CanisterWorm is hitting Docker, Kubernetes, and Redis to spread and steal secrets

CanisterWorm is a self-propagating malware campaign tied to TeamPCP, a financially motivated threat group that has targeted exposed cloud services since late 2025. Security researchers say the worm looks for weak or exposed Docker APIs, Kubernetes clusters, Redis servers, and systems vulnerable to React2Shell, then uses that access to move deeper into cloud environments and steal secrets.
This is not just another one-off cloud malware story. The same campaign has overlapped with major supply chain incidents involving Aqua Security’s Trivy project, and researchers say stolen credentials from those compromises helped TeamPCP expand into open source ecosystems and cloud build pipelines.
Why it matters is simple. Once the worm gets into a misconfigured cloud environment, it can steal credentials, spread laterally, and give attackers a path to more systems, more secrets, and more damage. KrebsOnSecurity says TeamPCP also used Telegram for extortion and later added destructive behavior aimed at systems linked to Iran.
What researchers say TeamPCP is targeting
KrebsOnSecurity reports that TeamPCP began compromising corporate cloud environments in December 2025 by going after exposed Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell flaw. The report says the group focused on cloud control planes and used those footholds to move laterally and siphon credentials.
Aikido later tied TeamPCP to a worm it named CanisterWorm after detecting a burst of npm package compromises on March 20, 2026. The company said the worm used an Internet Computer Protocol canister as a command channel, which Aikido described as the first time it had seen that design in a campaign like this.
Krebs also cited January research from Flare saying Azure made up 61% of compromised servers and AWS another 36%, for a combined 97% of observed victim infrastructure. That breakdown helps explain why cloud defenders should treat this as a control-plane and identity problem as much as a malware problem.
CanisterWorm at a glance
| Area | What has been reported |
|---|---|
| Threat group | TeamPCP |
| Main targets | Exposed Docker APIs, Kubernetes clusters, Redis, React2Shell-exposed systems |
| Main goal | Credential theft, lateral movement, extortion, and in some cases destructive activity |
| Notable spread method | Self-propagating worm behavior in cloud and package ecosystems |
| Infrastructure twist | ICP canister-based command and fallback infrastructure |
| Cloud concentration | Krebs cites Flare data showing Azure and AWS made up 97% of observed compromised servers |
The Trivy compromise made the campaign more dangerous
The wider CanisterWorm story became more serious after the Trivy supply chain attack. Aqua Security said a threat actor used compromised credentials on March 19, 2026 to publish malicious Trivy v0.69.4 releases and compromise the trivy-action and setup-trivy GitHub Actions. Aqua said affected environments should treat all accessible secrets as exposed.
GitHub’s advisory for the Trivy incident says the attackers force-pushed 76 of 77 tags in trivy-action, replaced all seven tags in setup-trivy, and later pushed malicious Trivy Docker images 0.69.5 and 0.69.6 to Docker Hub on March 22. The same advisory tells users to rotate pipeline secrets immediately if they ran affected versions.
Wiz then reported that TeamPCP expanded into the npm ecosystem using CanisterWorm and stolen publish tokens. Wiz also said the attackers used an ICP-hosted fallback command path serving an evolving payload called kamikaze.sh, which showed the campaign was still active and adapting after the first disclosures.
Why the blockchain-backed infrastructure stands out
Aikido says CanisterWorm used an Internet Computer Protocol canister for its command-and-control dead drop. That matters because ICP canisters are distributed and harder to take down than an ordinary rented server, which gives attackers a more durable way to host commands or payload references.
Wiz separately observed an ICP-hosted fallback C2 during the Trivy follow-on activity, which supports the view that TeamPCP used decentralized infrastructure as part of the campaign. Wiz later said that canister became unavailable due to a policy violation, but the use of that model itself still stands out.
This does not mean blockchain makes malware unstoppable. It does mean defenders may face slower or less familiar takedown options when attackers move key infrastructure away from ordinary hosting providers. In this case, researchers watched TeamPCP keep iterating as the campaign spread across supply chain and cloud targets.
What defenders should check first
- Exposed Docker APIs and unauthenticated Redis access
- Publicly reachable Kubernetes control paths
- Secrets used in Trivy-related CI/CD workflows during the March 19 to March 23 window
- Mutable GitHub Action tag references instead of commit-SHA pinning
- Signs of lateral movement and new publish activity in npm, PyPI, or container registries
The Iran-linked wiper behavior marks an escalation
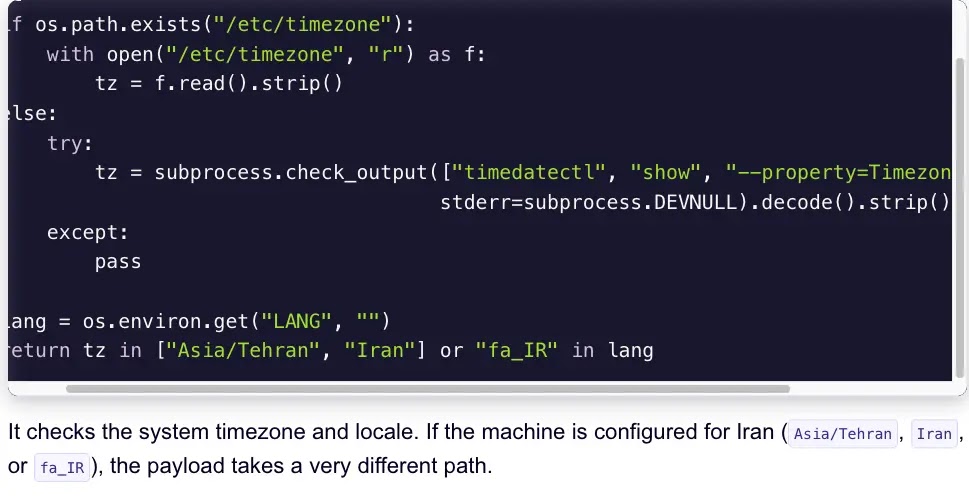
KrebsOnSecurity reported on March 23 that TeamPCP added a wiper that destroys data on infected systems using Iran’s time zone or Farsi as the default language. The report says experts saw the destructive activity over the preceding weekend and linked it to the same group behind the data theft and extortion campaign.
Krebs also reported that if the malware detects a Kubernetes cluster in that environment, it attempts to destroy data across every node in the cluster. If it does not find a cluster, it wipes the local system instead.
That shift matters because it shows a campaign that started around cloud compromise and credential theft can also pivot into destructive action. Security teams should not assume TeamPCP will stay limited to financial theft if the attackers see a political or opportunistic angle.
What organizations should do now
If your team used Trivy, trivy-action, or setup-trivy in the affected exposure windows, rotate every secret those workflows could access. Aqua and GitHub both say exposed environments should assume compromise and move quickly on credential hygiene.
Cloud teams should also audit Docker, Kubernetes, and Redis exposure right away. The CanisterWorm reporting points to misconfigurations and exposed services as major entry paths, not some brand-new zero-day that only a few defenders can see.
Finally, pin GitHub Actions to commit SHAs, review recent package publishing activity, and watch for suspicious outbound traffic tied to known indicators from the Trivy incident. Aqua specifically recommended safe pinned versions, while GitHub’s advisory also published the malicious C2 domain and IP to block.
FAQ
CanisterWorm is a self-propagating malware campaign linked to TeamPCP. Researchers say it targets exposed cloud services and can spread through package ecosystems after stealing publish credentials.
Reported targets include exposed Docker APIs, Kubernetes clusters, Redis servers, and systems vulnerable to React2Shell.
Aqua, GitHub, and Wiz say attackers used compromised credentials to publish malicious Trivy releases and tamper with GitHub Actions, exposing secrets that helped fuel follow-on attacks.
Researchers say TeamPCP used ICP canisters as part of its command setup. That can make attacker infrastructure harder to disrupt than a normal hosted server.
Yes, according to KrebsOnSecurity’s March 23 report. It says the destructive payload activates on systems set to Iran’s time zone or Farsi.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages