Coruna iOS kit reuses Triangulation exploit code as mass attacks widen
Kaspersky says the Coruna iOS exploit kit uses an updated version of the same kernel exploit framework seen in Operation Triangulation in 2023. The company now says the overlap goes beyond shared bugs and points to the same author or development lineage behind both toolsets.
That matters because Coruna no longer looks like a tightly controlled espionage tool. Google said it first saw the kit in targeted operations tied to a customer of a surveillance vendor, then in watering hole attacks against Ukrainian users, and later in broader campaigns run by a financially motivated China-based threat actor.
In plain terms, a framework once associated with high-end spy activity now appears in wider criminal use. Kaspersky said Coruna is a maintained evolution of the Triangulation framework, while Google and iVerify have both described a shift from niche deployment to broader exploitation.
Why researchers now link Coruna to Triangulation
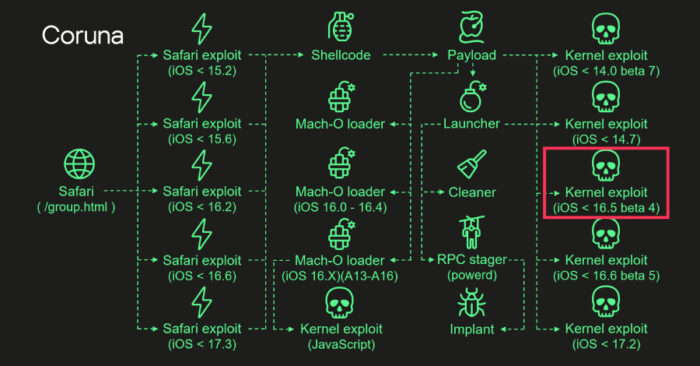
When Google and iVerify first published on Coruna in early March, the public evidence showed a powerful iPhone exploit kit with five full exploit chains and 23 exploits targeting devices from iOS 13.0 through iOS 17.2.1. At that point, shared vulnerabilities alone did not prove the same developers built both systems.
Kaspersky says the picture changed after it obtained and analyzed Coruna binaries. Its researchers concluded that the kernel exploit used for CVE-2023-32434 and CVE-2023-38606 in Coruna is an updated version of the exploit used in Operation Triangulation, and that Coruna also contains four more kernel exploits built on the same framework.
The company also found support in the code for newer Apple chips, including A17, M3, M3 Pro, and M3 Max, along with checks for newer iOS builds. Kaspersky says those additions show active maintenance rather than a recycled public toolkit stitched together from old research.
How the Coruna attack chain works
Researchers say Coruna starts when a victim opens a malicious or compromised website in Safari. A stager fingerprints the browser and device, selects the right remote code execution and pointer authentication bypass components, then hands off to a payload that starts kernel exploitation.
Kaspersky said the payload then downloads more components, executes kernel exploits, chooses the right Mach-O loader for the device and firmware, and runs a launcher that installs the final implant and removes traces of exploitation. That design helps the kit scale across different iPhone models and software versions.
Google’s earlier reporting said the full Coruna package showed how sophisticated mobile exploitation can spread from a surveillance vendor customer to a suspected Russia-linked espionage group and then to a broader criminal operator. That timeline has become more important now that Kaspersky says the framework itself traces back to Triangulation.
Coruna at a glance
| Item | Verified detail |
|---|---|
| Exploit kit name | Coruna |
| First public reporting | March 2026 by Google Threat Intelligence Group, with parallel iVerify analysis |
| Supported target range | iPhones running iOS 13.0 through 17.2.1 |
| Number of full exploit chains | Five |
| Total exploits in kit | 23 |
| Key new Kaspersky finding | One Coruna kernel exploit is an updated version of a Triangulation exploit; four more share the same framework |
| Noted newer chip support | A17, M3, M3 Pro, M3 Max |
Why this raises the stakes for iPhone users
The new Kaspersky findings suggest Coruna did not simply borrow ideas from Triangulation. The firm says it reflects continued development of the same exploitation framework, which means elite mobile attack tooling can survive disclosure, evolve, and move into new hands.
That risk has grown even more serious because another advanced iPhone exploit chain, DarkSword, has also spread across multiple actors and a newer version leaked on GitHub in March. Google said DarkSword has appeared in campaigns since at least November 2025, and TechCrunch reported that leaked samples were easy to reuse against devices running older Apple software.
Apple has already patched Coruna-related flaws in supported software over time, and Apple told TechCrunch it issued emergency updates on March 11 for devices that cannot run recent iOS versions. Even so, older or unpatched devices remain the weak spot, especially when high-end exploit frameworks start moving from targeted espionage into broader criminal use.
What security teams should watch
- Safari-based one-click exploit delivery through compromised websites remains a key risk path.
- Older iPhones and iPads on outdated iOS versions face the highest exposure.
- Shared tooling across espionage and criminal campaigns suggests a growing resale market for advanced mobile exploits.
- Fast patching matters more now because exploit frameworks are getting easier to reuse across actors.
FAQ
Coruna is a sophisticated iOS exploit kit that researchers say contains five full exploit chains and 23 exploits used to compromise iPhones through malicious web content.
Kaspersky says one of Coruna’s kernel exploits is an updated version of the exploit used in Triangulation, and that the broader exploitation framework shares common code and design.
Google and iVerify said Coruna targeted Apple devices running iOS 13.0 through 17.2.1.
Because the framework appears to have moved from selective espionage use into wider campaigns, including mass exploitation tied to financially motivated actors.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages