Cybercriminals abuse IRS and tax filing lures to push malware in new 2026 campaigns
DeepLoad is the more recent sample you shared earlier, but for this attached tax-season piece, the stronger angle is this: cybercriminals are using IRS, tax filing, W-2, and W-8BEN lures at scale in 2026 to push malware, remote monitoring tools, and credential theft pages. Proofpoint says it has tracked more than 100 tax-themed email campaigns so far this year, with a noticeable increase in attacks that abuse legitimate remote management software.
The immediate risk for businesses is straightforward. These messages do not always try to drop obvious malware first. In many cases, they push trusted remote access tools or fake login pages, which lets attackers blend into normal enterprise activity and steal credentials before defenders realize what happened.
This also lines up with the IRS’s own warning for the 2026 filing season. The agency says taxpayers should not click unsolicited links or open unexpected attachments that claim to come from the IRS, because they may lead to fake sites or install malicious software on the victim’s device.
Tax lures are driving more than fake refund scams
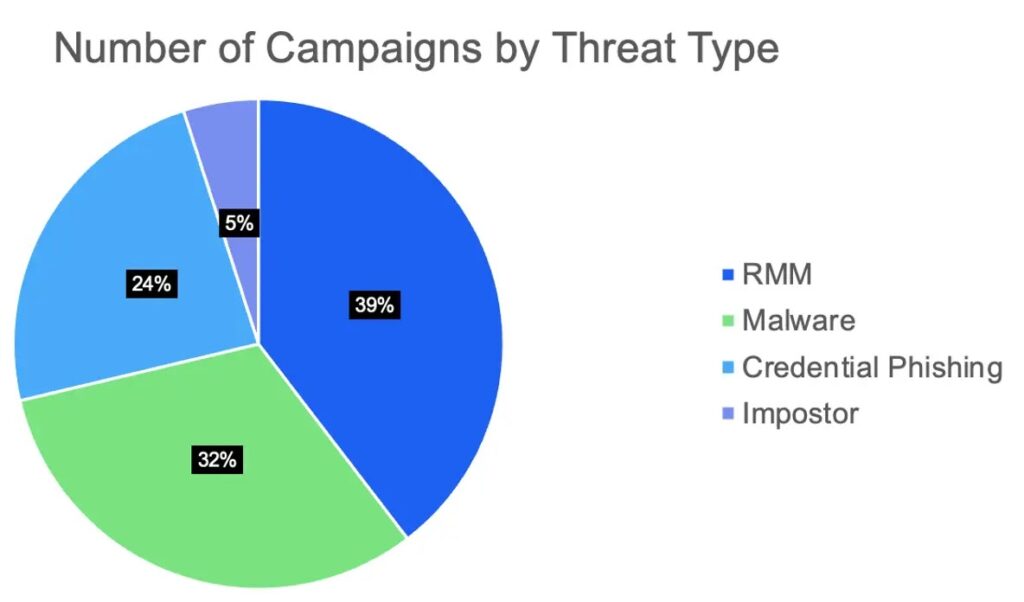
Proofpoint says malware and remote monitoring and management payloads now account for much of the tax-themed email activity it has observed in 2026. The campaigns mainly target users in the United States, but researchers also saw activity aimed at Canada, Australia, Switzerland, and Japan.
A key reason these campaigns work is trust. Attackers increasingly rely on legitimate software such as N-able, Datto, RemotePC, Zoho Assist, and ScreenConnect. Because these tools are real and digitally signed, many security products do not immediately treat them as malicious.
One example stood out in early February. Proofpoint says a campaign impersonating the IRS used a fake “Transcript Viewer” button that linked to a Bitbucket-hosted executable, which then installed N-able RMM on the victim’s machine. Researchers also noted that the email included a real IRS phone number to make the message look more convincing.
W-8BEN and HR-style lures widen the attack surface
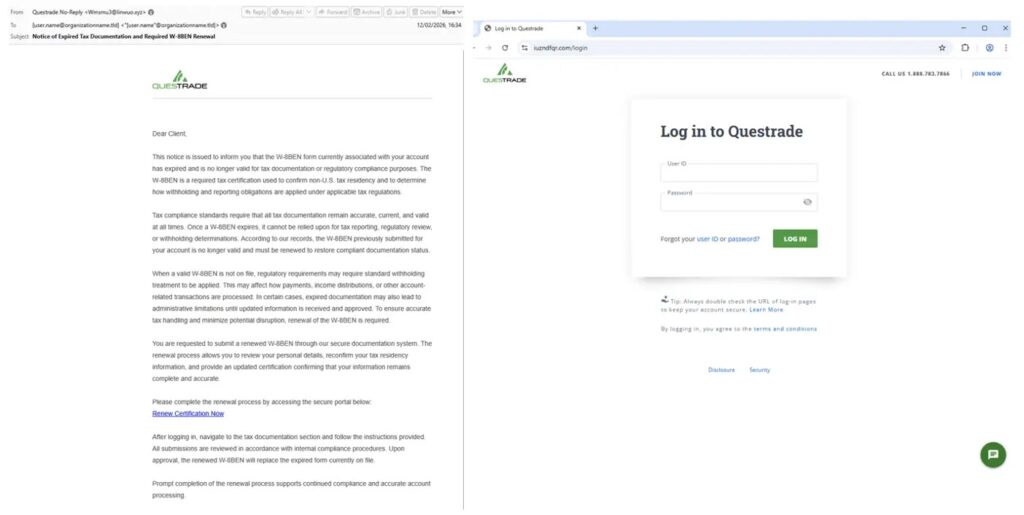
The tax-themed lures now go well beyond generic IRS notices. Proofpoint says attackers have used messages about expired tax documents, filing notices, W-2 requests from fake HR teams, and W-8BEN forms aimed at non-U.S. taxpayers. That broader playbook gives criminals more ways to match the target’s location, role, or business context.
Proofpoint also linked some of this activity to TA2730, a credential phishing group it has tracked since June 2025. In February 2026, the actor impersonated Swissquote in Switzerland and Questrade in Canada, pushing victims toward fake login pages designed to steal account credentials.
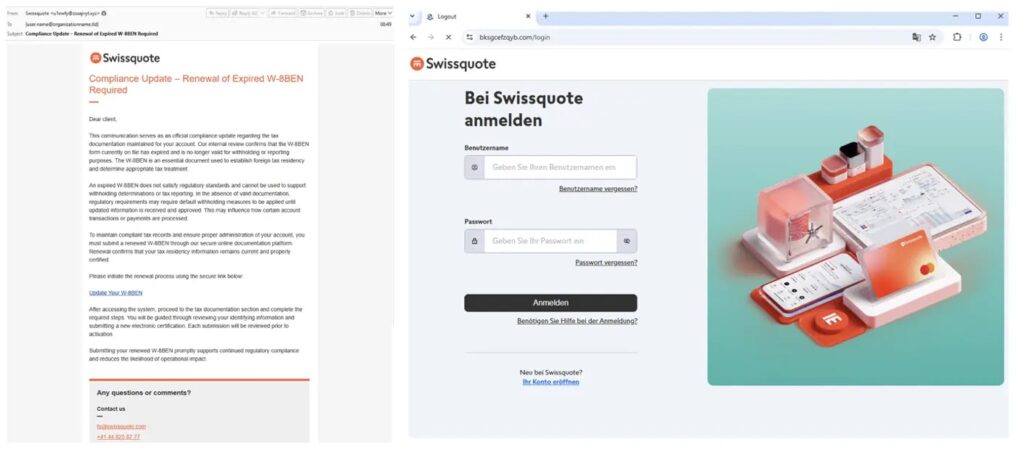
The IRS separately warns that suspicious W-8BEN messages should be reported because scammers use them in phishing attempts. Its guidance tells recipients not to trust unexpected messages and to send suspicious W-8BEN emails, faxes, or letters to [email protected] using “W8-BEN” in the subject line.
TA4922 uses a slower, more deliberate attack chain
Proofpoint says TA4922 has emerged as one of the more notable actors in this year’s tax-themed wave. The company describes the group as financially motivated and says it has tracked the actor since spring 2025. In 2026 campaigns, TA4922 reportedly impersonated tax authorities and used a multi-step social engineering process to build trust before sending malicious content.
The first stage often looks less aggressive than classic phishing. Researchers say the attacker sends an email that claims the target has unresolved tax obligations and asks for a mobile phone number. Once the victim moves the conversation out of email, the actor can pose as finance leadership or another trusted contact and deliver the real payload through a separate channel.
Proofpoint says TA4922 has primarily delivered malware from the Winos4.0 ecosystem, also known as ValleyRAT. In early March 2026, the company saw a related campaign spoof the Inland Revenue Department and lead victims to an information stealer that remained under investigation at the time of publication.
What defenders should know right now
The takeaway for enterprises is that tax-themed attacks now mix phishing, credential theft, and abuse of legitimate administration tools in the same campaign. That makes old advice like “watch for malware attachments” too narrow for 2026, because some of the most damaging payloads may arrive through signed remote access tools or fake portals instead.
The IRS says it generally contacts taxpayers by mail first, not through urgent email, text, or social media messages demanding action. The agency also says it does not send text messages without permission and urges people not to reply, click links, or open attachments in suspicious tax-related messages.

For companies, the practical response is to lock down which remote management tools can run, train employees to question tax-related messages that ask for personal contact details, and verify every unexpected tax request through official channels before anyone clicks or downloads anything.
Tax-themed malware campaigns in 2026 at a glance
| Area | What researchers observed | Why it matters |
|---|---|---|
| Campaign volume | Proofpoint tracked 100+ tax-themed campaigns in 2026 | Shows broad, active seasonal abuse |
| Main themes | IRS notices, W-2 requests, expired tax documents, W-8BEN lures | Attackers tailor messages to different users and regions |
| Payload types | Malware, RMM tools, credential phishing pages | Risk goes beyond fake refund scams |
| Common tools abused | N-able, Datto, RemotePC, Zoho Assist, ScreenConnect | Legit tools can slip past basic defenses |
| Key actors | TA4922 and TA2730 | Organized groups are behind part of the activity |
| Regions hit | U.S., Canada, Australia, Switzerland, Japan | Campaigns are not limited to one market |
How organizations can reduce the risk
- Allow only approved remote monitoring and remote access tools on corporate systems.
- Treat any email about tax filings, refunds, W-2s, or W-8BEN forms as suspicious until verified.
- Tell staff that the IRS warns against clicking unsolicited links or opening unexpected attachments.
- Verify tax and payroll requests through known internal contacts or official agency channels, not the message itself.
- Review endpoint detections for newly installed RMM software and unusual outbound access.
FAQ
Security researchers at Proofpoint say attackers are impersonating the IRS, tax authorities, and HR teams to deliver malware, remote access tools, and credential phishing pages.
Many campaigns use legitimate remote management software or fake login pages instead of obvious malware files, which can help attackers avoid immediate detection and gain persistent access.
The IRS says people should not click unsolicited links or open attachments in messages that claim to be from the agency. It also says it usually contacts taxpayers by mail first.
The IRS says not to reply, click links, or open attachments. Suspicious IRS-related phishing emails and messages can be reported to [email protected], and text messages can also be forwarded to 7726.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages