BRUSHWORM and BRUSHLOGGER hit South Asian financial firm in targeted malware attack
A targeted cyberattack against a South Asian financial institution used two custom malware tools, BRUSHWORM and BRUSHLOGGER, to steal files, capture keystrokes, and maintain persistent access on infected systems. Elastic Security Labs says BRUSHWORM worked as the main backdoor, while BRUSHLOGGER ran as a DLL-side-loaded keylogger disguised as libcurl.dll.
The case stands out because the malware mixed several practical functions in one operation. Elastic says the backdoor handled persistence, command-and-control communication, payload downloads, USB-based spreading, and file theft, while the second component quietly logged keystrokes and tracked active window titles.
Researchers also found signs that the toolset was still under active development. Earlier test versions appeared on VirusTotal under simple names such as V1.exe, V2.exe, and V4.exe, which suggests the threat actor kept iterating before the malware reached the victim environment. Elastic assessed with moderate confidence that the author may be relatively inexperienced and may have used AI-generated code without fully reviewing it.
How the malware worked
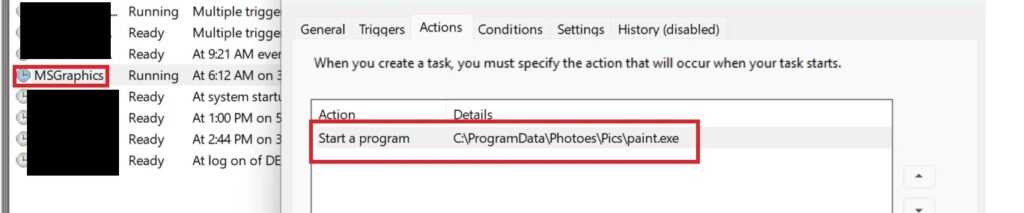
BRUSHWORM arrived as paint.exe and set itself up as the primary implant. Elastic says it created hidden directories, stored stolen files in staging folders, maintained an encrypted configuration file, and established persistence through a Windows scheduled task named MSGraphics that ran at user logon.
The malware then contacted a command-and-control address hosted at resources.dawnnewsisl[.]com/updtdll and downloaded a DLL payload saved as Recorder.dll. It launched that module through a second scheduled task named MSRecorder using rundll32.exe, which gave the attacker a flexible way to add extra capabilities after the initial infection.
BRUSHLOGGER handled credential and activity capture in parallel. Elastic says it used a simple Windows keyboard hook to record system-wide keystrokes and appended the active window title to each session, then wrote the logs to disk with basic XOR obfuscation. That made the data easy for the attacker to collect later, even though the protection itself was weak.
Why financial firms should pay attention
This was not just a basic keylogger incident. Elastic says BRUSHWORM also spread through removable drives using lure names such as Salary Slips.exe, Documents.exe, Presentation.exe, and Emails.exe, which fit naturally inside a corporate financial environment.
The file theft logic also cast a wide net. According to Elastic, the malware targeted documents, spreadsheets, presentations, PDFs, archives, email files, notes, and even code or data files such as .py, .xml, and .json. That combination points to an operation interested in both business data and internal technical material.
One of the more notable features was its offline behavior. If BRUSHWORM could not reach the internet, it still copied itself to USB media and moved stolen files onto those drives, effectively turning removable storage into a physical exfiltration path for restricted or air-gapped environments.
Key technical details
| Component | Role in the attack | Notable behavior |
|---|---|---|
| BRUSHWORM | Main backdoor | Persistence, C2 traffic, payload download, USB spreading, file theft |
| BRUSHLOGGER | Keylogger | DLL side-loading, keystroke capture, active window logging |
| Persistence | Scheduled tasks | Uses MSGraphics and MSRecorder |
| C2 delivery | Remote payload loading | Downloads Recorder.dll from attacker infrastructure |
| Data theft | Broad collection | Targets office files, archives, email stores, and code/data files |
| Offline theft | USB bridge | Copies stolen files to removable media when internet access fails |
Source basis: Elastic Security Labs.
Signs the malware author may still be learning
Elastic’s report says neither binary used strong obfuscation, advanced packing, or mature anti-analysis defenses. The malware checked for simple sandbox conditions, such as low screen resolution or a machine name of sandbox, but the logic was basic and inconsistent. Even when it detected a hypervisor, it only slept briefly before continuing.
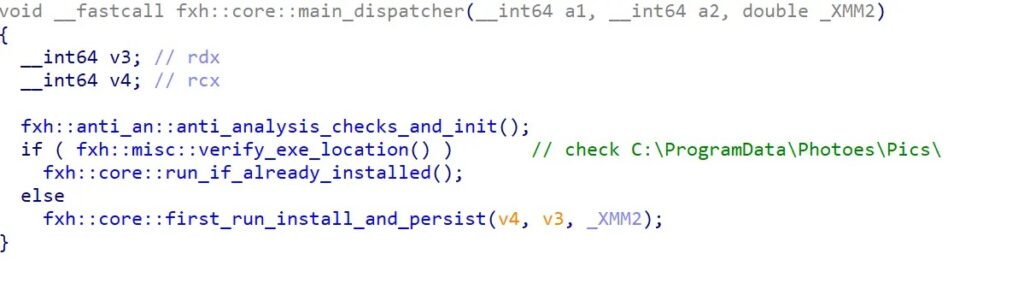
Researchers also pointed to coding mistakes. One example involved the malware decrypting its configuration to disk in cleartext before encrypting and saving a second copy, then deleting the original. Elastic said several rough edges, the use of free dynamic DNS services in earlier versions, and the lack of a kill switch all support the view that the malware author may not be highly experienced.
That does not make the threat harmless. Low sophistication can still cause serious damage when the malware has persistence, keylogging, payload delivery, USB propagation, and broad file theft. In a financial environment, that mix can expose credentials, internal records, and operational data in a single intrusion.
What defenders should do now
Financial organizations should monitor for suspicious scheduled tasks, especially MSGraphics and MSRecorder, and investigate unusual executions of rundll32.exe tied to user-writable directories. Those behaviors match the persistence and payload execution chain Elastic documented in the case.
Security teams should also review USB activity closely. BRUSHWORM’s removable-media propagation and offline file copying make endpoint visibility around drive insertions, new executable creation, and unusual file staging especially important in environments that depend on portable storage.
Elastic published YARA rules for both malware families, which gives defenders a practical starting point for hunting across endpoints and related infrastructure. Organizations that restrict unsigned binaries, inspect DLL side-loading behavior, and tighten user access to removable media will reduce the chances of a repeat attack.
Quick takeaways
- BRUSHWORM acted as the main backdoor and handled persistence, C2 traffic, payload downloads, USB spread, and file theft.
- BRUSHLOGGER captured keystrokes and active window titles through DLL side-loading.
- The malware targeted a South Asian financial institution and focused on both online and offline exfiltration.
- Elastic found signs of active development, including earlier test builds uploaded to VirusTotal.
- Elastic released detection guidance and YARA rules to help defenders hunt the malware.
FAQ
BRUSHWORM is the main malware implant Elastic found in the attack. It acts as a modular backdoor that installs itself, persists on the system, communicates with a remote server, downloads extra payloads, spreads through USB drives, and steals files.
BRUSHLOGGER is a separate keylogger that masquerades as libcurl.dll through DLL side-loading. It records keystrokes and logs the active window title for context.
Elastic Security Labs said the malware targeted a South Asian financial institution. The public report did not name the victim.
BRUSHWORM can copy itself to removable drives and can also move stolen files onto those drives when internet access is unavailable. That gives the attacker a way to spread or exfiltrate data through physical media.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages