anomalous internal email behavior, not just sender reputation
- Hunt for unusual UDP traffic and persistence changes in the registry
- Treat messages from trusted organizations with the same scrutiny as external phishing when attachments or macro prompts appear
Unit 42 specifically recommends strict macro execution controls, behavioral endpoint monitoring, stronger email protections that detect thematic and behavioral anomalies, and threat hunting for UDP-based beaconing, process injection, and unusual registry activity.
FAQ
Boggy Serpens is the Unit 42 name for the Iranian cyberespionage group widely known as MuddyWater. Unit 42 assesses it as linked to Iran’s Ministry of Intelligence and Security.
It shows a move from broad phishing toward longer, more targeted intrusions that abuse trusted relationships, official mailboxes, and custom malware for persistence.
Unit 42 highlighted diplomatic organizations, government, maritime, energy, aviation, telecommunications, and financial entities.
Yes. Unit 42 says the group used a compromised mailbox at Oman’s Ministry of Foreign Affairs in August 2025 to send fake diplomatic invitations to foreign ministries, embassies, and international organizations.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages