Critical LangSmith flaw allowed account takeover through malicious links
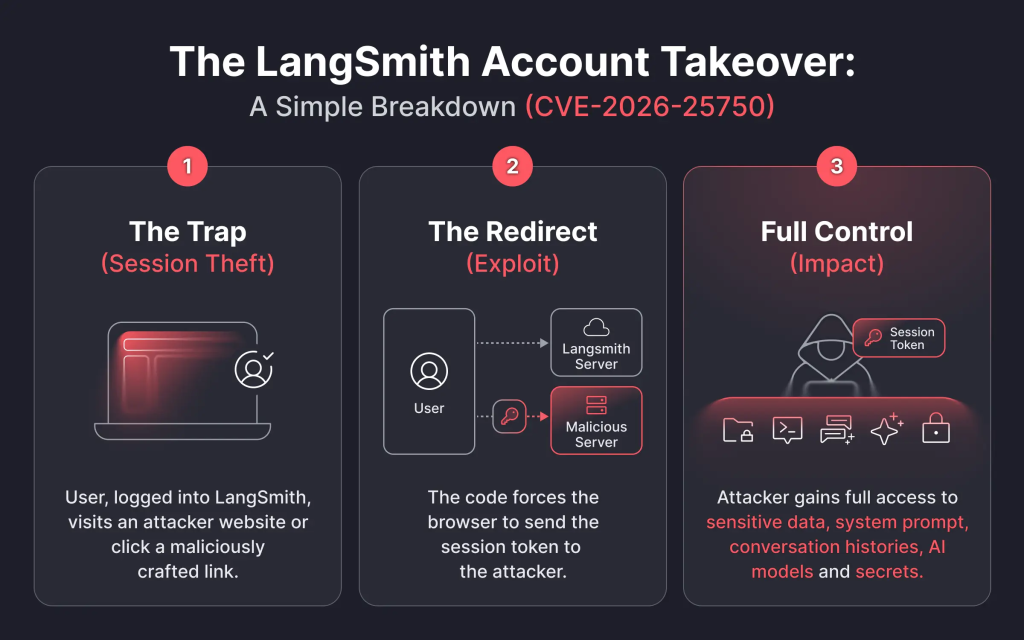
A critical vulnerability in LangSmith could let attackers steal session tokens and take over user accounts if a logged-in user clicked a specially crafted link. The flaw, tracked as CVE-2026-25750, affected both LangSmith Cloud and self-hosted deployments before fixes were rolled out.
The issue centered on LangSmith Studio’s baseUrl handling. Before the fix, an attacker could abuse that parameter to make a victim’s browser send requests, including authentication data, to an attacker-controlled server. With the stolen bearer token, the attacker could access the same LangSmith resources and actions available to the victim inside their workspace.
That made the bug especially serious for enterprise AI teams. LangSmith sits close to debugging, tracing, and observability workflows for large language model applications, so a compromised account could expose sensitive trace data, internal workflows, and proprietary prompts. Miggo, which discovered the bug, said LangChain remediated the cloud service on December 15, 2025, and later shipped a patch for self-hosted deployments.
What happened
According to the published CVE details, the bug was a URL parameter injection flaw in LangSmith Studio. An authenticated user who clicked a malicious link could have their bearer token, user ID, and workspace ID sent to an attacker-controlled server. The attack required social engineering, such as phishing or a malicious link shared through email or chat.
Miggo’s research says the attack could also start when a logged-in victim visited a malicious website or a legitimate website compromised with hostile JavaScript. That script could then force the browser to load a crafted LangSmith Studio URL that pointed to an attacker-controlled backend.
Why this matters
An account takeover in LangSmith can expose more than normal profile data. Because LangSmith handles traces and observability data for AI applications, an attacker who gets in may gain access to execution histories, raw outputs, internal prompts, and other sensitive material tied to model behavior. That could include confidential business data if teams used LangSmith during debugging or monitoring of production systems.
The practical danger also comes from how little user interaction the attack needed. The victim did not have to manually type credentials into a fake login page. A single malicious link could have been enough while the user already had an active session.
Affected products and fixed versions
| Item | Status |
|---|---|
| LangSmith Cloud | Fixed by December 15, 2025 |
| Self-hosted LangSmith | Patch released December 20, 2025 |
| Vulnerable self-hosted versions | Prior to version 0.12.71 |
| Patched Helm chart line | langsmith-0.12.33 and later, according to Miggo |
| Exploitation in the wild | No evidence reported in the advisory |
These version and timeline details come from the CVE record and Miggo’s write-up.
What LangSmith users should do
- Self-hosted admins should upgrade immediately to the patched release line.
- Security teams should review whether users clicked suspicious LangSmith links shared in email, chat, or documentation portals. This is a reasonable defensive step based on the attack path described in the advisory.
- Organizations should rotate tokens or review session activity if they suspect exposure. This is an inference based on the fact that stolen bearer tokens enabled impersonation.
- Cloud customers do not need to take platform-side remediation steps because LangChain already fixed the hosted service, according to Miggo.
Key facts at a glance
| Detail | Information |
|---|---|
| CVE | CVE-2026-25750 |
| Vulnerability type | URL parameter injection |
| Main risk | Token theft and account takeover |
| User action needed | Clicking a crafted malicious link or loading a hostile page while logged in |
| Impact | Access to LangSmith resources within the victim’s workspace |
| Patched self-hosted version threshold | Prior to 0.12.71 were affected |
Source data comes from the CVE entry and Miggo’s research.
FAQ
Yes. The published CVE says both LangSmith Cloud and self-hosted deployments were affected before fixes were applied.
It required social engineering or a malicious link, but not the classic kind where the victim manually enters credentials into a fake page. The token theft could happen through the active session.
The advisory and follow-up research say there is no evidence of exploitation in the wild.
They should upgrade to the patched release immediately. The CVE record points to fixes after version 0.12.71, while Miggo also cites Helm chart langsmith-0.12.33 and later for protected deployments.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages