Censys warns 5,219 Rockwell and Allen-Bradley PLCs are exposed as Iranian cyber activity targets critical infrastructure
U.S. cybersecurity and national security agencies are warning that Iranian-affiliated threat actors are actively targeting internet-facing Rockwell Automation and Allen-Bradley programmable logic controllers across critical infrastructure. The joint alert says the activity is ongoing and affects sectors that include water, energy, and government facilities.
That warning matters because these PLCs control real-world industrial processes. When attackers gain access, they can do more than steal data. They can interfere with operations, change logic, and disrupt how operators see or manage industrial systems.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Censys says it found 5,219 internet-exposed hosts worldwide that respond to EtherNet/IP on port 44818 and identify themselves as Rockwell Automation or Allen-Bradley devices. The United States accounts for 3,891 of those systems, or about 74.6% of the total exposed footprint.
Why this campaign stands out
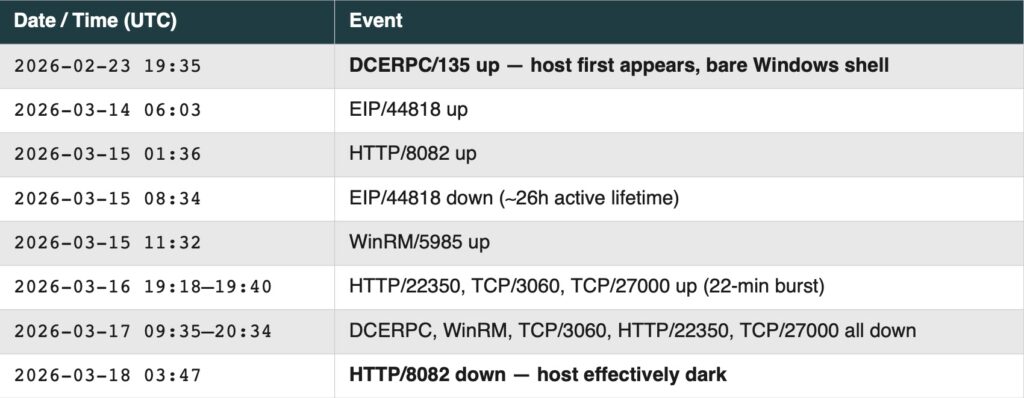
The campaign does not appear to rely on a zero-day vulnerability. Instead, the joint advisory says the threat actors are exploiting internet-facing PLCs directly, while Censys reports that the group can use legitimate Rockwell engineering software to interact with exposed devices and related project files. That makes the activity more dangerous because it can blend in with normal administration.
The agencies link the operation to Iranian-affiliated actors associated with the IRGC Cyber Electronic Command. The same cluster has been tracked under names such as CyberAv3ngers, Shahid Kaveh Group, Storm-0784, Bauxite, and UNC5691. Officials also connect this activity to earlier attacks on Unitronics PLCs in U.S. water and wastewater systems.
The advisory names CompactLogix and Micro850 as confirmed targets. It also notes that threat actors have been probing additional OT protocols, including Modbus on port 502 and S7 on port 102, which suggests the targeting may not stop with one vendor family.
What the exposure data shows
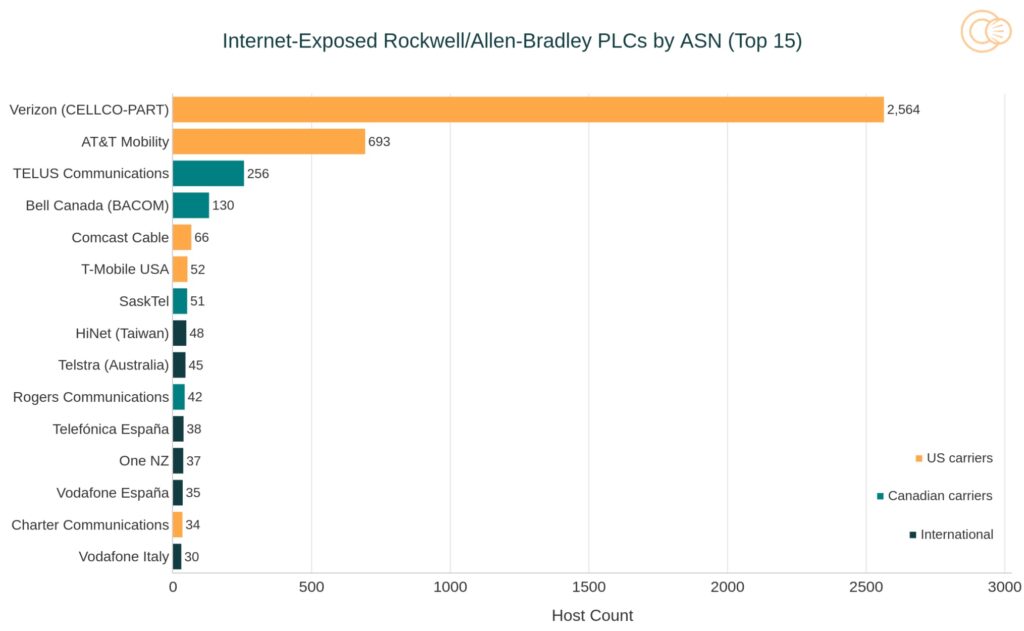
Censys found that a large share of exposed devices sits behind carrier networks rather than traditional enterprise infrastructure. Verizon Business accounts for 2,564 exposed hosts, or 49.1% of the global total, while AT&T Mobility accounts for another 693, or 13.3%. That pattern points to field deployments connected through cellular modems, including remote facilities that may lack strong segmentation or monitoring.
The geographic breakdown outside the United States also shows notable exposure in Spain, Taiwan, and Italy. Censys says this reflects a broad attack surface rather than a narrow domestic issue, even though the U.S. remains the clear primary concern in the current advisory.
Researchers also found other services exposed alongside PLC interfaces. Censys reported 771 instances with VNC, 280 with Telnet, and 292 with Modbus. Those extra services create more ways in, especially in environments where remote access tools and engineering workstations sit too close to operational assets.
Key numbers at a glance
| Metric | Finding |
|---|---|
| Total exposed Rockwell/Allen-Bradley hosts | 5,219 |
| Exposed hosts in the United States | 3,891 |
| U.S. share of global exposure | 74.6% |
| Hosts on Verizon Business | 2,564 |
| Hosts on AT&T Mobility | 693 |
| VNC co-exposures | 771 |
| Telnet co-exposures | 280 |
| Modbus co-exposures | 292 |
What organizations should do now
The most urgent step is simple. Remove PLCs from direct internet exposure wherever possible. The joint advisory makes clear that internet-facing OT devices remain a live target in this campaign.
Security teams should also review inbound traffic tied to the protocols named in the advisory, audit remote access paths, and shut down unnecessary services on adjacent systems. Censys specifically highlighted VNC and Telnet as common co-exposures, while the government alert points defenders toward known indicators and suspicious operator infrastructure.
For Rockwell environments, defenders should pay close attention to engineering access, exposed HMIs, and aging deployments that may still rely on older firmware or weak remote connectivity. Rockwell’s own product pages show that Studio 5000 Logix Designer is central to managing Logix controllers, which helps explain why misuse of legitimate tooling is such an operational risk in this case.
Immediate defensive priorities
- Remove internet-facing PLC access where possible.
- Disable unnecessary remote services such as VNC and Telnet.
- Review exposure on ports 44818, 502, 102, 2222, and 22.
- Audit cellular modem deployments and field-connected OT assets.
- Restrict engineering workstation access and enforce MFA for remote OT administration.
- Investigate any overlap with indicators listed in the government advisory.
FAQ
Yes. The April 7, 2026 joint advisory says Iranian-affiliated cyber actors are actively exploiting internet-facing PLCs across U.S. critical infrastructure.
Censys reported 5,219 internet-exposed hosts worldwide that identify as Rockwell Automation or Allen-Bradley devices, with 3,891 located in the United States.
The current reporting does not point to a zero-day. The concern centers on direct access to exposed systems and the abuse of legitimate engineering tools and weak remote connectivity.
The joint advisory highlights critical infrastructure, including water, energy, and government-related environments, especially where PLCs remain reachable from the public internet.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages