DPRK Hackers Steal Record $2 Billion in Crypto Despite Bybit Breach Response

North Korea-linked operators stole $2 billion in cryptocurrency across 2025, marking their most aggressive year yet. The Bybit exchange hack on February 21, 2025, took $1.46 billion in a single blow, history’s largest confirmed crypto theft. Far from slowing down, DPRK groups intensified attacks through 2026. Elliptic’s full analysis confirms social engineering drives every major incident
January 2026 saw double the exploits compared to January 2025. Total known DPRK crypto theft now exceeds $6 billion. Funds directly finance weapons programs. Attackers expanded beyond exchanges to developers and contributors.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Social engineering remains the entry point. AI-generated fake identities fool even experts. Victims face convincing job offers or urgent tech fixes. Once engaged, malware grabs private keys instantly.
Bybit funds laundered through refund scams, junk tokens, and Chinese OTC desks. Over $1 billion cleaned by August 2025. Infrastructure matured post-Bybit, not declined.
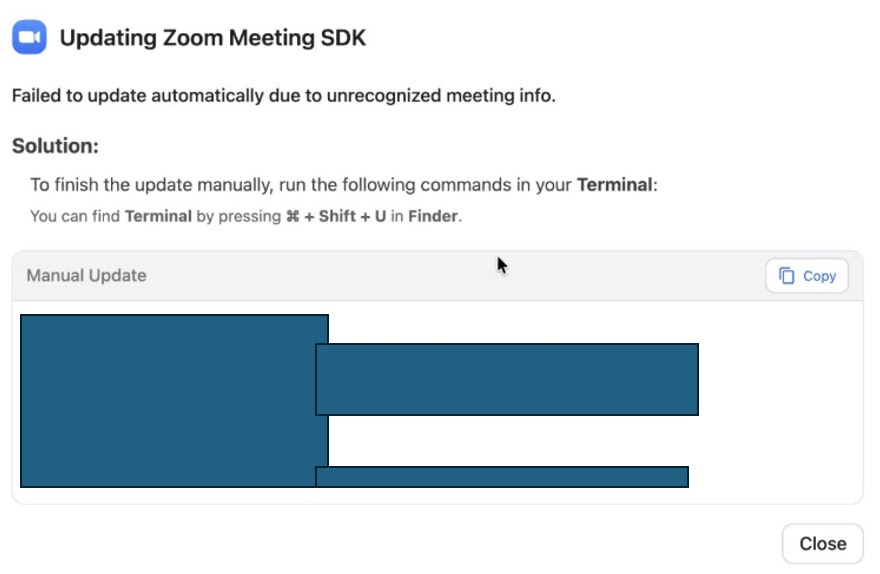
DangerousPassword campaign compromises social accounts first. Fake video calls show “audio errors” pushing malicious SDK installs. Contagious Interview offers dream developer jobs with infected code repos.
Both generated $37.5 million from January to mid-February 2026 alone. Corporate devices become ransomware vectors. One infected wallet drains entire teams.
Attack Campaigns Table
| Campaign | Method | Payout (2026) |
|---|---|---|
| DangerousPassword | Fake Zoom/Teams + SDK malware | $20M+ |
| Contagious Interview | Job lures + infected repos | $17.5M |
| Bybit Follow-ups | Exchange smart contract exploits | $1.46B (2025) |
Developers face highest risk now. Unsolicited collaborations carry malware. Enterprises must verify all remote contributors rigorously.
Social Engineering Tactics
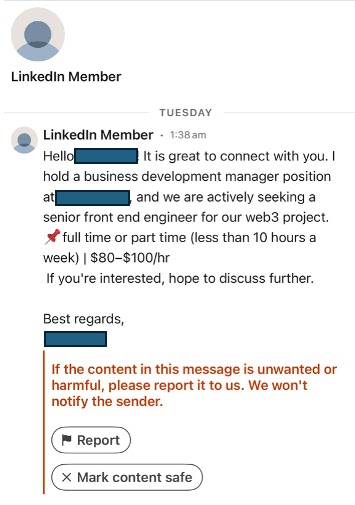
AI crafts LinkedIn profiles and messages that pass scrutiny. Victims reference “shared connections” or past projects convincingly.
Fake interviews request “skills tests” via GitHub. Repos hide keyloggers in npm dependencies or build scripts.
Video call traps push urgent “connection fixes” downloading trojanized tools. Seed phrases harvested within minutes.
Organizations lost millions to single careless clicks. Crypto firms report daily attempts. Verification gaps persist across teams.
Defense Measures
- Vet all unsolicited job offers and collaborations.
- Block command-line installs from unverified sources.
- Scan GitHub repos before cloning.
- Train developers on AI social engineering red flags.
- Monitor wallets for DPRK laundering patterns.
DPRK operations show no signs of stopping. Global crypto security demands new defenses beyond technical controls. Human vigilance remains the weakest link.
FAQ
$2 billion across multiple attacks. Bybit’s $1.46B was the largest single theft.
Laundered crypto through OTC desks and mixing services. Over $6B total since tracking began.
Social engineering via AI-crafted identities. Targets developers and contributors.
Fake video calls and job interviews delivering key-stealing malware.
Verify identities, scan repos, block unapproved installs. Elliptic report linked above.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages