DarkSword iOS exploit chain used in real attacks to steal iPhone data

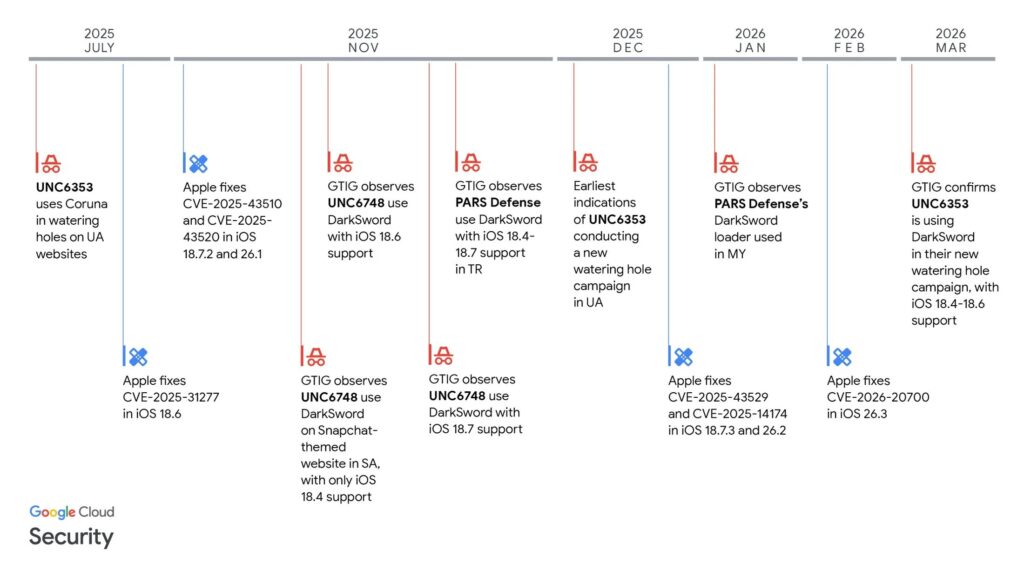
A newly disclosed iPhone exploit chain called DarkSword has been used in real-world attacks to fully compromise vulnerable devices and steal sensitive personal data. Google Threat Intelligence Group says multiple commercial surveillance vendors and suspected state-backed actors have used the chain since at least November 2025 against targets in Saudi Arabia, Turkey, Malaysia, and Ukraine.
DarkSword matters because it is a full-chain iOS exploit, not a single bug. Google says it strings together six vulnerabilities to move from browser-based code execution to sandbox escape and then to full kernel-level compromise on supported iOS versions.
The campaign also appears broader than a typical one-off spyware incident. Reuters, citing Google, Lookout, and iVerify, says the exploit was delivered through malicious or compromised websites and affected devices running exposed iOS 18 builds, with Apple stressing that the underlying flaws have already been fixed in later updates.
What DarkSword is and who used it
Google says DarkSword is the name it assigned to a new iOS full-chain exploit after finding matching toolmarks in recovered payloads. The company says several different operators adopted it, including suspected state-linked actors and commercial surveillance vendors.
Google specifically links one set of Turkey and Malaysia activity to Turkish commercial surveillance vendor PARS Defense. It also describes a separate Ukrainian watering-hole campaign tied to UNC6353 and another campaign tied to UNC6748.
That multi-actor use is one of the most important parts of this story. Google’s report suggests DarkSword did not stay in the hands of a single operator, which points to a wider exploit supply chain rather than one isolated espionage campaign. This is an inference drawn from Google’s finding that multiple distinct actors used the same exploit chain.
How the exploit chain works
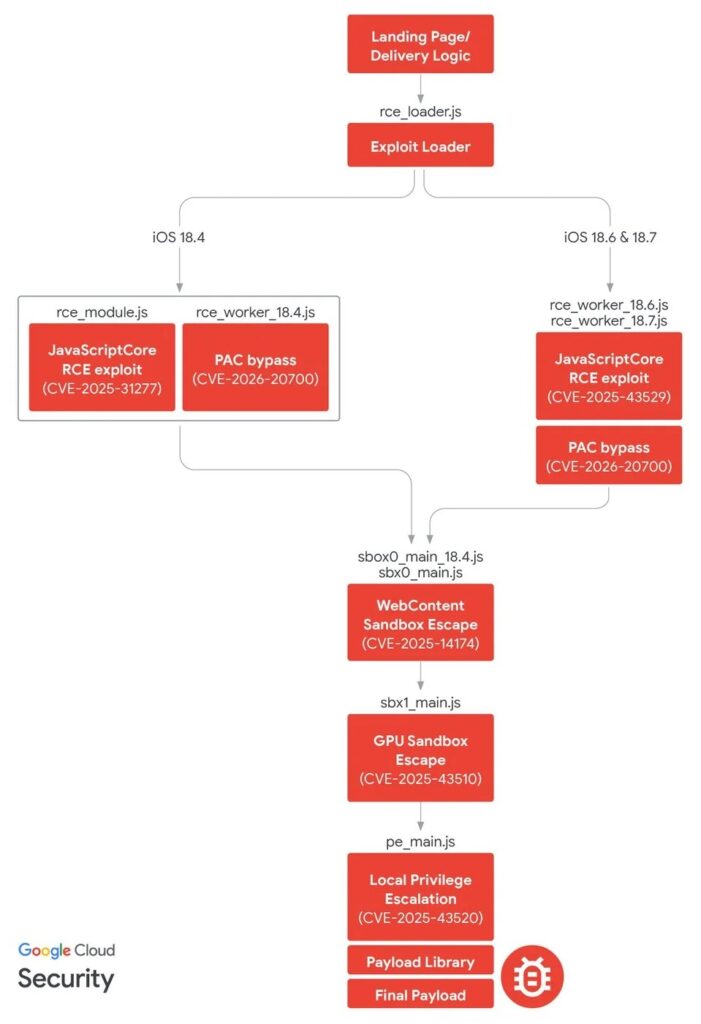
Google says DarkSword uses six vulnerabilities to fully compromise an iPhone. The chain starts with remote code execution in JavaScriptCore, moves through a PAC bypass in dyld, then uses sandbox escapes and kernel bugs to reach full device compromise.
Here are the six vulnerabilities Google documented:
| CVE | Component | Role in chain | Zero-day | Patched in |
|---|---|---|---|---|
| CVE-2025-31277 | JavaScriptCore | Initial RCE for older supported builds | No | iOS 18.6 |
| CVE-2025-43529 | JavaScriptCore | Initial RCE for iOS 18.6 to 18.7 | Yes | iOS 18.7.3, 26.2 |
| CVE-2026-20700 | dyld | User-mode PAC bypass | Yes | iOS 26.3 |
| CVE-2025-14174 | ANGLE | Sandbox escape via GPU process | Yes | iOS 18.7.3, 26.2 |
| CVE-2025-43510 | XNU kernel | Additional sandbox escape | No | iOS 18.7.2, 26.1 |
| CVE-2025-43520 | XNU kernel | Local privilege escalation and memory access | No | iOS 18.7.2, 26.1 |
Apple’s security notes confirm CVE-2026-20700 and state that Apple is aware of reports that it may have been exploited in an extremely sophisticated attack against targeted individuals on iOS versions before iOS 26. Apple also says CVE-2025-14174 and CVE-2025-43529 were addressed in response to the same report.
What data the malware tries to steal
Google says DarkSword delivered three different payload families: GHOSTKNIFE, GHOSTSABER, and GHOSTBLADE. Each one appears tuned to a different operator or mission.
According to Google and Reuters, the malware can steal signed-in account data, messages, browser information, location history, audio, wallet data, Safari artifacts, Health data, keychain-related information, and saved Wi-Fi credentials, depending on the payload used.
That makes this more than a browser exploit. It turns into full surveillance once the chain succeeds, with the exact collection set depending on which backdoor lands on the phone.
The biggest accuracy fix versus the sample
The sample says DarkSword compromises iPhones running iOS 18.4 through 18.7. Google’s technical report says DarkSword supports iOS 18.4 to 18.7, but Reuters reports researchers found it being delivered to users running iOS 18.4 to 18.6.2, and Google’s Ukraine-related UNC6353 activity only supported iOS 18.4 to 18.6. So the broader “18.4 through 18.7” range applies to the exploit family overall, but not every campaign or every observed delivery path.
What users should do now
- Update to the latest iOS version as soon as possible. Google and Apple both say the underlying vulnerabilities have been patched in later updates.
- Turn on Lockdown Mode if you cannot update right away and you face elevated risk. Google specifically recommends it.
- Avoid opening suspicious links, especially from social lures or unfamiliar sites. Reuters says one campaign involved compromised Ukrainian websites, while Google documented phishing and watering-hole style delivery.
- Treat outdated iPhones as higher risk. Apple says the attacks targeted out-of-date software.
FAQ
DarkSword is a full-chain iOS exploit that Google says multiple actors used to fully compromise vulnerable iPhones.
Yes. Google says it was used in distinct campaigns, and Reuters says coordinated research from Google, Lookout, and iVerify found it in active attacks.
Yes. Apple says the underlying vulnerabilities have been addressed across multiple updates, including iOS 26.3 for CVE-2026-20700.
Yes. Google says users who cannot update should enable Lockdown Mode for stronger protection.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages