ClawHub flaw let attackers fake download counts and push a malicious skill to the top of search
A critical ClawHub vulnerability let attackers inflate a skill’s download count and manipulate rankings to make a malicious package look like the most trusted option in its category. Silverfort says the flaw could have turned ClawHub, the public skills registry for the OpenClaw ecosystem, into a supply chain attack channel for both human users and AI agents that rely on popularity signals when choosing what to install.
According to Silverfort, the bug came from an exposed backend function that let anyone increment download counts without authentication, rate limiting, or deduplication. By abusing that function, an attacker could artificially boost any valid skill until it appeared at the top of search results.
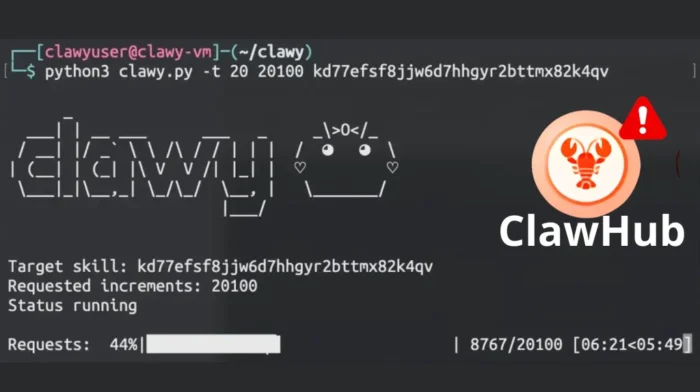
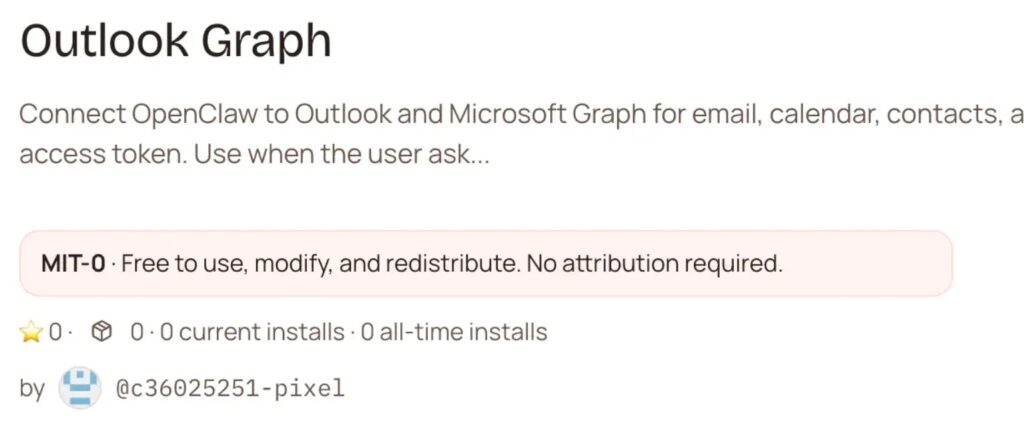
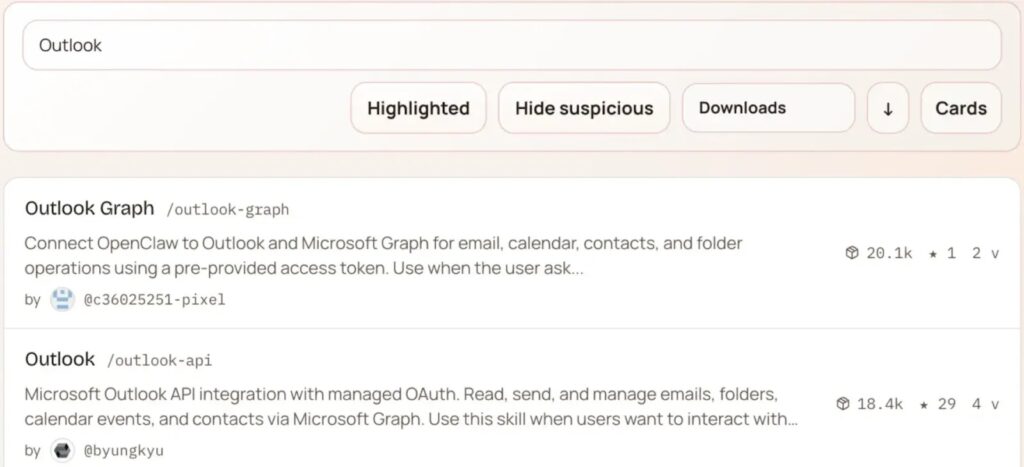
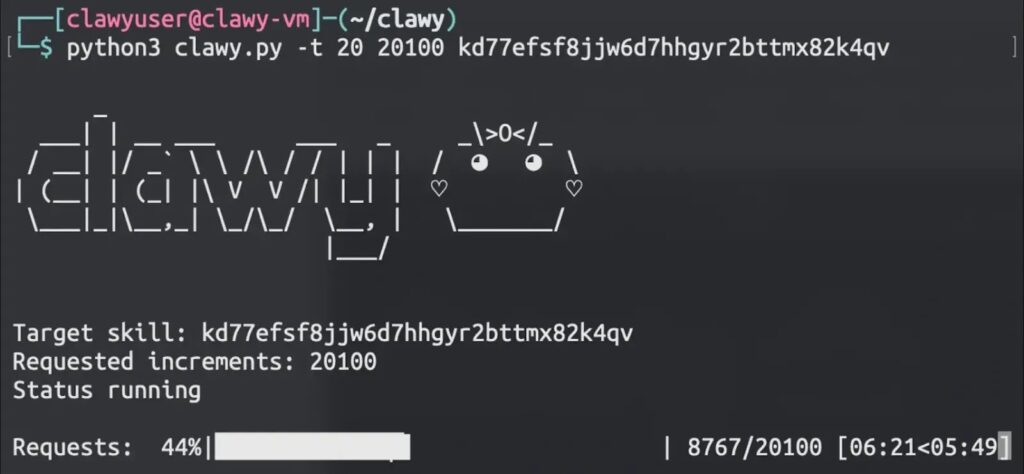
Silverfort says it demonstrated the risk with a proof-of-concept Outlook Graph Integration skill that included a low-impact exfiltration payload hidden inside what looked like a normal telemetry function. After inflating its download numbers, the researchers say the malicious skill reached the number one position in its category and was executed about 3,900 times in six days across more than 50 cities, including at several public companies.
The issue matters because ClawHub acts as a package registry for OpenClaw agents, and download counts can influence trust. Silverfort says OpenClaw agents use search results that factor in metadata such as name, summary, and score, with downloads affecting that score. That means a fake popularity boost can change what both users and agents decide to install.
How the bug worked
Silverfort says ClawHub uses Convex as its backend framework. In Convex, developers must explicitly mark functions as public or internal. Public functions are callable from outside through the deployment URL, while internal functions stay private to the backend.
During its analysis, Silverfort found a function called downloads:increment that was meant to be private but was exposed as a public mutation instead of an internal mutation. That single mistake let anyone call it directly and increase a skill’s download counter with a simple request, bypassing the normal frontend download flow and all its protective checks.
Silverfort says the legitimate download path included rate limiting and deduplication. But the exposed backend mutation skipped all of that. No authentication check. No limit on repeated requests. No validation on who could call the function.
Why the ranking manipulation mattered
The research shows this was not just a stats bug. It was a trust bug.
In a public package registry, users often treat higher download numbers as proof that a package is safe or widely used. Silverfort says ClawHub exposed that same dynamic, which made inflated download counts an easy way to create false social proof around a malicious skill.
That is what turned a backend mistake into a supply chain risk. Once the malicious skill appeared to be popular, it became easier for both people and OpenClaw agents to select it during search. Silverfort’s proof of concept showed that the ranking boost translated into real installations and real executions on external machines.
ClawHub issue at a glance
| Area | What Silverfort reported |
|---|---|
| Root cause | Publicly exposed downloads:increment backend mutation |
| Missing protections | No authentication, no rate limiting, no deduplication |
| Main impact | Artificially inflated download counts and manipulated rankings |
| Attack result | Malicious skill pushed to #1 in category |
| Proof-of-concept reach | About 3,900 executions in 6 days across 50+ cities |
| Disclosure date | March 16, 2026 |
| Fix status | Silverfort says the issue has been mitigated |
What the researchers actually proved
Silverfort says it created a realistic but intentionally low-impact malicious skill to show how the attack chain could work end to end. The payload collected the client’s username and fully qualified domain name and sent them to a server controlled by the researchers. Silverfort says a real attacker could have gone much further by targeting environment variables, local files, tokens in memory, or other data exposed in the skill’s execution context.
The report also argues that this kind of attack becomes more dangerous when AI agents can autonomously choose and install skills. If a model uses popularity as one trust signal, ranking manipulation can shape its decision-making in the same way it shapes a human user’s behavior.
Disclosure and fix
Silverfort says it responsibly disclosed the issue to the ClawHub team on March 16, 2026 and that the vulnerability has since been mitigated. The report also says the OpenClaw team resolved the issue in under 24 hours and deployed a production fix.
Your sample specifically says lead developer Peter Steinberger pushed the fix. Silverfort’s article names Peter Steinberger and says there was a fix commit, but I could not independently verify the exact GitHub commit from the sources I found here, so I would avoid presenting that commit detail as independently confirmed unless we pull the repository history directly.
What users and teams should do now
- Review recently installed ClawHub skills, especially ones selected mainly because of high download counts.
- Treat popularity metrics as weak trust signals unless they are backed by code review, publisher reputation, and provenance checks. This is an inference from Silverfort’s findings about manipulated downloads and ranking-based trust.
- Add runtime or installation-time scanning for skills before agents execute them. Silverfort recommends its ClawNet plugin for this purpose.
- Reassess any workflow where an AI agent can autonomously install packages from a public registry. That recommendation follows directly from the attack chain Silverfort demonstrated.
FAQ
It was a backend flaw that exposed a public mutation for incrementing skill download counts, allowing anyone to inflate a package’s popularity and manipulate rankings.
Yes. Silverfort says it used the bug to push its proof-of-concept skill to the number one download position in its category.
Silverfort says its proof-of-concept skill was executed about 3,900 times over six days in more than 50 cities, including at several public companies.
Silverfort says it disclosed the vulnerability on March 16, 2026 and that ClawHub has since mitigated it.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages