Cortex XDR Live Terminal Abuse Lets Hackers Use EDR for Stealthy C2 Control

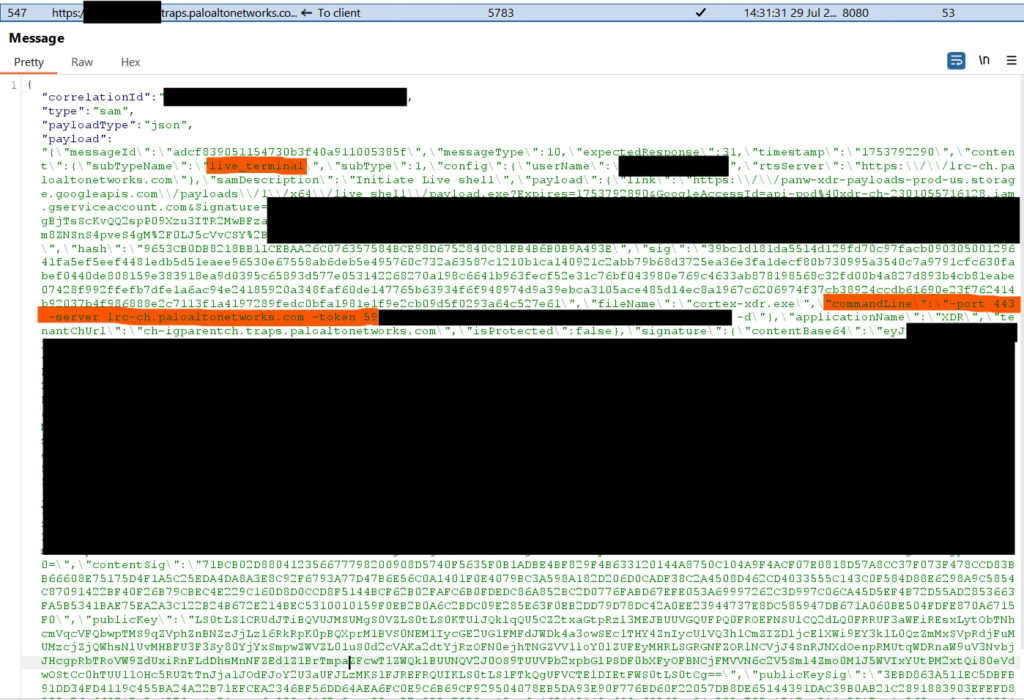
]Hackers can hijack Palo Alto Networks’ Cortex XDR Live Terminal feature for command-and-control communications. The trusted EDR tool runs attacker commands without detection. InfoGuard Labs states: “No command signing allows WebSocket redirection to attacker servers.”
Live Terminal lets admins run PowerShell, Python, file ops remotely via WebSocket to Palo Alto cloud. Attackers exploit missing validation. They redirect connections to their servers since cortex-xdr-payload.exe trusts .paloaltonetworks.com endings in full URLs.
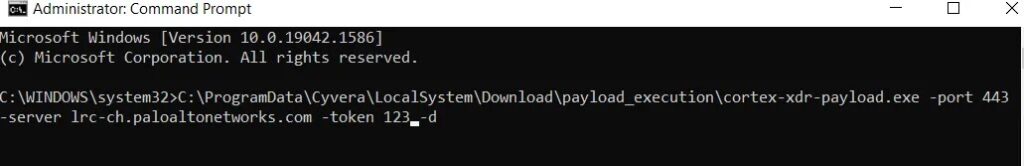
Two abuse methods exist. Cross-tenant attacks use stolen session tokens to link victim endpoints to attacker Cortex tenants. Custom servers mimic WebSocket protocol with minimal code. Both bypass EDR blocks as trusted processes.
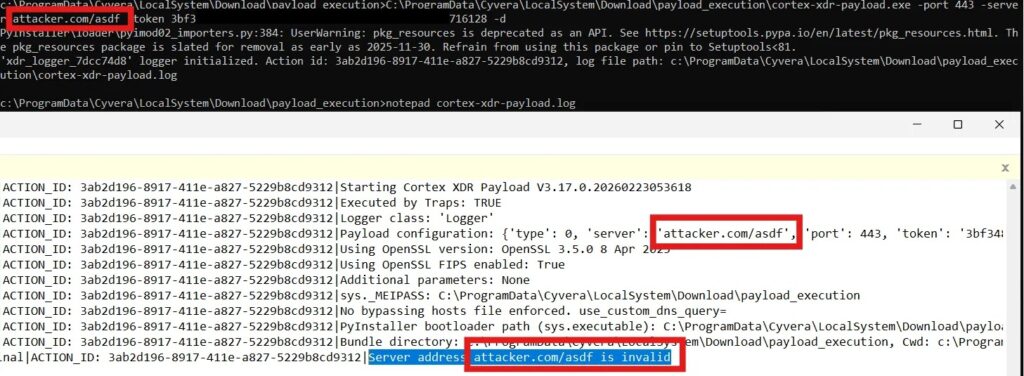
Researchers decompiled the Python 3.12 payload. The run_lrc_payload function checks full URLs, not hostnames. attacker.com/test.paloaltonetworks.com fools it. Traffic blends with normal agent flows, skipping TLS inspection.
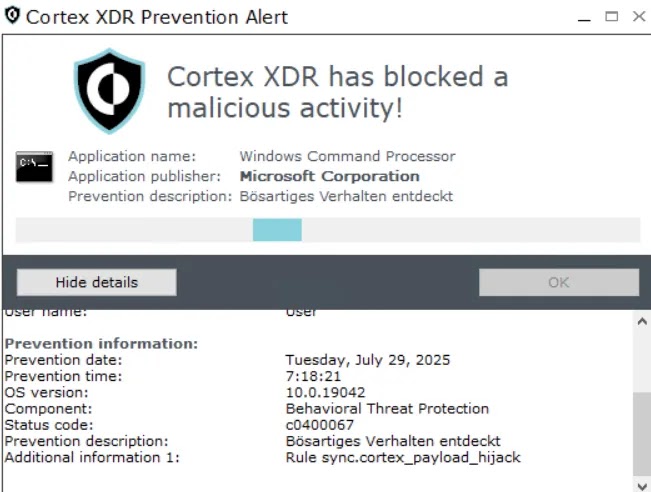
Palo Alto got notified September 30, 2025. Versions 8.7-8.9 claim fixes. Tests on February 23, 2026, with 8.9.1 show flaws persist. Parent process cyserver.exe should spawn payloads; deviations signal abuse.
Enterprises face stealth persistence. Attackers issue commands, grab files, move laterally via “living off the land.” No new malware needed.
Attack Methods Table
| Method | Technique | Requirements |
|---|---|---|
| Cross-Tenant | Steal WebSocket token, redirect to attacker’s Cortex | Valid session from own tenant |
| Custom Server | Mimic Palo Alto WebSocket protocol | Traffic capture, basic server setup |
Key Technical Flaws
Exploitable weaknesses.
- No command signing or mutual auth.
- URL validation checks full string vs hostname.
- Trusted EDR process skips prevention rules.
- WebSocket traffic excluded from inspection.
Detection Rules
Monitor now.
- Flag cortex-xdr-payload.exe with non-cyserver.exe parent.
- Watch WebSocket redirects to odd .paloaltonetworks.com URLs.
- Alert unusual Live Terminal sessions.
- Hunt process creation events daily.
Mitigation Steps
Secure your deployment.
- Update beyond 8.9.1; verify fixes.
- Enable full TLS inspection on agent traffic.
- Lock Live Terminal to admin-only IPs.
- Add behavioral blocks on payload spawns.
- Request Palo Alto protocol redesign.
FAQ
Redirect WebSocket to attacker servers; no signing validation.
No; tests show bypass still works as of Feb 2026.
cortex-xdr-payload.exe not spawned by cyserver.exe.
Trusted EDR traffic blends; skips inspection rules.
Add mutual auth, hostname-only validation, command signing.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages